GEOG 882
Lesson 1: Critical Thinking
Lesson 1.1 Overview
Every professor tells you they want you to think critically. Most of them don’t tell you how to do that. This lesson will teach you to how to use higher order and critical thinking skills.

What do you think?
How might geospatial analysts or various other types of professionals utilize critical thinking skills in the field? Why is this subject prominently placed at the beginning of this course?
Lesson Objectives
At the end of this lesson, you will be able to:
- Define the six elements in Bloom’s Taxonomy, the terms “Higher Order Thinking,” and “Critical Thinking;”
- Explain Facione’s six cognitive skills and the seven affective dispositions toward critical thinking;
- Explain the terms “Higher Order Thinking” and “Critical Thinking;"
- Explain why critical thinking is an essential skill for a citizen in a democratic United States.
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
Lesson 1.2 Checklist
Lesson 1 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to Lesson 1
- Work through Lesson 1 in this website.
- Read (the following are available in Canvas):
- Facione, Peter A. Critical Thinking: What it Is and Why it Counts. [2] Millbrae, CA. California Academic Press, 2020, pp. 1-28.
- View "What is Critical Thinking" video.
- View Facione's "The Importance of Critical Thinking Today" video.
- Take the Critical Thinking Self-Rating Ungraded assessment.
- Take the Lesson 1 - GRADED Quiz (#1).
* Students who register for this Penn State course gain access to assignments, all readings, and instructor feedback, and earn academic credit. Information about Penn State's Online Geospatial Education programs is available at the Geospatial Education Program Office [3].
Lesson 1.3 Critical Thinking: What is it?
Before we jump into the bulk of the lesson, I would like you to spend a few minutes reflecting on your own critical thinking skills. Please answer the reflection questions here and on the next two pages.
Reflection Opportunity 1
Lesson 1.4 Critical Thinking: Who cares? Why should you?
Reflection Opportunity 2
Remember your response here and compare it to the lesson material that follows.
Lesson 1.5 Critical Thinking Mindset Self-Rating
Measured Reasons LLC is an organization that specializes in “assessing reasoning, thinking strategically, and educating for critical thinking.” The following activity was adapted from their Critical Thinking Mindset Self-Rating Form. Reflect on your thinking over the last two days and answer the following questions. If you have described yourself honestly, this self-rating form can offer a rough estimate of what you think your overall disposition toward critical thinking has been in the past two days.
Reflection Opportunity 3
Please complete the following self-rating form.
If your total is 14 ("correct" answers) or above, you are rating your disposition toward critical thinking over the past two days as generally positive. Scores of 10 or lower indicate a self-rating that is averse or hostile toward critical thinking over the past two days. Scores between 10 and 14 show that you would rate yourself as displaying an ambivalent or mixed overall disposition toward critical thinking over the past two days.
Interpret results on this tool cautiously. At best this tool offers only a rough approximation with regard to a brief moment in time. Other tools are more refined, such as the California Critical Thinking Disposition Inventory, which gives results for each of the seven critical thinking habits of mind.
© 2009 Measured Reasons LLC [4], Hermosa Beach, CA. Used with permission.
Lesson 1.6 What is Critical Thinking Video
What is critical thinking? What is critical thinking not? Thinking critically can help you work methodically through problems in the workplace. It may help you sift through relevant information more efficiently and help you prioritize tasks. In your personal life it can help you decipher things like medical information to help you be a better consumer and advocate for yourself. Please view the video below about critical thinking.
Video: What is Critical Thinking (2:30)
Critical thinking is all about asking questions: the right questions questions that help you assess both the meaning and the significance of claims and arguments. Building these skills and applying them in your life makes it easier for you to assess evidence, evaluate arguments, and adapt your thinking so you stay switched-on and engaged in different situations. Critical thinking involves stepping back from a situation, to enable you to see all the angles before making judgments or taking decisions. It means identifying the key points, analyzing the sources of information, weighing up different types of evidence, just as a judge and jury would do in a court of law, and putting it all together into your own independent, thought-through point of view. One thing that it's very important to realize is a critical thinking isn't about being critical and it's about much more than just finding flaws in other people's claims. By itself that isn't enough to give you an edge. To be a true critical thinker means being creative reflective and adaptable- evaluating the evidence to decide for yourself what is accurate, what is relevant, and do I have sufficient information to take a decision on this topic. Thinking critically means taking a stand for yourself. It can be difficult not to be swayed by close family or friends' views on things or certain beliefs that just feel right but learning how to use these higher-order thinking skills can help you to feel much more confident in your own opinions and conclusions. Critical thinking is also about a sense of discovery and excitement- not only about learning but evaluating arguments to see how they stand up and filtering for yourself what resonates is right or wrong. By using these techniques you'll find yourself becoming a clearer, better thinker Macat: Learn better, think smarter, aim higher.
Lesson 1.7 Expert Consensus Statement
Peter A. Facione, an expert in the field, wrote a report that contains the following consensus statement regarding critical thinking (CT). A definition of critical thinking is contained within.
"We understand critical thinking to be purposeful, self-regulatory judgment which results in interpretation, analysis, evaluation, and inference, as well as explanation of the evidential, conceptual, methodological, criteriological, or contextual considerations upon which that judgment is based. CT is essential as a tool of inquiry. As such, CT is a liberating force in education and a powerful resource in one's personal and civic life. While not synonymous with good thinking, CT is a pervasive and self rectifying human phenomenon. The ideal critical thinker is habitually inquisitive, well-informed, trustful of reason, open minded, flexible, fair-minded in evaluation, honest in facing personal biases, prudent in making judgments, willing to reconsider, clear about issues, orderly in complex matters, diligent in seeking relevant information, reasonable in the selection of criteria, focused in inquiry, and persistent in seeking results which are as precise as the subject and the circumstances of inquiry permit. Thus, educating good critical thinkers means working toward this ideal. It combines developing CT skills with nurturing those dispositions which consistently yield useful insights and which are the basis of a rational and democratic society." -Dr. Peter A. Facione
Reference
Critical Thinking: A Statement of Expert Consensus for Purposes of Educational Assessment and Instruction. [5] Peter A. Facione, principle investigator, The California Academic Press, Millbrae, CA, 1990.
Lesson 1.8 Benjamin Bloom
Benjamin Bloom and his taxonomy
"Creativity follows mastery, so mastery of skills is the first priority for young talent." -Benjamin Bloom
Benjamin Bloom (1913-1999) was a highly influential psychologist and educator. Bloom's Taxonomy is a foundation of modern education theory.
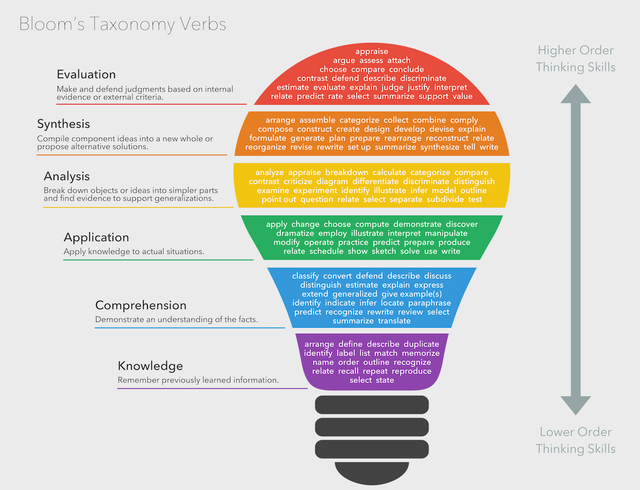
One way to foster critical thinking skills is to think about our own learning at a meta level. How do skills build upon one another? Benjamin Bloom developed a taxonomy that helps educators use shared vocabulary and/or verbs to align their teaching practices with outcomes and related assessments so that we can continually scaffold toward higher-order thinking.
For example, a very young child may think that the game of football is simply a mass of people jumping into a pile after an odd shaped ball. As they learn the subskills of catching and passing, they are demonstrating greater skill. Then later when a player has developed a playbook and can adapt to situations on the field, they are synthesizing their skills, while their coaches help them to evaluate their performance and up their skills for the next game. Where are you in your development with the material in this course? Where will you go next and what do you need to work on?
The video below provides some background about Bloom's taxonomy and its usefulness in an educational setting. Prior to viewing, reflect about a topic that you have considerable knowledge about and something that you have only a basic understanding or skill set with. Think about your own skill set within Bloom's taxonomy.
Video: Bloom's Taxonomy: Structuring the Learning Journey (4:47)
Bloom's Taxonomy is a toolbox that teachers or students can use to classify and organize learning objectives. Its most popular version is based on the cognitive domain and assumes that learning should be structured from easy to difficult in the following six steps: One – remember. Two – understand. Three – apply. Four – analyze. Five – evaluate. Six – create.
On the first level, we learn to remember. There is just rote memorization and recollection of facts without much understanding. For example, if we learn about lemons, we want to remember the name, shape, color, size and that they are sour. Once we memorize these essentially meaningless facts, we move to the second level of learning.
On level two, we learn to understand. We begin to decode information and learn that a lemon is yellow when it's ripe to eat and if we take a bite, that it's really super sour. We also understand that lemons love sunshine and that they contain lots of vitamin C, which is a great natural antioxidant that keeps us healthy. Now, as we really understand a lemon, we can work with it.
On the third level, we apply what we know. We've understood that while lemons are sour, they are also a great provider of vitamin C. To apply this knowledge in a meaningful way, we could boil a lemon into hot water and add some honey, then serve this hot lemon to our sick sister who's in need of treatment.
On the 4th level, we learn to analyze, this involves examining and breaking down information into components, determining how the parts relate to one another and finding evidence to support generalizations. We study the lemon flesh, examine the skin, and look at levels of vitamins. We conclude that we can eat everything inside, while the skin tastes bitter and contains traces of toxic pesticides, it ought not to be consumed.
Now, we are ready to evaluate. We analyze, critique and compare. To evaluate our lemon as a good source of vitamins, we compare it to other sources such as oranges and supplements. We look at the following properties: vitamin levels, affordability, taste and packaging waste. If we evaluate our thoughts critically and without bias, we learn where the lemons score high and where others score higher.
Now after we have learned, understood. Applied, analyzed and evaluated, we are ready to create. As we now really understand lemons, also in comparison to similar things, we can formulate a plan to create our own natural lemonade. It's now easy to come up with a cute shop design, a good name, and a good slogan: "natural, healthy, yummy".
Bloom's Taxonomy was first created in 1946 by American psychologist Benjamin Bloom. The revised version from 2001, as just presented, serves as the backbone of many teaching philosophies, in particular those that aim towards teaching specific skills. Each level usually comes with a clear learning objective that can be tested. Critics of the taxonomy often questioned the existence of a sequential hierarchical link between each level. What are your thoughts? Please share them in the comments below.
Millions of students from all around the globe have watched our Sprouts videos for better learning. Thousands of teachers play them in their classrooms to start projects. Volunteers on YouTube have translated them to over 25 languages. Our mission is to promote learning by doing in classrooms around the world. If you are a great explainer and a passionate teacher, and you want to help us develop outstanding content, contact us. To support our channel with a donation, visit Patreon dot com slash sprouts.
Lesson 1.9 Bloom's Taxonomy
Bloom's Taxonomy and related verbs
Bloom’s Taxonomy is a system for organizing levels of knowledge. It is a spectrum of sorts that begins with memorizing basic facts or vocabulary and builds from there when the learner practices and applies learned knowledge to eventually solve problems and to be able to evaluate systems or create something new to add to the topic.
| knowledge | comprehension | application | analysis | synthesis | evaluation |
|---|---|---|---|---|---|
| define identify describe label list name state match recognize select examine locate memorize quote recall reproduce tabulate tell copy discover duplicate enumerate listen observe omit read recite record repeat retell visualize |
explain describe interpret paraphrase summarize classify compare differentiate discuss distinguish extend predict associate contrast convert demonstrate estimate express identify indicate infer relate restate select translate ask cite discover generalize group illustrate judge observe order report represent research review rewrite show trace |
solve apply illustrate modify use calculate change choose demonstrate discover experiment relate show sketch complete construct dramatize interpret manipulate paint prepare teach act collect compute explain list operate practice simulate transfer write |
analyze compare classify contrast distinguish infer separate explain select categorize connect differentiate divide order prioritize survey calculate conclude correlate deduce devise diagram dissect estimate evaluate experiment focus illustrate organize outline plan question test |
design compose create plan combine formulate invent hypothesize substitute write compile construct develop generalize integrate modify organize prepare produce rearrange rewrite adapt anticipate arrange assemble choose collaborate facilitate imagine intervene make manage originate propose simulate solve support test validate |
reframe criticize evaluate order appraise judge support compare decide discriminate recommend summarize assess choose convince defend estimate grade measure predict rank score select test argue conclude consider critique debate distinguish editorialize justify persuade rate weigh |
In the educational realm, Bloom’s has been used to help teachers connect their content and students with objectives or desired outcomes. Modern interpretations of Bloom’s focus more on the act of learning by utilizing verbs that scaffold for higher levels of skill and knowledge, building upon one another, so that learners can develop from basic factual memorization to more elaborate concepts that incorporate these facts. The verbs also lend themselves to learning a continuum of procedures that graduate accordingly and can help a learner understand and reflect about their own capabilities.
Lesson 1.10 Foundational Skills: Knowledge, Comprehension, Application
Foundational Skills
"You must crawl before you can walk, and walk before you can run." -Unknown
What foundational subskills must we develop? In the field of Geospatial Information, what are the building blocks that form one’s basis of understanding and what kinds of actions do we need to demonstrate to experience growth and learn and demonstrate knowledge?
The foundational skills pictured above must be mastered before an individual can master higher order thinking skills in the future. This often involves the memorization of basic facts and behaviors related to the subject at hand. This brings us to you, the student, interacting with online content. As the adage says, “you get out of it what you put into it.” So having a broader sense of "where you are coming from and where you’re going” can be empowering as you manage your own educational experience. This sort of reflective practice helps you be aware of your own thought processes and development so that you are in greater control of your own destiny. This self-understanding can be defined as your own metacognitive knowledge. Having metacognitve knowledge also helps you in future roles when you are asked to contribute in a team environment or when you’re helping a newer colleague onboard into a new role in an organization.
Lesson 1.10a Knowledge
Knowledge
I sometimes hear some of my younger colleagues or students contending that rote memorization is an outmoded learning approach in our modern technological era where we have knowledge at our fingertips via a Google search on our phone. I strongly disagree with this.

Consider a child learning to read. The first thing they must master is memorization of the alphabet. Children learn (memorize) their ABC’s through repetition and song (did you learn to sing your ABC’s?). Being able to recite the alphabet, however, does not mean you comprehend that the letters represent sounds and have meaning. Learning to count is the formation of knowledge about numbers, their quantity, and numbers in sequence.
A learner at this stage in their development can be observed demonstrating:
- observation and recall of information
- knowledge of dates, events, places
- knowledge of major ideas
- mastery of subject matter
Verbs that demonstrate knowledge:
list, define, tell, describe, identify, show, label, collect, examine, tabulate, quote, name, who, when, where, etc.
Lesson 1.10b Comprehension
Comprehension
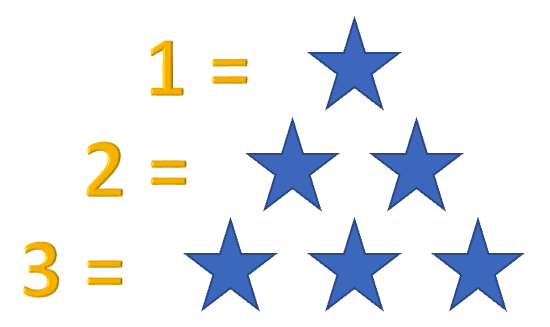
Consider our pupil once again. They have memorized their letters and numbers. They now need to understand that these letters and numbers have meaning. Letters have certain sounds. Numbers represent a numerical value such that one equals one star but three equals three stars and is more than one.
A learner at this stage in their development can be observed demonstrating the ability to:
- understand information
- grasp meaning
- translate knowledge into new context
- interpret facts, compare, contrast
- order, group, infer causes
- predict consequences
Verbs that demonstrate comprehension:
summarize, describe, interpret, contrast, predict, associate, distinguish, estimate, differentiate, discuss, extend
Lesson 1.10c Application
Application
Our student is progressing nicely. The next step is application or applying their knowledge and comprehension. As our pupil strings letters together into words and then sentences they are beginning the process of learning to write. As they take numbers and add, subtract, multiply, and divide them they are calculating new values. The next thing you know they are doing calculus and inventing artificial intelligence. Hopefully, having mastered these foundational skills, they will use their higher order thinking skills to make good decisions.
A learner at this stage in their development can be observed demonstrating their ability to:
- use information
- use methods, concepts, theories in new situations
- solve problems using required skills or knowledge
Verbs that demonstrate application:
apply, demonstrate, calculate, complete, illustrate, show, solve, examine, modify, relate, change, classify, experiment, discover
Lesson 1.10d Check on Learning Foundational Skills
Knowledge Check
These two pages offer a chance for you to apply what you've learned about Bloom's Foundational Skills. Consider some of the terms and verbs that will serve as building blocks as you become adept and fluent in thinking critically. Demonstrate your understanding of the levels for foundational skill development according to Bloom's Taxonomy.
Lesson 1.10e Check on Learning Foundational Skill Terms
Knowledge Check
Lesson 1.11 Higher Order Skills
Higher Order Skills of Bloom's Taxonomy
An analyst must understand how to gather data that can tell where and when an event like a forest fire takes place. They’ll need to understand how to use software to gather the data. But synthesizing the data with other geographical concepts gets them closer to understanding why something happened. The synthesizing process demonstrates a higher level of thinking and understanding about the topic at hand and can contribute to a larger dialogue about addressing future forest fires.
So when someone can combine some background in climatology, along with patterns of data, and maybe some practical knowledge about how governmental mechanisms function in the field- then we are getting closer to answering why something like a forest fire happens and how to adapt our behavior or response accordingly.
Lesson 1.11a Analysis
Analysis
Now that we’re moving on to the higher order thinking skills, I am going to use the Cold War and the Cuban Missile Crisis as an example of how these skills were used in a real life situation. I am pulling much of the information about this from the fascinating book by J.A. Nathan, Anatomy of the Cuban Missile Crisis.

Consider the photo above, in which a person is observing several aerial photos. To the untrained eye these may be just pretty pictures. The question is, do they have the training to actually “analyze” the imagery to determine: what they see, where it is, when it is, and perhaps how it got there?
Analysis is, simply stated, taking things apart or deconstructing them.
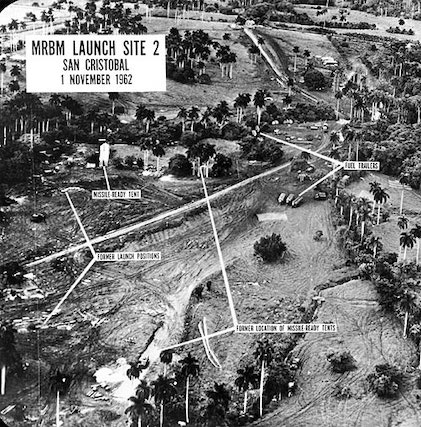
Let us go back to the Cuban Missile Crisis of 1961. US photo reconnaissance aircraft took photos (see above) of odd installations in Cuba that were newly installed. Image interpreters used their knowledge and comprehension of image interpretation keys including: density, concentration, pattern, spatial association, and Soviet aircraft, missile, and vehicle identification guides to analyze the images. They used change detection to determine that what they were seeing was new as it was not on previous images. The fact that the density, concentration, and pattern of objects were regular and symmetrical indicated they were most likely human engineered. The shapes of objects on the ground matched those of Soviet missile systems and support equipment.
A learner at this stage in their development can be observed demonstrating their ability to:
- see patterns
- organize parts
- recognize hidden meanings
- identify components
Verbs that demonstrate analysis:
analyze, separate, order, explain, connect, classify, arrange, divide, compare, select, explain, infer
References
Nathan, J.A. (2000). Anatomy of the Cuban Missile Crisis. New York: Bloomsbury Publishing PLC.
Lesson 1.11b Synthesis
Synthesis
For our Cold War image analysts looking at Cuba they clearly have something that appears to be newly installed and human engineered. As they look at the location and time of these new installations, it is clear they are in relatively remote and easily securable areas. They see a specific pattern or layout. Given knowledge of the US-Soviet-Cuban relations at the time, the analysts know that the USSR is hostile to the US, and that the USSR and Cuba are allies. This leads to a hypothesis that these new installations may be Soviet installations. Comparing imagery of various Soviet military sites leads to the conclusion that these sites may house Soviet offensive surface-to-surface missiles.
A learner at this stage in their development can be observed demonstrating their ability to:
- use old ideas to create new ones
- generalize from given facts
- relate knowledge from several areas
- predict, draw conclusions
Verbs that demonstrate synthesis:
combine, integrate, modify, rearrange, substitute, plan, create, design, invent, compose, formulate, prepare, generalize, rewrite
References
Nathan, J.A. (2000). Anatomy of the Cuban Missile Crisis. New York: Bloomsbury Publishing PLC.
Lesson 1.11c Evaluation
Evaluation
As our analysts evaluate the data available, they conclude these types of offensive missiles typically carry nuclear weapons. This means the Soviets have likely installed offensive nuclear weapons only 90 miles off the coast of the US capable of hitting Washington, D.C., and other targets on the Eastern Seaboard with less than ten minutes warning.
This information was critical to US President John F. Kennedy’s decision to blockade Cuba, and brought the world to the brink of nuclear war during the Cuban Missile Crisis.
It was aerial imagery and interpretation that later assured President Kennedy that the Soviets had kept their word and removed the weapons from Cuba, thus averting a catastrophic war.
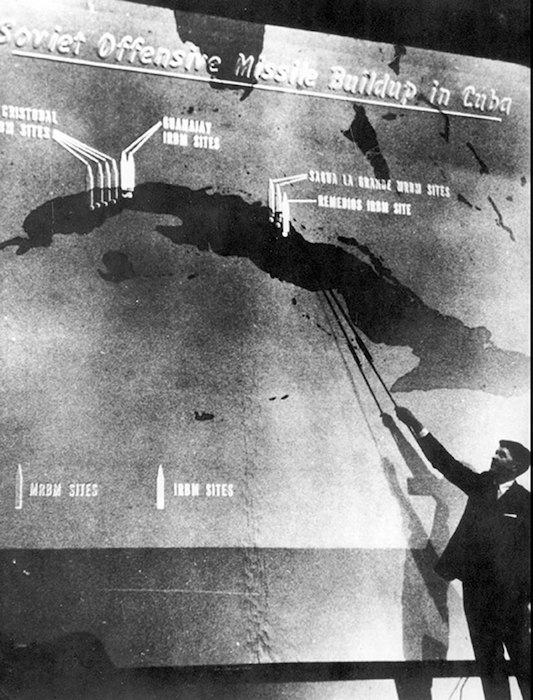
Note the air photos by themselves were just pictures. It took trained air photo interpreters using their foundational and higher order thinking skills and critical thinking to make the photos understandable and useful to policy makers and the public. The photos with associated interpretation were key evidence to make President Kennedy’s claims and actions credible.
A learner at this stage in their development can be observed demonstrating their ability to:
- compare and discriminate between ideas
- assess value of theories, presentations
- make choices based on reasoned argument
- verify value of evidence
- recognize subjectivity
Verbs that demonstrate evaluation:
assess, decide, rank, grade, test, measure, recommend, convince, select, judge, explain, discriminate, support, conclude, compare, summarize
References
Nathan, J.A. (2000). Anatomy of the Cuban Missile Crisis. New York: Bloomsbury Publishing PLC.
Lesson 1.12 Facione's Critical Thinking
Please make sure you read Facione's Critical Thinking: What It Is and Why It Counts [2]. You will be assessed on this reading, as well as the rest of the lesson's content in the Lesson 1 quiz. Additionally, please watch the video below about Facione's Critical Thinking.
Video: The Importance of Critical Thinking Today (2:57)
Welcome to the worldwide community of people advancing critical thinking. Please know that you have like-minded colleagues all over the world, in every profession, in every country, on every continent. My name is Peter Facione, and I am only one of the many people who believes that teaching ourselves and others how to reason well will benefit everyone with whom we share this planet. Critical thinking, as you know, is the human process of forming reflective well-reasoned judgments about what to believe or what to do. As such, it relies on our skills of analysis, interpretation, inference, evaluation, explanation, and, most importantly, self-reflection. But more, it is motivated by our desire to seek the truth courageously, to ask challenging questions, to be open-minded, to trust in the power of reason, and to make wise and thoughtful choices. The skills are important, and so is the consistent internal motivation to apply those skills to problem-solving and to decision-making in every part of our lives. Critical thinking is the process of using those skills with a positive motivation and mindset to form a reasoned judgment. I am sure you know the challenge of developing strong critical thinking. We can achieve this goal only by active engagement, not by memorization. Critical thinking must be practiced each day and in many different contexts – in our personal lives, in our learning, in our workplaces, and in our community activities. Critical thinking is a powerful force, it can liberate our minds from false ideas, it enables us to engage questions scientifically, it gives us the capacity to evaluate the credibility of the claims that we see in the media, and it demands that we follow reasons and evidence wherever they may lead. Critical thinking is skeptical without being cynical. How important is critical thinking today? It is the singularly most important outcome of all of education. It is our only and best hope to free ourselves from the tyranny of superstition, manipulation, and ignorance. Thank you for being a person who strives to free the minds of people everywhere. And thank you for empowering them to solve problems and make good decisions using strong critical thinking.
Reference
Facione, P. (2020). Critical Thinking: What It Is and Why It Counts [24].
Lesson 1.13 Cognitive Skills
The following six pages provide an example of higher order thinking in the context of a military operation by the 450th Movement Control Battalion in 2003 during Operation Iraqi Freedom.
As heard in Facione's video on the previous page, "Critical thinking is the human process of forming reflective well-reasoned judgments about what to believe or what to do. As such, it relies on our skills of analysis, interpretation, inference, evaluation, explanation, and, most importantly, self-reflection."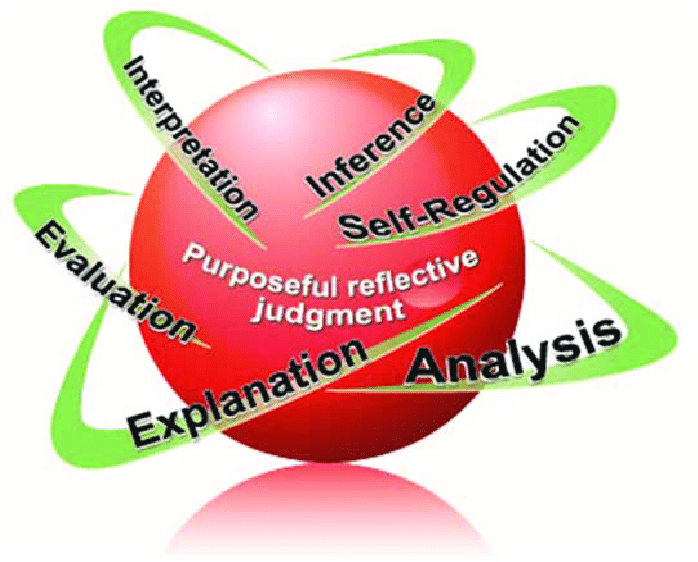
Cognitive Skills
- Interpretation
- Analysis
- Evaluation
- Inference
- Explanation
- Self-Regulation
Critical Spirit
The experts also said that a true critical thinker has a critical spirit. This is not to say that they are by any means negative or mean. It does mean that they have:
"a probing inquisitiveness, keenness of mind, a zealous dedication to reason, and a hunger or eagerness for reliable information."
Note
The following six pages provide an example of higher order thinking in the context of a military operation by the 450th Movement Control Battalion in 2003 during Operation Iraqi Freedom.
Lesson 1.13a Interpretation
Interpretation
Know the difference between a fairy tale and a war story? A fairy tale starts with “Once upon a time.” A war story starts with “And this is no kidding.” Let’s use a war story from Operation Iraqi Freedom. If you want the long version you can read US Army Transportation School Historian Gregg Adam’s version here: 450th Transportation Battalion (USAR) | U.S. Army Transportation Corps and Transportation School | Fort Gregg-Adams, Virginia [27].
The battalion commander (BC) of the 450th Movement Control Battalion (MCB) arrived at Talil Airbase Iraq two weeks into Operation Iraqi Freedom in 2003. He was greeted by BG Jack Stultz with a sneer and the query “where the hell have you been?” BG Stultz explained that theater transportation (especially the movement of critical meals ready to eat —MREs—also known by the troops as meals refusing to exit, and bottled water to support the warfighters) was not working. The general’s actual language was much more colorful. The general wanted the problem fixed yesterday.

Having just arrived, the BC had little situational understanding. In other words, he didn’t know what was going on. He thought he had better gain that situational understanding or he would be at best out of a job, and at worst—dead.
The first of the cognitive skills is interpretation. Interpretation means to comprehend and express the meaning or significance of a wide variety of experiences, situations, data, events, judgments, conventions, beliefs, rules procedures, or criteria. So, step one was to understand the mission and the commander’s desired effect. This was easy. Do not let US Vth Corps starve or die of thirst. The next step towards situational awareness was how to navigate the battlefield without getting killed. If you can’t move around the battlefield safely then you can’t gain information. The solution in unarmored HUMVEEs was to drive fast and bristle with weapons so no one dared mess with you. The next step was to get out on the road, to talk to everyone involved, observe the current operation and operating procedures, and develop that situational awareness of the process from the origin depots in Kuwait up to the destination at Balad Airbase (later Logistics Support Area Anaconda and later Joint Base Balad) 40km north of Baghdad. Gaining situational understanding was the interpretation phase.

The three sub-skills of interpretation are categorization, decoding significance, and clarifying meaning.
Lesson 1.13b Analysis
Analysis
The second cognitive skill is analysis. Analysis is to identify the intended and actual inferential relationships among statements, questions, concepts, descriptions, or other forms of representation intended to express belief, judgment, experiences, reasons, information, or opinions. In normal English it means to take things apart to understand how they work.

Having gained situational understanding via extensive visits to every transportation node, base, and unit, the BC and his staff were able to start deconstructing and charting many moving pieces of the theater distribution effort. Some parts of the operation seemed very clear cut. Other parts of the operation were hampered by differing perceptions, variable willingness, and in some cases outright lies, fraud, theft, and waste. Not everything was black and white—that was for sure. Oh—and don’t forget the enemy had a vote and they showed their displeasure with the US presence.

The three sub-skills of analysis are examining ideas, detecting arguments, and analyzing arguments.
Lesson 1.13c Evaluation
Evaluation
The BC and his movement controllers—having utilized interpretation and analysis —now turned to evaluation. Evaluation is to assess the credibility of statements or other representations which are accounts or descriptions of a person's perception, experience, situation, judgment, belief, or opinion; and to assess the logical strength of the actual or intended inferential relationships among statements, descriptions, questions or other forms of representation.

The BC and his movement controllers' evaluation determined that theater distribution did not suffer from one problem, but from a series of problems starting at the origin and perpetuating all the way through delivery at the destination. These problems fed into one another creating a cascading effect. There were no simple answers. To solve this challenge would require a fairly complex plan with buy-in from numerous stakeholders (some of whom were hostile to each other, and many of whom had their own agendas and priorities).
Lesson 1.13d Inference
Inference
The next cognitive skill is inference. Inference is to identify and secure elements needed to draw reasonable conclusions; to form conjectures and hypotheses; to consider relevant information and to deduce the consequences flowing from data, statements, principles, evidence, judgments, beliefs, opinions, concepts, descriptions, questions, or other forms of representation. Some might say inference is the ability to read between the lines.

The BC, his staff, and his unit commanders learned to read between the lines very quickly. As former President Ronald Reagan said when talking about arms control, “Trust but verify.” It was not that people often lied (although some did), but that people had bad information due to the fog of war, or their situational understanding was poor. Thus, while movement controllers analyzed the theater distribution system, they also had to probe deeper to read between the lines. This often meant observing operations from start to finish to get the real story, making friends with people to gain their trust and get their candid insights (versus the party line), and auditing and crunching data to see if the reports matched the actual performance. When people are tired, dirty, hungry and in danger you ought not be surprised that they make mistakes, sometimes cut corners, or even do unethical things to get by. Inference helps you get past that to see the real picture.
The three sub-skills of inference are querying evidence, conjecturing alternatives, and drawing conclusions.
Lesson 1.13e Explanation
Explanation
All the previous cognitive skills are useless if you can not explain yourself in a way that will achieve your desired effect and complete your mission. Explanation is to state the results of one's reasoning; to justify that reasoning in terms of the evidential, conceptual, methodological, criteriological, and contextual considerations upon which one's results were based; and to present one's reasoning in the form of cogent arguments.

The BC’s challenge was to clearly explain all the problems in the system in a clear and concise matter, and then to present a plan that would satisfy all the competing stakeholders. Obviously, the movement controllers had to develop a plan before they could present it. To do so they worked with their staff counterparts of the stakeholder units so the plan was feasible and acceptable to them. The BC worked with his counterparts to socialize the plan and ensure no one was going to look (too) bad. By the time it was time to explain the situation and the plan to the brass, the key players were on board. The plan was not perfect and the colonels and generals made a few changes, but you have to give a little to get a lot.
The sub-skills under explanation are stating results, justifying procedures, and presenting arguments.
Lesson 1.13f Self-Regulation
Self-Regulation
The highest level of critical thinking is recursive self-regulation. Recursive is a math term meaning to infinitely divide into itself. Self-Regulation is to self-consciously monitor one's cognitive activities, the elements used in those activities, and the results educed, particularly by applying skills in analysis and evaluation to one's own inferential judgments with a view toward questioning, confirming, validation, or correcting either one's reasoning or one's results.

Emergency medical personnel use critical thinking and a series of protocols to determine what is wrong with the patient and how to treat them. The final step in their approach is to re-assess the patient to see if their condition, signs, and symptoms have changed thus requiring a change in treatment.

The BC and the movement controllers sold their plan to the brass and implemented it in conjunction with all their partners and stakeholders. No matter how well you think you did, self-regulation is essential so you do not succumb to arrogance and hubris. Situations change, personnel and units change, the enemy has a vote, and sometimes stuff just happens. You must constantly reassess the situation and your understanding and when the situation and your understanding change—change your approach with it.
When the 450th MCB relocated to Kuwait to conduct theater movement control operations from Camp Arifjan, the BC saw an opportunity to have his very own railroad—and not a scale model one. The Iraqi Republican Railroad (IRR) was reestablishing scheduled operations and the BC wanted to run the Army’s part of it. You don’t get to be a BC by not being an empire builder and maybe having a little arrogant streak. At first, the IRR worked fairly well. Then the war transitioned to the insurgency phase and the situation changed. But despite the staff’s evaluation, analysis, and inference that the IRR was extremely vulnerable to insurgent attack, the BC was blinded by previous success. Fortunately for the BC, a major general with great wisdom took him aside and told him that while he was highly aggressive, he was also being a numbskull. The general forbade any further involvement with the IRR. Within a few weeks, the IRR ceased operating due to constant insurgent attacks. The BC dodged a bullet on that one and the mentorship of senior officers may have saved some of his soldiers' lives. You can figure out the moral of this story.
In conclusion, remember that if you can’t do it with style—then don’t do it.

The two sub-skills here are self-examination and self-correction.
Lesson 1.14 Seven Dispositions Toward Critical Thinking
What kind of a person would be apt to use their critical thinking skills? Take a moment and reflect about people you interact with on a daily basis, whom you consider to posess critical thinking skills. What adjectives or dispositions characterize behaviors that are demonstrated? How can you add to your own critical thinking skill set? Facione's research in conjunction with expert opinion have devised the seven dispositions toward critical thinking below.
Seven Dispositions Toward Critical Thinking
- Inquisitive
- Systematic
- Analytical
- Open-minded
- Judicious
- Truth seeking
- Confident in reasoning

Lesson 1.15 Ask yourself...
As you study, ask yourself
- What is the essential element of an argument or position?
- Is there a hidden agenda?
- What is the essential information to support the argument?
- Are the facts true or are they only assumptions?

- What information would weaken or refute the argument?
- Is this information available elsewhere, but not provided in the article?
- What information would significantly strengthen the argument?
- Is it available and is it false or true?
- What correlation or associations are suggested?
Lesson 1.16 The Critical Thinking Community
The Critical Thinking Community
Take a look at the website for "The Critical Thinking Community [32]." As you can see there is a lot of thought and effort that goes into this important topic. The Foundation for Critical Thinking (which hosts the aforementioned website) publishes a series of excellent small books such as:
- Paul, Richard and Linda Elder. (2003). The Thinker's Guide For Students On How to Study & Learn. Dillon Beach, CA: The Foundation for Critical Thinking.
- Paul, Richard and Linda Elder. (2004). The Thinker's Guide to The Nature and Functions of Critical & Creative Thinking. Dillon beach, CA: The Foundation for Critical Thinking, pp. 21-47.
These books are available as hard copies from the Penn State Libraries [33].
Lesson 1.17 Summary
Summary
In this lesson about the importance of critical thinking we covered:
- What is it?
- Who cares?
- Bloom’s Taxonomy
- Facione Reading Assignment
- Cognitive Skills
- Seven Affective Dispositions Toward Critical Thinking
Final Tasks
Your last challenge this week is to take Lesson 1 - GRADED Quiz (#1) on this week's material.
Deliverable: Lesson 1 - GRADED Quiz (#1)
Return to Lesson 1 in Canvas. Look for the Lesson 1 - GRADED Quiz (#1), where you will find the twenty-five question quiz on this week's readings. You will have unlimited time, and it is open book, but be forewarned. This is a tough quiz. To do well, you must have read and studied the readings.
Before you move on to Lesson 2, double-check the Lesson 1 Checklist [34] to make sure you have completed all the required activities for this lesson.
Looking Ahead
- Class Discussion & Thinking Critically about Geography Fundamentals.
2.2 Checklist
Lesson 02 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 02:
- Work through Lesson 02 in this website.
- Complete the Required Reading Assignments:
-
Facione, Peter A. Critical Thinking: What it Is and Why it Counts. [2] Millbrae, CA. California Academic Press, 2013, pp. 1-28.
- Read the following from The Geopolitics Reader 2nd edition (Required text):
- Toal's General Introduction addressing "Thinking Critically about Geopolitics"
(Pages 1-14) - Toal's Chapter 12: "Geopolitics and Discourse:..."
(Pages 94-102) - Toal's Introduction to Part One that discusses "Imperialist Geopolitics"
(Pages 17-33) - Toal's Introduction to Part Two that discusses "Cold War Geopolitics"
(Pages 59-74) - Toal's Introduction to Part Three on "Twenty First Century Geopolitics"
(Pages 119-135)
- Toal's General Introduction addressing "Thinking Critically about Geopolitics"
-
- Complete Mini Quizzes 1 through 5 each with a score of 100% in Canvas.
- Complete Lesson 02 - GRADED Quiz (#1).
Lesson 2: Geography Fundamentals
2.1 Overview
In this lesson, we are going to discuss definitions of geospatial intelligence, the scope of the subject, and examine why geography as a subject and a discipline is fundamental to the idea of geospatial intelligence. For those of you out there who are geospatial intelligence practitioners and professionals, the definition of geospatial intelligence may seem obvious, i.e., "geospatial intelligence is what my agency says it is, and the scope encompasses what we do..." However, as you will find out, different people and different agencies have different understandings of the definition and scope of the field.
It also may seem apparent to some that geography and geographical understanding and knowledge obviously underlay any field called "geospatial intelligence." However, it is quite possible that geospatial analysts have very little if any geographic knowledge and understanding. At Penn State, we think that is a real problem and one of the main reasons that a course entitled "Geographic Foundations of Geospatial Intelligence" is the foundation course of the Certificate in Geospatial Intelligence. So here is a fundamental concept of this course:
A reasonable knowledge of geography and associated geographical viewpoints is essential for all practitioners of geospatial intelligence no matter their agency, mission, focus, or specialization.
Lesson Objectives
At the end of this lesson, you will be able to:
- define Kant's three ways of ordering knowledge;
- define "Geography" and discuss the taxonomy of the word;
- define the terms Human Geography, Physical Geography, and Geographic Information Science and Technology (GIS&T); provide examples of each (sub-disciplines); discuss the relationship between the three;
- affirm or criticize, based on your own opinion and experience, the relevance of Human Geography to the field of Geospatial Intelligence;
- argue or defend how the definition of Geospatial Intelligence is socially contested and constructed; provide at least one organizational definition (e.g., NGAs) and argue or defend your own definition;
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
2.2 Checklist
Lesson 2 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 2:
- Work through Lesson 2 in this website.
- Read (the following are available in Canvas):
- Wikipedia article on Geography [35]
- Chapter 1 in: de Blij, Harm (2012). Why Geography Matters More than Ever. New York: Oxford University Press. (Located in Canvas)*
- Chapter 6, titled "Geospatial Intelligence and the Geospatial Revolution," in: Siedschlag, A., & Jerković, A. (Eds.). (2015). Cross-Disciplinary Perspectives on Homeland and Civil Security. Peter Lang Publishing. (Located in Canvas)*
- View both Episodes One and Five of the Geospatial Revolution Series (embedded on page 2.4).
- Participate in the "Geography Definitions" UNGRADED Discussion Forum.
- Participate in the "Human Geography Sub-discliplines" UNGRADED Discussion Forum.
- Participate in the "Lesson 2 - GRADED Discussion Forum (#1)".
- Take the Lesson 2 - GRADED Quiz (#2) (30 points).
* Students who register for this Penn State course gain access to assignments, all readings, and instructor feedback, and earn academic credit. Information about Penn State's Online Geospatial Education programs is available at the Geospatial Education Program Office [3].
2.3 Kant's Three Ways of Ordering Knowledge
Immanuel Kant [36] (1724-1804) was a famous German philosopher who lived in Königsberg in East Prussia (now Kaliningrad, Russia). He was one of the great thinkers of the European Enlightenment. Among his many ideas was his conception of how all knowledge might be organized. Kant said that there are three ways to organize all knowledge: the topical approach, the chronological approach, and the spatial approach.
- Topical Approach: A topical approach is to know everything about one thing. Thus, political science is a topical approach, as it involves everything about politics. Economics involves everything concerning financial economies, and biology concerns all knowledge about living things.
- Chronological Approach: A chronological approach looks at how things change over time. This is the approach of historians as they examine how the world has changed over time. Historians focus on what has happened in the past.
- Spatial Approach: A spatial approach looks at where things happen and why. This is the fundamental approach of geographers as they try to understand the world in terms of where things happen, why and how they happened there, and the interactions between phenomena in one place relative to phenomena in others.
In reality, few people limit themselves to using only one of these ways of ordering knowledge. Political Scientists may focus on the politics of certain eras or places. Historians may focus on the history of a particular country. And geographers, as we will see, are great synthesists who invariably use the spatial approach in conjunction with topical and chronological approaches. Yet, Kant's three ways of ordering knowledge demonstrates that the spatial approach of the discipline of geography makes geography one of the core scholarly disciplines.
Knowledge Check
2.4 What Is Geography?
People use the word "geography" all the time. And while it has many uses and meanings, most people would be at a loss to define what "geography" is. We are going to examine the definition and scope of geography, but before we do, I want to see how you might define "geography."
Discussion
Without any research or outside help, please return to Lesson 2 in Canvas and enter your short definition of "geography" in the Lesson 2 - Ungraded Geography Definitions Discussion Forum. If you see another definition you would like to comment on, feel free to post a reply.
Geography Defined
Let us take the word "geography" apart. The word geography can be broken into the two basic elements of "GEO" and "GRAPHY." Geo comes from the Greek word for earth (the word Gaea, also meaning earth, derives from the Greek as well). The "ography" part comes from the Greek word graphein, which is literally to write about something. The word "graph" derives from the same basis.
Thus, GEO + GRAPHY literally means "to write about the earth." We have commonly come to understand that the translation might also be taken to describe and map the Earth. The American Heritage Dictionary defines geography as "the study of the Earth and its features, inhabitants, and phenomena." I agree with the dictionary, but I like to tell my students that geography really is the study of how the world works in terms of the physical and human processes that occur every day.
So for me, Geography is really about how the world works. That is pretty good knowledge for a geospatial analyst to possess.
Breaking it Down
Understanding how the world works is a pretty tall order, so let us break down the study of geography into some manageable parts. At the most basic level, think of geography as a coin with two sides.
- HEADS: On one side, we have Physical Geography, or the study of the spatial distribution and attributes of naturally occurring phenomena.
- TAILS: On the other side, we have Human Geography, or the study of the spatial distribution and attributes of human-induced/engineered phenomena.
Physical geography looks at the natural processes that make the surface of the Earth the way it is. Physical geography includes the three major subdisciplines of Geomorphology, Meteorology, and Climatology.
Geomorphology is the study of landforms and landform processes. Geomorphologists want to know:
- What are the different landforms?
- Where are the different landforms?
- Why are they where they are?
- How do they form?
- What will happen to them over time?
Meteorology is the study of atmospheric weather processes. Meteorologists want to understand:
- What are the different atmospheric processes that create our weather?
- Where do these weather phenomena occur?
- How and why does the planetary weather system work the way it does?
- What will happen with the weather in the future? (This will allow them to forecast the weather.)
Climatology is the study of climate, which is basically the long-term pattern of temperature and precipitation. Climatology, like meteorology, is a branch of the interdisciplinary field of Atmospheric Science. Climatologists seek to understand:
- the different climate types found on Earth;
- the processes that cause these different climate types to occur in specific places (i.e. why are there different climate types);
- the places where these climates occur;
- how and why climates change over time; and
- what will happen to the earth's climate in the future so they can forecast the effects of climate change.
Human geography looks at the human activities that make the surface of the earth the way it is. Human geography includes numerous subdisciplines, some of which are:
- population geography
- cultural geography
- economic geography
- political geography
- and many others
Human geography is essentially synthesizing a spatial perspective with one of the topical disciplines to come up with new knowledge and a new perspective to understand how the world works.
Discussion
Can you think of some other human geography subdisciplines by combining a topical approach with a spatial perspective? Please return to Lesson 2 in Canvas and enter your list of other human geography subdisciplines in the Lesson 2 - Ungraded Human Geography Subdisciplines Discussion Forum. Feel free to post comments to other lists you see in the discussion forum.
Geographic Techniques
The world is fortunate that geographers through the ages have developed a set of spatial tools to help us understand how the world works. These tools are often referred to as the geographic techniques and they include the subdisciplines of:
- Cartography: The art and science of making maps and the oldest of the geographic techniques;
- Remote Sensing: The art and science of obtaining information about the earth by study from afar;
- Geographic Information Systems: A GIS is a computer-based system that collects, stores, analyzes, and displays spatial information to solve problems; and
- Global Positioning Systems: The use of a system of satellites, ground stations, and receivers to obtain precise locational information of phenomena on the earth.
Geospatial intelligence relies heavily on the geographic techniques (collectively known as Geographic Information Science and Techniques (GIS&T or GIScience) for the collection, analysis, and communication of results. Your other coursework will involve very detailed explorations and applications of the geographic techniques.
Knowledge Check
Penn State Public Broadcasting has produced an amazing series of webisodes on the "Geospatial Revolution."
Please take the time to view Episode One of the Geospatial Revolution Series (13:45 running time) and think about how the revolution applies to this lesson.
Video: Geospatial Revolution / Episode One (13:44)
Welcome to the geospatial revolution.
Capt. Arturo Derryberry, U.S. Marian Corps: In a world where everybody's texting, geospatial technology is critical to understanding what's happening at a particular location.
Mark Brender, VP Communications, GEOEYE: It's the speed of the Internet. It's the capability of remote sensing satellites. It's software like Google Earth. Taken all together, you have an explosion in the way we view the Earth.
Text on screen: It starts with MAPS that show where everything is...
Walter Scott, Founder, Digitalglobe: Everybody's somewhere, everything's someplace, and a map is a way of organizing all of that information.
Text on screen: Made by REMOTE SENSORS from everywhere...
David Cowen: Professor Emeritus, University of South Carolina: It's information from aircraft, from satellites. It can be a collection of information from a tower that you've set up.
Text on screen: and GPS that tells you where you are now...
Kass Green, President, KGA Geospatial:We've been using maps for hundreds and hundreds of years to know where we are. Now, that nice lady tells me which way to turn.
GPS voice: Turn right, then turn left.
Text on screen: with INFORMATION that tells you what's there...
Adena Schutzberg, President, ABS Consulting Group: Virtually all of the information that you're sharing with anybody these days has some kind of geospatial tag on it.
Text on screen: from PEOPLE everywhere communicating with everyone...
Patrich Meier, Director, Crisis Mapping, Ushidi: It's really the human element. There's basically this entire information ecosystem that we have access to now.
Text on screen: inside MOBILE devices that put the world... in the palm of YOUR hand.
Joe Fancica, Editor-in-Cheif, Directions Media: I can receive information. I can transmit information. I can broadcast my location. And that is revolutionary.
Jan Van Sickle, Geomatic Engineer: It's amazing. It's cutting-edge. It's--well, changing the world.How We Get There
GPS voice: In 1/10 mile, turn right at stop sign.
David DiBiase, Dept. of Geography, Penn State: Some people will call this a GPS. It's not. It's a GPS receiver. It is, I think it's fair to say, a miracle of science and technology. It's able to collect signals from global positioning satellites far up in space.
Adena Schutzberg: Each one of them is, every moment of every day, saying, "This is the location that I'm at in orbit around the Earth." If you know where you are with respect to three satellite points, you can use mathematics to determine where you must be on the face of the Earth.
David DiBiase: There are millions of coordinates encoded in this box.
GPS voice: Recalculating
David DiBiase: And it can take those coordinates and render a map on the screen for you.
GPS voice: Turn left on Whitehall Road. Then turn left in 0.3 miles.
David DiBiase: Where do all those coordinates come from? Where do those streets come from? Lots and lots of people driving special cars continuously up and down every single road and digitizing those roads into a database that then can be downloaded into this little box.
[electronic beep]
How We Got HERE
Michael Jones, Chief Technologist, Google Earth: There's nothing new about mapping. You can imagine without being able to talk, somebody showing where you're going, and draw a line showing where the river is, and an X where they are now, and an X where they're gonna go.
Mark Brender, VP Communications, Geoeye: Viewing the Earth has really been based on technology. The Babylonians etched the lay of the land on clay tablets in 2300 B.C. And then in the 15th century, with the advent of printing, they started making maps using wooden blocks.
David DiBiase: Surveyors would map by making measurements in front of them to a reference point and then back behind to the reference point they had just passed. That information had to be transcribed into a map.
David Cowen: From in the air, it's as if we sent out thousands of surveyors all at once. Remotely sensed data provides highly accurate measurements of the Earth and the features upon it.
[rocket rumbling]
Gen. C. Robert Kehler, Commander, USAF Space Command: We rely on satellites for pictures of the Earth, for communications, for navigation, for weather. Geospatial technology has become woven throughout the fabric of how we live.
Jack Dangermond, President, ESRI: About 50 years ago, people came along and started building on big old mainframes geographic information systems which would integrate on a map information about culture, about population, about demographics, about physical environment. GIS allows us to bring it all together.
Jan Van Sickle: I used the first commercial GPS receiver. Took two men to carry it. Our antenna was a meter-square piece of aluminum. We had to have a generator for it. Massive batteries!
Tim Trainor, Cheif, Geograph Division, U.S. Census: The census bureau in the United States needed to capture all of the line work for roads, railroads, hydrography, and then boundaries. That formed the basis of the first TIGER files in the late 1980s in support of the 1990 census. Tiger was an impetus to technological developments like MapQuest, Yahoo, followed by Google.
Text on screen: TIGER.Topologically Integrated Geographic Encoding and Referencing
Matt O'Connell, CEO, Geoeye: Google Earth introduced people to the coolness of place. "I am here. Where's the nearest Starbucks?" Or, "Where's the nearest hospital?"
Chris Pendelton, Technical Evangelist, Bing Maps: Now we're all carrying around GPS. We've got really rich interfaces that allow us to do things that we would only imagine previously.
Michael Jones: On a mobile device, you are the center of the map, and the city is around you, not you see a city and then look for yourself on the map. It's putting you in the map.
[electronic tone]
[horn honks]
[phone rings]
Adena Schutzberg: Say you find yourself in a location that you don't know very well. You might want to find a place to have dinner. Well, what places are around? And which places have other people rated very highly? Maybe you want a particular kind of food within a 15-minute walk.
David Cowen: I've got not only a restaurant, but I've got the map. I can find the reviews of it. I can find out what the menu is.
Chris Pendelton: We're moving away from me having to actively search for something, to now search is telling me what I should check out that might be interesting to me. These are the things where location and search start to come together.
Why We Need It
Joe Fancica: We're becoming individual sensors. We're creating this huge sensor network of people holding these mobile devices. And that information is two-way.
[electronic beeping]
David Cowen: It's not just passive collection, listen to your GPS technology, tell you how to get to some place. You're gonna say, "Wait a minute. "I see a problem. "I want to report that problem." "I want to see that someone's going to respond to that."
Jean Philippe Frantz, Carrefour, Haiti: We were playing basketball. We see, like, the ground keep on moving. I see a lot of people, some of them dying, like the ceiling, like, killed them.
Jean-Robert Durocher, Entrepreneur, Cambridge, Massachusetts: I have both extended family members and close family members who live in Haiti. And the first reaction was more, like, surreal."Is this really happening?"
Capt. Arturo Derryberry: We needed to know where we could go in. And so, we used geospatial technology to prepare the area with information before we even got there.
Craig Clarke: Approximately 2/3 of the cell towers stayed active. And aid workers and Haitian nationals were posting information saying that they needed help.
Patrick Meier: I was watching CNN and immediately called our USHAHIDI tech lead in Atlanta. I told him that we really need to move and set up an USHAHIDI platform for Haiti.
Jaroslav Valuch, Field Representative, USHAHIDI: USHAHIDI is an open-source platform for crowd-sourcing crisis information. Basically, that means you are following local media, Twitter, Facebook, text messages, any sort of information you can get. Once you aggregate this information, you map it, you have a real-time picture of the actual situation on the ground. This information can be used by rescue workers or anyone.
Patrick Meier: With an USHAHIDI platform, you can decide what kind of map you want to use. OpenStreetMap uses crowd-sourcing to do street mapping. And within a few days, OpenStreetMap had the most detailed map of Haiti that was available.
Kate Chapman, President, Openstreetmap, USA: There were maps of Haiti before the earthquake, but they just weren't up-to-date anymore. So people started using donated satellite imagery to trace in OpenStreetMap collapsed buildings, clinics, hospitals.
Patrick Meier: Within a week or so, we had trained over 100 individuals at Tufts University to map the incidents and the alerts. And then a text number, 4636, was set up for reporting. But these text messages were all going to be in Creole. So we started getting as many Creole-speaking volunteers as possible.
Jean-Robert Durocher: I found out about the 4636 effort through a friend of mine. So I got online, started getting involved, basically staying up late after putting the kids to bed, try to translate as many text messages as I could.
Various unknown speakers within a group: Our top priority is Port-au-Prince. It's good. It's good, good translations.
Jean-Robert Durocher: There was this energy.
Unknown speakers: Today's SMS.
Jean-Robert Durocher: People from basically all over the world creating this sort of, like, support system over the internet.
Craig Clarke: A soccer stadium was serving as a camp for displaced persons. But we didn't know it was there. Through USHAHIDI's mapping ability, we knew that that would be a location to take aid. We wouldn't have seen it without them.
Capt. Arturo Derryberry: USHAHIDI alerted the world that if you've got needs in Haiti, or you're trapped in a building, or you're out of food, or you're injured, and you need help, that you can alert us.
Text on screen: More than 2,000 volunteers and 20 organizations from 49 countries participated in the Haiti crisis mapping effort.
Craig Clarke:Whether you are that person in Des Moines, Iowa, who's reading Twitter or Facebook, or you're a Haitian on the ground, with mobile technology and open-sourcing of information, you're suddenly empowered.
Unknown speaker:I work from California.
Jean-Robert Durocher:Being able to stay online translating those text messages, and you know that that information will be forwarded directly to a specific aid organization. That made it feel like, almost, I was on the ground helping.
Jack Dangermond:A map is worth a million words. Maps communicate with everybody. That's powerful. You know, you can make a difference. You can look at relationships and patterns and processes and models, help save the world.
Joe Fancica: I don't think we can project 50 years out, but given what we're seeing today, it's just a fantastic explosion of location technology. And location-based data. And now we have the devices to read it and capture it and visualize it. And that's something that's really helping the geospatial revolution truly explode.
Walter Scott: Revolutions rarely end up the way they started. That's almost the definition of a revolution.
Video: Geospatial Revolution / Episode Five (21:28)
Mapping the Pandemic (somber music) (suspenseful music) Al Powered Early Warning (bell ringing) - [Peter Coyote] 1854, London. In the wake of a cholera epidemic, Dr. John Snow placed cholera deaths on a grid to confirm the source of the outbreak as water from a single pump. Geography is central to fighting disease. New Year's Eve 2019, 166 years later, a global infectious disease surveillance system detects an unidentified respiratory illness emerging in Central China. The threat was real. And the platform issued the warning nine days before the official WHO report. The system was built by an interdisciplinary team at BlueDot, a small startup out of Toronto; using artificial intelligence and machine learning to scour the internet for clues of emerging infectious disease. - When we're talking about the problem of infectious diseases, we need a diverse set of data. We can't just be tracking a microbe, we need to understand how people are moving across the planet, we need to understand in some situations climate conditions, animal populations, health systems. And so when we think about where geospatial technologies are going, there's this massive increase in production of data that are all associated with a place and time. And geospatial technologies now allow us to wield those data to integrate them and to make sense from massive amounts of data to derive an actionable insight and to do this in real time. - [Peter Coyote] In an unequal world where official reports of outbreaks are not always timely, epidemiology's pressing need is to develop surveillance capacity, to sift through the layers of data that can predict an outbreak. - So we've been using machine learning and natural language processing to stitch together a global panoramic view of infectious disease threats that are appearing around the world. And so our algorithms are scanning through vast amounts of online sources, open source data, in 65 different languages and looking for these early signals that maybe there's an unusual cluster of a disease happening. It might be a disease that we know of, or it might just be a syndrome in the way that we in fact picked up an early signal that there was an unusual cluster of pneumonia cases in a city called Wuhan. [Peter Coyote] These global tracking systems, mine, process and filter myriad information sources to essentially create a living breathing map of risk information. And to build it takes a host of experts ranging from public health to data science to veterinary medicine. - This is inherently a complex problem, and it requires a diverse set of skills and perspectives. - [Peter Coyote] This emerging field of digital epidemiology and disease surveillance is a mashup of computer science, statistics and big data mapping. Algorithms are trained to understand disease terms and to process whether an alert is relevant. And while detection is the first concern, dispersion of the pathogen is the second. - [Kamran Khan] Human population, mobility and movements are critical to understanding how diseases spread. So humans in essence have become the vectors that are transporting diseases inadvertently across the planet. So within the span of about a second or two, we had automatically now assessed how Wuhan was connected to the rest of the planet and which places were in the path. If this thing were to spread out further, where should we be looking for it next? - [Peter Coyote] The only requirement for the spread of COVID-19 is proximity and movement. Transported undetected by their human hosts, the virus crossed borders worldwide. (suspenseful music) Tracking a Pandemic in Real Time At Johns Hopkins University in Baltimore, a small team led by Dr. Lauren Gardner had been watching the outbreak with deepening concern. - [Lauren Gardner] I saw this as a really unique opportunity to start building out a dataset on an emerging infectious disease in real time. - Dr. Gardner and I, we had a very small group team meeting. She suggested to me why don't you create a dashboard for the coronavirus because she knew I was from China and very anxious to know what's the situation in China and know my relatives, my friends and how they were doing. - [Lauren Gardner] My student Ensheng Dong and I were basically the two that started this and he's a total wiz with dashboard development. - After I talk with Dr. Gardner, I went back to the office. I spent eight to nine hours and came up with the first version of the dashboard. - [Lauren Gardner] And so we built the dashboard that night and then the next day shared it publicly. - The dashboard went viral after that. - I don't know how many views the Hopkins dashboard got and continues get, but I'm sure it's off the charts. - They are in fact, the creators of the most viral map-based application in the history of the world. - Four or five billion maps are generated off that website every day. Sometimes it was as high as 10 and 12 billion on a day. That meant that people were looking at it and re-looking at it and seeing the trends. - [Gardner] We massively underestimated the interest of the general public in following the progression of this outbreak. [Nita Bharti] For a lot of people being able to see disease data in a spatial format meaning an interactive map was a really important way for them to understand what was happening and also for them to assess what their immediate risk was. - This was a huge day of awakening for the world because they began to see the power of geospatial visualization in their own lives. - [Peter Coyote] The Johns Hopkins dashboard quickly became the authoritative source and public health officials rushed to create their own. - It was within a week that we started to see similar dashboards coming out and Hong Kong had a dashboard and Thailand had a dashboard and Korea had a dashboard. - And I remember the first time I saw it thinking, I want that including the map and the visualization of all the countries and all the cases in the red dots, I want that on our website. - Anybody who felt comfortable going into GitHub, could go pull those data, could pull the actual tables and the numeric data and make their own maps or do their own analysis. It was very transparent, it was updated regularly and it was easy to use. - [Este Geraghty] Never before have we really had this opportunity to watch real time data update. And that is the ideal for disease surveillance. - And this is why visualization of that work and the work that we've been doing on the ground is so critical because we need to know where things are happening so we can address them. We can focus our attention, we can accentuate our efforts and ultimately we can drive resources to those very communities that are seeing the disproportionate impact of this horrific pandemic. (suspenseful music) - [Peter Coyote] Days before the WHO called the crisis a pandemic, the Johns Hopkins map showed it to be true. The small clusters of red dots had grown larger and crossed borders. But dark spaces on the map marked where public health data had been withheld. One of these was Iran. In late February 2020, Iran's Ministry of Health reported 12 deaths, but posts on social media painted a darker picture. A team at Maxar Technologies used their human geography dataset and crowdsourcing platform to investigate the rumors, then confirmed them with high resolution satellite imagery. - The largest cemetery in Iran in Qom, what we were seeing from space... mass graves being dug. And so we saw trenches that were upwards of a hundred yards long. We saw large piles of lime to counter the odor and the decay. - [Peter Coyote] The satellite pictures suggested the number of dead was significantly higher than the official figure. - That then allowed us to be able to support in this case The Washington Post, to be able to publish an article to bring transparency. And I think having that type of shared experience where we all were able to see the impact of that, I think it helps drive behavior. (lively instrumental music) The goal is to understand what is normal and when is there a variance. This proliferation of sensors, whether those sensors are on the ground, through social media or passive sensors that are collecting data. If we can derive patterns from that, that then can help inform how we apply assets in space to be able to collect imagery and then extract the insights from that imagery in short timelines to be able to drive decision-making. - [Peter Coyote] From space, the signs of COVID could be seen everywhere. Passenger planes grounded, new hospitals built within months, St. Peter's Square on Palm Sunday empty. In Mecca, the crowds that visit the Kabaa, Islam's holiest shrine, told the story. - Going from densely populated cultural iconic location of interest to no one there and then the leaders at that location established mechanisms to create social distancing kind of a stark change in behavior. (suspenseful music) Mass Gathering Footprints - [Peter Coyote] On February 29th, 2020, the Trump administration announced new travel restrictions on Iran. The same day the US recorded its first death from COVID-19. Colleges canceled student travel programs, but many students had already boarded planes for spring break. - You see on news that spring breakers are still flocking to the beach in Fort Lauderdale. We thought, man, this is really reckless to have all of these people go from universities to one location, congregate who don't really feel the symptoms of COVID get together and then return back home and go back to their schools. We said, let's see if we can show that story in our mapping platform". - [Peter Coyote] To bring awareness to the situation, Tectonix, a data analytics and visualization company, planned to isolate and track cell phone users crowding onto a single beach using anonymized location data. - [Rob Gresham] As we zoom in towards the Fort Lauderdale Beach, we are saying "filter the geo-fence down to what you're actually seeing on the map". And then what you end up seeing next is an even more precise filter where we start drawing a lasso around devices on the beach. And you could just see the congregation of many many people. - [Peter Coyote] Once lassoed by the geo-fence, every beachgoer's cell phone location data could be tracked by Tectonix platform. [Rob Gresham] And then when we zoomed out in the days following, you could see these students returning to essentially all over the country. - [Peter Coyote] The team sent out a video on social media. - The next morning, checked Twitter and saw that we had millions of views. And we just said, "what the heck have we gotten ourselves into?" - [Peter Coyote] On March 15th all public beaches in Fort Lauderdale were closed. (lively instrumental music) By August, US COVID deaths had reached 160,000. Warnings about mass gatherings and social distancing largely went unheeded. And in South Dakota, the 2020 Sturgis Motorcycle Rally opened as scheduled, 250,000 attended. The Tectonix crew lassoed devices in all the hotspots and then tracked them back to their home states. - Sturgis was interesting because it happened to be a lot of middle-aged or older people. But when people flocked to South Dakota, it actually set off a series of events where South Dakota briefly was the epicenter for COVID spread globally for several weeks. - [Peter Coyote] In rural America, meat packing plants reached a crisis situation with COVID cases. Tectonix isolated an Indiana plant for a full month, the resulting footprint was huge. Devices traveled to 48 states and into Canada. - For whatever reason, the meat packing industry was very hard hit by COVID. And now I think we've seen a lot of the working conditions and how close people were on conveyor belts and that sort of thing. - [Peter Coyote] These demonstrations proved in case after case, how desperately interventions were needed. That responsibility fell to public health officials who found themselves facing an angry backlash against emergency measures as they prepared to roll out the largest vaccination campaign in American history. (suspenseful music) Engaging the Virus - Geospatial technology has been a huge asset for epidemiology... for understanding how outbreaks are moving through populations and understanding how we can get response to those populations. - Now you've got all this data, how are you then determining what you do there? How do you accentuate your communication messages? What are you pulling back? If it's a zero sum game you don't have enough resources, you can only do one or the other; you're gonna focus on where you have the most risk. The most proportion of tests that are coming back positive, the most hospitalizations, what's happening with deaths in that area. But then it's the next phase of it which is now about adding in the protective measures. Where are your PPEs? Where are the masks going? What are the data showing in terms of mobility? Are people wearing masks? Are they moving around? Are they not moving around? Are they staying close to their home? This is all geospatial technology and mapping that allows you to visualize. And then on top of that the last protective measure is on vaccines. - To monitor our vaccine inventory, to understand the population phases and how many people in each phase need to be vaccinated. To look at the vaccination venues. - Now you layer socioeconomic information, housing, transportation issues, challenges with social vulnerability index or what we call them SVI. Add in where you have increase in cases, hospitalizations, deaths and vaccine knowledge. And now you have a geospatial ecosystem that you can not just share internally, but share with your folks on the ground but also your policy makers, your elected officials, with the community who are looking at all this information and saying, "Gosh, I wanna protect my own family!" (suspenseful music) Wearable Technology Detection - [Peter Coyote] As vaccinations take hold across the United States, COVID-19 cases and deaths have dropped to their lowest levels in nearly a year. But even as the outlook improves, researchers are testing new methods to stop the next pandemic. A team at Scripps Research in San Diego has proposed using wearable technology to monitor a population for early signs of an outbreak. (heart beating) - So we're launching DETECT and we're really excited about this. Because this is a way to track from a smartwatch, a person's heart rate and to know well before people have fever and symptoms, whether there's a cluster of abnormalities that's happening. - [Peter Coyote] Roughly a hundred million Americans own a wearable health tracker. And this study only needs to gather physiological data from one or two percent of them to set up an effective public health surveillance system. [Eric Topol] We have a mobile app where people will be asked if they wanna join a research effort to track their health, their resting heart rate through their smartwatch. - [Peter Coyote] Once a person volunteers, readings from their device will be monitored continuously through the app. And they'll be asked to enter their vaccination dates and report symptoms. - [Eric Topol] In the setting of this COVID-19, it gives us a handle on things like heart rate, which we know is a great antecedent abnormality before people get sick. So by tracking people at scale, we'll be able to see an outbreak in a way that previously has not been obtainable. - [Peter Coyote] This new twist on telemedicine, the ability to perform medical interactions without face-to-face contact is especially important in the midst of a pandemic; when we simply can't test enough people in time to know what the virus is doing. - It's real time, it's continuous, it's scalable. And so we're really keen on this added ability to be able to detect an emerging problem in any part of the geography of the United States. (somber music) [Peter Coyote] The global pandemic has caused incredible pain and hardship. We have suffered great loss and isolation, and we have not seen the last of COVID-19. The reality is that the world has entered a pandemic era in which new pathogens continue to emerge and spread within populations. And more than ever, geography is central to fighting disease. - [Kamran Khan] COVID-19 I think has been an awakening and we can all agree none of us wanna be back here again soon. - We certainly have hope with the vaccine, but concern yet about the variants. We have a number of lessons learned, but it's unknown how well we'll do with applying those lessons. - I'm trying to think about it as an opportunity to make changes and to think about the world in different ways. What can we be doing? What kind of information can we be collecting? The limit to this technology and the limit to geography is really our imagination. - COVID-19... what it has done, it's allowed us to see a purpose that's bigger than ourselves and I think deep down, probably every one of us wants to feel like we're part of something that's just bigger than us. - Geospatial community stood up and I'm so proud of them. Their work has literally saved lives and made things understandable. It's a great day for the application of science and technology to this great challenge that's facing the whole world. (light instrumental music changing to somber music)
The Relationship of Physical Geography to Human Geography
In an Introduction to Geography class (usually for freshmen and sophomores), a fellow instructor likes to stress the point that physical and human geography are completely separate disciplines and that there can be NO mixing between the two. In fact, he makes a big deal that students must write this down, and put stars by it in their notes as this important point will most certainly be on the test. He then stops and lets them think about this statement as they dutifully write it down.
Now, you might be thinking that this contention that physical and human geography are completely separate and can never be mixed seems nonsensical—and you would be correct. Eventually, a few of the students start to grin and perhaps a bold one might challenge the instructor (not very often though).
The instructor then gets to point out to the students the fallacy of such a contention and makes the point that physical and human geography, like the sides of a coin, are absolutely inseparable. We know that physical systems can have enormous impacts on human systems (ask the survivors of Hurricane Ida). We also know that human impacts on the environment have been great. As humans have always modified the surface of the planet to scratch out a living or to build great civilizations (western Europe had a climax vegetation of forest—consider the landscape there now—forests are rare, protected, and highly valued).
I think that the geographic subdiscipline of Environmental Geography occupies the space in the center of the coin, gluing human and physical geography together. A problem in many modern geography programs is that students specialize in either human or physical geography with inadequate knowledge of the other side of the coin. The even greater problem is for students who specialize in the geographic techniques (whom I affectionately call "Techno-Geeks") and lack the necessary background in human and physical geography.
Here is the fundamental contention that justifies this whole course:
All the geospatial technology in the world can tell you what is happening where and when. It may even tell you something about how it is happening. The technology, however, will NOT tell you why it is happening. To understand the why, you must understand how the world works—and that is the value of human and physical geographic knowledge.
Required Reading
Now that you have a basic understanding of the definition and scope of geography, study the Wikipedia article on Geography linked from the Lesson 2 Checklist [40]. Compare and contrast what I have said with the article. Are there any significant differences, and if so, why?
The Four Traditions of Geography
There are some other ways to conceptualize the field of geography. Parkinson suggested that geography has four traditions: The Earth Science Tradition, Culture-Environment Tradition, Locational Tradition, and Area Analysis Tradition. Geographic techniques support these traditions. The chart below shows how selected subdisciplines fit within these four traditions.
All the subdisciplines, with the exception of the Regional Approach, are topical approaches. The regional approach breaks the Earth down into areas that share certain uniform cultural and physical characteristics. Regional geographers then study the human and physical geography of that particular region. We typically break the world into the cultural regions of North America, South America, Europe, Russia and the Slavic World, the Middle East and North Africa, Sub-Saharan Africa, South Asia, East Asia, Southeast Asia, and Australia and Oceania.
Geographic Systems Theory
Yet another approach to understanding the scope of geography is Geographic Systems Theory. A system is a series of components such that, when you add energy to it, the components work together to produce an output. Take for example an automobile. Your gasoline-powered car includes multiple subsystems including the chassis with suspension and tires, the engine, the cooling subsystem, the transmission, the fuel tank (with fuel pump and fuel filter), the steering subsystem, etc. When you add gasoline, the engine generates energy, which the transmission sends to the wheels, which results in the output of the car moving. Open systems exchange both energy and matter with the outside universe. Closed systems exchange only energy.
The earth is a system. Is it a closed system or an open system? The answer is the earth is a closed system in that it exchanges energy with the universe, but it does not exchange any significant amount of matter (space junk and meteorites are insignificant—if the earth is destroyed by an asteroid I will admit I was wrong).
According to Geographic Systems Theory, the Earth has two major sub-subsystems, which are the Physical Subsystem and the Human Subsystem. The Physical Subsystem has four major component subsystems of the Atmosphere, Hydrosphere, Lithosphere, and Biosphere. The Human Subsystem has three major components of Beliefs, Institutions, and Technologies.
The atmosphere is the gaseous envelope that surrounds the earth and sustains air-breathing animals. The lithosphere is the solid rock and soil that comprises the outer solid layer of the planet. The hydrosphere includes all the liquid and solid water (water vapor is in the atmosphere). These three spheres are "abiotic" in that they are non-living. The final sphere is the biosphere containing all life. The biosphere relies on the other three abiotic spheres to function for it to sustain life.
A critical part of systems theory is understanding that if one system is significantly degraded, then the system function as a whole degrades. And if one system fails, then the whole system fails. If you consider that Planet Earth is the spaceship for the human race, and that we rely on all of its systems to function properly, you start to contemplate why we do not take better care of it. It is the only spacecraft we have and there are no lifeboats.
Geography as Synthesis
Geography is a synthesizing discipline in that geographers take topical subjects and analyze them through the spatial filter, thus seeing the world in new ways. This synthesis is very exciting and liberating in that geographers have the freedom to explore many different subjects and apply topical, chronological, and spatial approaches while integrating both the human and physical world. No other academic discipline takes such a holistic approach, and that makes geography special.
The Necessity for Geographic Literacy
The world is getting smaller, more crowded, and more integrated as the population expands, resources diminish, and globalization brings us all closer together. The US is a "hyper-power" with unprecedented influence around the globe. For the citizens of such a country that is also a democracy comes a duty to be geographically literate—to understand how this planet works in terms of its physical and human geographies. Geographically illiterate citizens will at best be ignorant of what their government is doing globally, and at worst support their government in making bad decisions that are detrimental to national, regional, and global stability and well-being.
Globalization means that America will interact with its global neighbors through combinations of cooperation, competition, and (unfortunately) occasional conflicts. Thus, it is essential that American citizens be geographically literate so that they may hopefully cooperate most of the time, compete some of the time, and occasionally engage in conflict. Viewed this way, geographic illiteracy might be seen as a threat to national security. Of course this is true for citizens of other nations as well, however national rankings of geography literacy show that our neighbors abroad understand the importance of geographic knowledge and do not suffer our illiteracy.
Geographic literacy for intelligence professionals (especially analysts and managers) is especially important. The geospatial intelligence professional must be geographically literate to fully leverage the power of geographic techniques.
To reiterate the fundamental rationale for this course:
All the geospatial technology in the world can tell you what is happening where and when. It may even tell you something about how it is happening. The technology, however, will NOT tell you why it is happening. To understand the why, you must understand how the world works—and that is the value of human and physical geographic knowledge.
A geographically illiterate analyst or manager is likely to produce flawed analyses and poor decisions. In the national security arena, this could result in disastrous policy decisions. In the disaster relief/international humanitarian aid arena, this might result in wasted resources and lost lives.
If you get the feeling I am passionate about this topic—you are right. I am on a mission to stamp out geographic illiteracy, one classroom full of ignorant people at a time. That is a major motivation for me to teach this course to current and future geospatial intelligence professionals.
Required Reading
Why Geography Matters More than Ever (De Blij, Harm J.)
I now want you to read your second reading assignment by the noted geographer Dr. Harm de Blij. Dr. de Blij (1935–2014) served as the resident geographer of ABC's morning television program Good Morning America for several seasons, as well as an editor of National Geographic magazine. His book on Why Geography Matters More than Ever is worth your time to read. For our purposes, you will only read Chapter One, but if it piques your interest, I encourage you to read the whole book.
Registered students can access a PDF of the reading in Lesson 2 in Canvas.
Click the following link to access a PowerPoint Presentation with a review of the Definition, Nature, and Scope of Geography [41].
Click the thumbnail below to see the pdf version of my Geographic Fundamentals of Geospatial Intelligence ppt.
2.5 What Is Geospatial Intelligence?
As I said in the introduction, many of the GEOINT practitioners figure they know the definition of geospatial intelligence—it is what their agency says it is and it is what they do.
The United States National Geospatial-Intelligence Agency or NGA —as the name implies— is the primary government agency responsible in the US for geospatial intelligence. The NGA's mission is to "provide world-class geospatial-intelligence and lead the Global GEOINT Enterprise." The NGA defines GEOINT as:
"The exploitation and analysis of imagery and geospatial information to describe, assess, and visually depict physical features and geographically referenced activities on the Earth. GEOINT consists of imagery, imagery intelligence, and geospatial information." (National Geospatial-Intelligence Agency, n.d.)
But language is powerful, and words have different meanings to different people. If we are to think critically, we must go beyond accepting things at face value and do some analysis, synthesis, and evaluation to ultimately come to a judgment about the information. As we learn to apply critical approaches, you will find that a key question concerns power relationships. For example, as you research definitions of GEOINT, you will find that the NGA definition dominates. But why is that so? Why are alternative definitions not readily evident when you do a Google or other search? The answer may be that the NGA is a powerful government agency with lots of money and employees. The sheer size of their organization makes their definition dominant in the literature, media, and on the web. The NGA is also a part of the US Department of Defense and is both a national intelligence agency and a combat support agency. NGA's place in the government will naturally focus it on national security and military issues. As you analyze and evaluate the NGA definition, is it necessarily the last word? Are there other definitions? Are there other applications besides national security applications?

Required Reading
Geospatial Intelligence and the Geospatial Revolution
Reading the chapter "Geospatial Intelligence and the Geospatial Revolution" provides an expanded definition of geospatial intelligence and addresses several foundational principles of the discipline.
Registered students can access a PDF of the reading in Lesson 2 in Canvas.
Reference:
National Geospatial Intelligence Agency (n.d.). NGA's Mission. Retrieved October 3, 2023 from https://www.nga.mil/about/Mission.html [43]
2.6 Geospatial Intelligence Applications
I want to share a story with you. Getting this geospatial intelligence program approved took a lot of negotiation between different groups within the Penn State Geography Faculty. The members of the faculty, that come from technical geography backgrounds and/or the military and who work with NGA and other agencies, initially envisioned the program as predominantly a technical course of study in support of the traditional US national defense mission. We will call this the traditional technical security discourse.
Another group of faculty members, however, coming from human geography backgrounds, were uncomfortable with this primarily technical and security approach. They proposed an alternative discourse that went beyond security to encompass disaster preparedness and international disaster relief applications (as well as some other applications). They also insisted that critical thinking skills and geographic knowledge that goes beyond the techniques were absolutely essential to support the ultimate goal of producing skilled geospatial intelligence analysts. We will call this the human discourse.
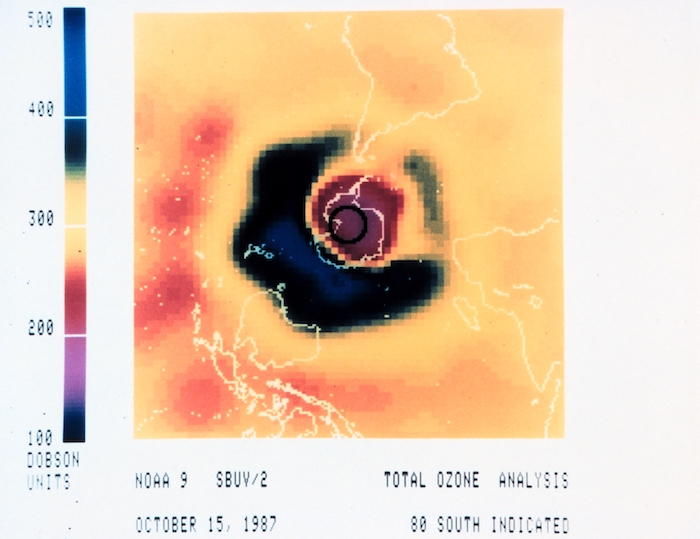
So the lesson here is that "Geospatial Intelligence" is not a naturally occurring phenomenon that has a "correct" definition that is fixed in stone. Geospatial Intelligence in terms of its definition and scope is a socially contested and constructed concept. To understand that human activities are socially contested and constructed, it is very instructive to study the underlying power relationships. Even the NGA definition and scope were socially constructed as different elements of the agency negotiated the creation of the official definition. This process is continuous.
This story has a happy ending. The social negotiation that took place, resulted in a compromise that retained the key elements of the technical/security discourse, while expanding the scope of the program to include emphasis on critical thinking and other applications of GEOINT (although not all possible applications). At the end of the day, all concerned felt that the program was far better for the input of both sides. This viewpoint was subsequently validated when outside agencies were shown the program and voiced their enthusiasm and support for it.
The major evaluated activity for this lesson is the Lesson 2 - GRADED Discussion Forum (#1). To prepare for the activity, I want you to do a web search and see if you can find some alternative definitions and applications of geospatial intelligence. We will be particularly interested in the nature of the organizations that have alternative definitions and applications. If you find some sites that you think other people in the class might find useful, consider adding the URL to the class "Webliography." (See panel below.)
Webliography
As you find sites of interest, add the URL and a comment on the content and why the site is of interest to our "Webliography." To access the Webliography, return to your Canvas window and look for the Webliography wiki page in our course.
Knowledge Check
2.7 Deliverable: Lesson 2 - Graded Discussion Forum (#1)
An online discussion forum is the equivalent to a traditional graduate school classroom seminar. I expect you to have studied the online lesson, read the assigned readings, and conducted some web research as indicated in the lesson. When you access the graded online discussion forum for Lesson 2, you will find that I (with the help of Matt Bugaj, my Canvas technical assistant at Penn State) have posed two discussion questions to get the ball rolling. The minimum requirement is that each of you post one primary response to each of my questions and comment at least twice on your classmates' posts. The idea here is to have an online conversation so that we can explore different ideas and alternative ways of seeing things. I expect you to demonstrate critical thinking and challenge the ideas of your classmates and yourselves. However, I know all of you will treat each other with dignity and respect and keep the discussion collegial and professional. I will moderate and facilitate the discussion, but do not be surprised if I have limited input. The function of the online discussion just as the traditional graduate seminar is for you to learn from each other. I encourage you to bring your own experiences and opinions into the discussion. That makes it so much more interesting.
CAUTION!
In the intelligence community, much of what they do is classified for national security reasons. Everything in this course is unclassified. Presume that the other students do not have a clearance, 'need to know', and remember that everything in this course is done in a non-secure environment. DO NOT divulge, discuss, or even hint at any classified information. Also, remember that this is an academic course open to anyone, including foreign nationals. If you are a government employee, remember that operational security and information assurance are your responsibilities. Please bring any security concerns to my attention via email, and police yourselves.
Deliverable: Lesson 2 - GRADED Discussion Forum (#1)
Return to Lesson 2 in Canvas. Look for the Lesson 2 - GRADED Discussion Forum (#1) where you will find the two questions for this assignment. The minimum requirement is that each of you post one primary response to each of my questions and comment at least twice on your classmates' posts.
PLEASE address each question in a separate primary post to make it easier for your classmates to respond to your ideas.
Note: Please post your primary response to the questions by Sunday evening to allow time for everyone to post comments by Tuesday night.
2.8 Summary and Final Tasks
Summary
In this lesson, we looked at Kant's three ways of ordering knowledge. We discussed definitions of geography and geospatial intelligence, the scope of the subject, and examined why geography as a subject and a discipline is fundamental to the idea of geospatial intelligence, and you read "Why Geography Matters." We also noted that different people and different agencies have different understandings of the definition and scope of the field. The lesson also included a brief discussion of how this course grew from a predominantly national security based course to include disaster preparedness, and international humanitarian aid.
Final Tasks
Deliverable: Lesson 2 - GRADED Discussion Forum (#1)
Return to Lesson 2 in Canvas. Look for the Lesson 2 - GRADED Discussion Forum (#1), where you will find the two topics for this assignment separated out in their own discussion forums. The minimum requirement is that each of you post one primary response to each of my questions and comment at least twice on your classmate's posts.
Note: Please post your primary response to the questions by Sunday evening to allow time for everyone to post comments by Tuesday night.
Deliverable: Lesson 2 - GRADED Quiz (#2)
Return to Lesson 2 in Canvas. Look for the Lesson 2 - GRADED Quiz (#2), where you will find the fifteen question quiz on this week's readings. You will have unlimited time, and it is open book, but be forewarned. This is a tough quiz. To do well, you must have read and studied the readings.
Before you move on to Lesson 3, double-check the Lesson 2 Checklist [40] to make sure you have completed all the required activities for this lesson.
Looking Ahead
In our next lesson, we focus on academic and professional writing. Your deliverable is a critical analysis which will give you the opportunity to demonstrate your higher order and critical thinking skills.
Lesson 3: Contemporary Thought
Lesson 3.1 Overview
You now possess a basic understanding of higher order and critical thinking skills, as well as some knowledge about the nature of geography, and the definitions of geospatial intelligence. This lesson capitalizes on that base of knowledge, and gives you the opportunity to demonstrate and improve your professional and academic writing skills.
To exercise our recently acquired critical thinking skills and geographic knowledge, we are going to carefully read the works of several eminent scholars: Samuel Huntington, Stephen Walt, and Edward Said. Huntington's "The Clash of Civilizations?" was a provocative article that articulated a new geopolitical discourse for the post-Cold War era. Published in Foreign Affairs in 1993, it created an immediate stir and resulted in a book length treatment of the idea by the same name. Steven Walt is a professor of international relations at Harvard. He challenged Huntington’s clash theory in his article “Building up New Bogymen” published in Foreign Policy in 1997. Edward Said was a Palestinian-American scholar of the Middle East famous for his writings on orientalism. Said countered Huntington's discourse in his article "The Clash of Ignorance" published in The Nation in 2001. Works of both Huntington and Said are still frequently referenced and cited. For example, see recent articles on Huntington [45] and Said [46].
You will have the pleasure of writing your first critical analysis paper as your deliverable for this lesson. For many of you, this will be a challenge as you have not written a graduate level paper employing critical thinking skills. However, the ability to clearly and concisely articulate your critically derived thoughts is another essential skill for the geospatial intelligence professional in any agency or organization.
Lesson Objectives
At the end of this lesson, you will be able to:
-
analyze multiple sources challenging and supporting a particular thesis (Huntingdon's Clash of Civilizations thesis);
-
defend your own analysis using your higher order and critical thinking skills;
- write a graduate level academic paper.
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
Lesson 3.2: Checklist
Lesson 3 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 3:
- Work through Lesson 3 in this website.
- Read (the following are available in Canvas):
- "The Clash of Civilizations?" Samuel Huntingdon
- "Building New Bogeymen" Stephen Walt
- "The Clash of Ignorance" Edward Said
-
Research two academic journal articles that support Huntington’s thesis.
-
Write your paper in accordance with the assignment and technical instructions and save using the correct file name convention.
- Submit Lesson 3 - GRADED Paper (#1) in Canvas.
Lesson 3.3 Academic Paper Assignment Details
Description
Write an academic paper comparing and contrasting the required readings; Huntington, Said, Walt, and at least two supporters of Huntington's idea, and then articulate and defend your own evaluation and judgement of the Huntington discourse (do you agree or disagree with him and why?) Your judgement is not your personal opinion. Your judgement must logically derive from your analysis and evaluation of your source material.
Your paper should utilize all of the content included in this lesson and be:
- Concise (1000 words plus/minus 10%)
- well organized with an introductory paragraph that clearly states your purpose and outlines the supporting points you will be addressing for your audience
- properly formatted
- written in the third person and active voice
- uses correct citations and bibliographic references
- is generally correct in terms of spelling, grammar, punctuation
Submission
Please submit your reflection paper in Microsoft Word Format using the following file naming convention: Lastname_Firstname_Paper_1.doc
Grading
Please see Canvas for the Lesson 3 - GRADED Paper (#1) Rubric that will be used to assess your work.
Lesson 3.4 Doing Academic Research
You might find doing research somewhat daunting, but you probably do research all the time. Consider planning a vacation. You most probably don’t just jump in the car and drive off with no destination in mind (OK maybe some of you do—to each their own). You go through a process to plan out your vacation and this includes research.
Brigham Young University Library lays out six steps to doing research. You can find the full article here: Basic Research Strategy - Step-by-Step Guide & Research Rescue - Subject Guides at Brigham Young University [47].
Step 1: Find and narrow your topic
Say your daughter lives in China and you would like to take a vacation to China. You have narrowed the topic of your vacation to China.
For your first paper, you have a very specific topic and your instructor has done step one for you.
Step 2: Finding articles
Now that we want to go to China, we can start our research going from the general to the specific. You can use the internet to look up articles on China in general and then zoom in on travel articles specifically.
In academic writing, articles come in many different flavors. You could use a general internet search, a more specialized search such as Google Scholar, or a library (you have access to the Penn State Library online) that has subscriptions to specialized databases with academic articles.
You may find some articles in trade journals such as NGA’s Pathfinder magazine (NGA Pathfinder Archive | National Geospatial-Intelligence Agency [48]). These are good sources but such articles are usually not “peer reviewed”. Articles in academic journals have been vetted through a process of blind peer review and thus have the stamp of approval of a particular academic discipline. Let us say you write a research article based on data you collected. You submit your article to an academic journal. The editor of the journal removes anything identifying you as the author and sends it out to two or three reviewers who have expertise with your topic. The reviewers look at your data sources, collection methods, analytical methods, literature review, etc., as well as your organization and writing style. They then recommend to the editor that they accept, accept with revision, or reject your article. This peer review process ensures the quality of the work and is a key institutional stamp of approval. University professors must often have a sustained record of peer-reviewed research publications to get tenured and promoted.
One other thought on journal articles: don’t just pick the first two you find. You should read the abstract of a few that sound interesting before selecting them and diving into the analysis.
Step 3: Finding Books
Books can be an excellent source for in-depth information. In our China trip example, you might find a book on the history and geography of China to give you deep background on the country and ideas for places to visit.
Books can be expensive so using the Penn State Library is a good idea. The library has access to many e-books. If you find a book that is not available as an e-book, you can request that the book be mailed to you, free of charge.
Step 4: Evaluating Credibility
This step is key. As you look at sources, you want to understand if they are commercial, government, academic, news, or opinion-making oriented. In our China example, is our source an advertisement from a tour company, a travel advisory from the US Department of State, an individual review based on a personal experience, or a peer-reviewed academic journal article?
Take for example a student paper on the pros and cons of gun control in America. How credible would you consider an opinion piece (with no citations) in the magazine American Rifleman (which is the official journal of the National Rifle Association)?
For this week’s assignment, you would do well to use reputable academic journal articles.
Step 5: Accessing and storing your sources
For big research projects like a major research paper, master's thesis, or PhD dissertation which might have tens or hundreds of sources you should consider using a source management and archive tool. Ask your research librarian for help.
Step 6: Citing your sources
YOU MUST CITE YOUR SOURCES! (I hate it when people scream at me in all caps.) Most students understand that you must cite your sources. If you do not, then you are indicating that the ideas are your original work—and that is plagiarism and academic dishonesty.
But there is another key reason we cite our sources in academic work, and that is to help other scholars conduct their research. Readers must be able to understand where your ideas came from, and must be able to easily access the original source you used. This helps them verify your use of the source, and more importantly, allows them to go to that source and look at your source’s sources. In this way, a scholar can follow links in a chain to help with their own research. Many sources are now found online. Ensure you provide the full universal resource locator (URL or web address) preferably as a clickable link in your citation.
This week’s lesson has detailed technical instructions on how to cite your sources in text and how to provide a full bibliographic reference in the “Works Cited” section at the end of the paper. Every citation must have a bibliographic reference in Works Cited.
Students who do not cite their sources get an automatic “REDO” on the paper and a very cross look from the instructor.
Penn State Library
Penn State has a great library with many resources for online students. Here are some key links:
Online Students Use of the Library [49]
Lesson 3.5: Intelligence Writing Guidelines
The intelligence writing style may be different than what most of you are familiar with. Because intelligence analysis requires clarity and precision, the written text explaining your analysis must also be clear and precise. For these reasons, please review the Writing Guidelines adopted from the text, "Intelligence and Crime Analysis: Critical Thinking through Writing" by David Cariens.
Note:
David Cariens spent over 30 years as an analyst with the CIA and wrote for all levels of the U.S. government. He headed the CIA University to teach new analysts writing and briefing skills. Since retirement from the CIA, he teaches intelligence analysis and writing for the intelligence community. Additional information about Cariens can be found at his website [52].
The following text is from “Intelligence and Crime Analysis: Critical Thinking through Writing” (2012) by David Cariens.
Rules for Intelligence Writing
From "Intelligence and Crime Analysis: Critical Thinking through Writing," (2012) p. 18.
Writing is thinking on paper. When you write you give the reader a glimpse of your thinking abilities-you are saying something about yourself. Like it or not, people form images about you based on how you write. If there are a number of spelling or grammar mistakes, what are you saying about yourself - that you are careless, not well educated, lack pride? Writing can be easy if you will remember a few simple rules:
Rule One: Think before you write. Know what you want to say before you put pen to paper or fingers to keyboard.
Rule Two: Organize your thoughts. If you are writing a longer paper or memorandum, take time to organize your thought so you can present a logical argument.
Rule Three: Use simple sentences wherever possible-in the active voice.
Rule Four: Pick your words carefully. Use shorter English words based on the Anglo-Saxon roots of the language. Usually these words are clear and void of nuance and innuendo.
Rule Five: Pursue the economy of language. Make each word count and use familiar terms.
Rule Six: Make the majority of your sentences short and to the point.
Rule Seven: Self-edit and proofread.
The Intelligence Style is expository writing. It is plain talk, straightforward and matter-of-fact communication. Expository writing efficiently conveys ideas, requires precision, and stresses clarity. A major goal of expository writing is to never make the reader wonder what the main point is in the paper or paragraph. Expository writing emphasizes the use of the active voice.
Basic Principles of Analytic Writing
From "Intelligence and Crime Analysis: Critical Thinking through Writing," (2012) pp. 87-88.
- Put your conclusion(s) first. If the reader reads nothing else, he or she will know from the topic sentence of the first paragraph the main intelligence point or conclusion you want to make.
- Organize your analysis by your topic sentences. Make sure the topic sentences of each succeeding paragraph ties to, explains, or advances your analysis.
- Know the formats your intelligence organization uses and know when to use them.
- Be precise: pick your words carefully so that you are sure you are conveying the right message.
- Be economical in your use of words-avoid adjectives and adverbs.
- Clarity trumps all else in intelligence writing. Your intelligence analysis must not leave the reader wondering what you mean or why you decided to write.
- Know when to use the active voice and when to use the passive voice [note: while this is David Carien's perspective, do not use passive voice in this class].
- Self-edit and then welcome the editorial review of others.
- Know the reader’s needs-know why the reader needs to take the time to read what you have written.
Mistakes
From "Intelligence and Crime Analysis: Critical Thinking through Writing," (2012) p. 41.
Six mistakes are common to all new intelligence analysts, mistakes that must be corrected to have a career in intelligence analysis:
- Breaking away from the more verbose academic writing style. The simple truth is, if you cannot write in the tighter intelligence style, you do not have a career.
- Being content with throwing down numbers and facts and not making judgments. These analysts do not identify gaps in knowledge, nor do they identify opportunities. In the case of new law enforcement analysts, they do not make recommendations.
- When new analysts do make judgments, they do not give their strongest evidence to support their analysis.
- When they write, they often write something that is very interesting, but their draft is not intelligence-it does not address an intelligence problem or question.
- They do not conceptualize their main point at the outset, and their drafts do not have an angle. If the intelligence is not clear, if there is no indication as to why a policy-maker should take his or her time to read their product, they have lost the reader.
- They overuse adjectives and colorful language; their goal seems to be to elicit an emotional response. The net result is sensationalism. This emotionalism undercuts the objectivity and credibility of the intelligence.
References
Cariens, D. J. (2012). Intelligence and crime analysis. Lulu.com.
Lesson 3.6: Technical Specifications
Your assignment is to write a critical analysis paper of 1000 words (plus or minus 10%), which is about four double-spaced pages in a 12-point font. Ensure you have a title and your name on the paper. Use one-inch margins all around and please use either Times Roman or Arial as your font.
Organization
Your paper must be well organized with an introductory paragraph that clearly states your thesis/purpose and outlines the supporting points you will be addressing for your audience. You may want to begin your paper with, "The purpose of this paper is to …" The body of the paper follows with paragraphs in logical succession that allows you to make your point. Finish with a conclusion that very briefly summarizes the paper and powerfully ends with your concluding statement.
Citing Your Sources
Cite your sources in text using the format of (author date), e.g. (Corson 2000). Include a “Works Cited” section at the end of your paper using the bibliographical reference format below.
Multi-authored journal article:
Single authored journal article:
Book Chapter:
Book:
Notes
I am not overly worried about the exact format as long as I can look at the author and date and easily reference it to the full citation in the works cited section. Citations do not count against your 1000 words.
Page Numbers
Please insert page numbers at the bottom of the pages. You may also include images, maps, charts, etc. Please ensure you include captions and reference any graphics in the text. Captions do not count against your 1000 words. Cite the source of the graphic in the caption, e.g. "author's photo."
Voice
Write your paper in active voice and avoid passive voice. Passive voice begs the question of who or what is the subject. For example, “You have been ordered to attack the hill” is passive voice. It begs the question who ordered me to attack that dangerous hill? Active voice puts the subject at the front of the sentence. “General Corson orders you to attack the hill” is active voice. Active voice also makes you take responsibility for your writing and helps you avoid imprecise language.
Writing in the third person (thus avoiding I, we, us, and our) helps writers maintain their objectivity and avoid personalizing the work. Your analysis and judgment must stand on its own. Do not assume the reader knows the assignment or has read the lesson or readings.
As indicated above, we write in third person in academic and professional writing. First person is “I, we, us, our”. Second person is “you, your”. Third person is “the author, this paper, Corson”. For example, “I want you to write in third person” is first person. “You must write in third person” is second person. “Corson contends that academic writing is done in third person” is third person.
Punctuation
Note the difference between a comma, semi-colon, and colon.
A comma indicates a pause between parts of a sentence. It is also used to separate items in a list and to mark the place of thousands in a large numeral. (Dictionary.com)
The most common semicolon use is joining two independent clauses [53] without using a coordinating conjunction [54] like and. Semicolons can also replace commas when listing items that already use commas, such as listing cities and states. (Grammerly.com)
The colon (:) is a punctuation [55] mark consisting of two equally sized dots aligned vertically. A colon often precedes an explanation, a list, or a quoted sentence. [56]It is also used between hours and minutes in time, [57]between certain elements in medical journal [58]citations, between chapter and verse [59] in Bible citations [60], and, in the US, for salutations [61] in business letters [61] and other formal letter writing [62]. (Wikipedia.com)
Lesson 3.7 Review of Bloom's Taxonomy and Critical Thinking Skills
Bloom's Taxonomy
Please review Bloom's taxonomy and note what I mean when I say demonstrate higher order thinking skills.
- Knowledge - is the lowest level of learning outcomes. Memorizing and recalling a wide range of facts, data, or even complete theories falls into this category. Being able to remember and regurgitate facts from reading assignments is an example of this category. This is NOT an acceptable level of scholarship for graduate studies.
- Comprehension - occurs when you understand the meaning of the material. You can demonstrate comprehension by interpreting the material through explanation or summation, by showing effects or consequences, or by translating the material from one form to another. While comprehension is critically important, it is still NOT an acceptable level of scholarship in graduate study.
- Application - is the ability to take knowledge that you comprehend and apply it to new situations. This could include applying new methods, principles, concepts, theories, or laws to new situations. Application demonstrates higher order thinking than simple memorization and comprehension and will often be required in follow-on technically oriented courses.
- Analysis - is essentially taking something and breaking it apart to see how it works. Deconstructing something to see its component parts and how they relate to the organizational structure are good examples of analysis. Analysis is higher order thinking because it requires an understanding of both the content and structure of the material in question. Graduate level coursework will often ask you to analyze something as part of an assignment.
- Synthesis - is essentially taking several different ideas and putting them together to form a new whole. This might mean taking numerous research sources, analyzing them, and then taking select components to build a new idea presented as a paper or presentation. Synthesis stresses being creative in formulating new patterns, ideas, or structures. Your reflection papers, case studies, and research papers will often demand that you synthesize various inputs.
- Evaluation - is the ability to make judgments about the usefulness, value, or veracity of given material for a specific purpose. The judgment must be based on definite criteria rather than instinct, faith, or feeling. These criteria may be external (relevance to purpose) or internal (organizational criteria). Evaluation is the highest in the cognitive hierarchy as it includes the other elements plus a conscious value judgment based on defined criteria.
Critical Thinking Skills
While you will have to demonstrate some knowledge and comprehension, you must demonstrate the ability to analyze, synthesize, and evaluate complex ideas to produce a satisfactory reflection paper. Now review the cognitive skills of the critical thinker:
- Interpretation is to comprehend and express the meaning or significance of a wide variety of experiences, situations, data, events, judgments, conventions, beliefs, rules, procedures, or criteria. The three sub-skills of interpretation are categorization, decoding significance, and clarifying meaning.
- Analysis is to identify the intended and actual inferential relationships among statements, questions, concepts, descriptions, or other forms of representation intended to express belief, judgment, experiences, reasons, information, or opinions. The three sub-skills of analysis are examining ideas, detecting arguments, and analyzing arguments.
- Evaluation is to assess the credibility of statements or other representations which are accounts or descriptions of a person's, perception, experience, situation, judgment, belief, or opinion; and to assess the logical strength of the actual or intended inferential relationships among statements, descriptions, questions or other forms of representation.
- Inference is to identify and secure elements needed to draw reasonable conclusions; to form conjectures and hypotheses; to consider relevant information and to educe the consequences flowing from data, statements, principles, evidence, judgments, beliefs, opinions, concepts, descriptions, questions, or other forms of representation. The three sub-skills of inference are querying evidence, conjecturing alternatives, and drawing conclusions.
- Explanation is to state the results of one's reasoning; to justify that reasoning in terms of the evidential, conceptual, methodological, criteriological, and contextual considerations upon which one's results were based; and to present one's reasoning in the form of cogent arguments. The sub-skills under explanation are stating results, justifying procedures, and presenting arguments.
- Self-Regulation is to self-consciously monitor one's cognitive activities, the elements used in those activities, and the results educed, particularly by applying skills in analysis, and evaluation to one's own inferential judgments with a view toward questioning, confirming, validating, or correcting either one's reasoning or one's results. The two sub-skills here are self-examination and self-correction.
You must demonstrate the appropriate critical thinking skills based on the approach you take. On this first paper, you may want to explicitly articulate the higher order thinking skills and type of critical thinking that you are applying. Please do not ruin the flow of your paper by overdoing this explicit articulation (be subtle).
This may seem daunting and cause some of you to worry. Remember that I am on your side and I want to help you develop these skills. As you get into this very intellectually stimulating exercise, I hope that you will actually find that critical thinking and concise written reflection are enjoyable.
Lesson 3.8: Summary and Final Tasks
Summary
In this lesson we:
- read:
- Huntington’s “The Clash of Civilizations?”
- Walt’s “Building up the New Bogeyman”
- Said’s “The Clash of Ignorance”
- researched two academic journal articles supporting Huntington’s thesis
- discussed the intelligence writing guidelines (or the uniqueness of writing in the intelligence field)
- reviewed the necessity and use of higher-order and critical thinking skills in intelligence writing.
The most important thing to get out of Lesson 3 is the ability to write a clear and concise academic/professional paper to explain your analysis and evaluation to others.
Final Tasks
Note:
Deliverable: Lesson 3 - GRADED Paper (#1) - Critical Analysis
When you have completed your paper, return to Lesson 3 in Canvas. Look for the Lesson 3 - GRADED Paper (#1) assignment link where you will submit your paper. You will find directions for submitting your papers when you enter the assignment.
Before you move on to Lesson 4, double-check the Lesson 3 Checklist [63] to make sure you have completed all the required activities for this lesson.
Looking Ahead
Next week, we begin part two of the course, addressing national security applications of geospatial intelligence. Lesson Four: Intelligence Organizations and Functions introduces you to a broad overview of intelligence, including definitions of intelligence, purposes of intelligence, and US intelligence community organization and functions. There will be a lot of reading once again, and the quiz experience. The next lesson will cover:
- the definition of "intelligence" as articulated by Lowenthal;
- the evolution of the US intelligence system;
- the layout of the US intelligence infrastructure and functions of the major agencies;
- the intelligence process including: requirements, collection, processing and exploitation, analysis and consumption, and feedback;
- the functions of collection and analysis as described by Lowenthal.
I am looking forward to reading your papers.
Lesson 4: Intelligence Organization and Functions
4.1 Overview
This lesson will take a broad look at the history, organizations, and functions of the US intelligence community. Let me give you fair warning that this week is primarily a reading week. We are going to leverage the knowledge and experience of Mark Lowenthal, who wrote your textbook Intelligence: From Secrets to Policy, now in its ninth edition. Dr. Lowenthal has thirty years of intelligence experience in both the executive and legislative branches of government, as well as in the private sector. He retired in 2005 from the government, having served three years as both the Assistant Director of Central Intelligence for Analysis and Production and Vice Chairman of the National Intelligence Council for Evaluation. He now runs a national security education, training, and consulting firm called the Intelligence and Security Academy, and he is an adjunct professor at Columbia University.
My teaching approach this week is to have you read six chapters from the textbook. Fortunately, this book is very well written, the chapters are concise (short and to the point), and I found it very interesting and enjoyable reading. I want you to read the book in conjunction with the online lesson. I will provide questions to contemplate and guide you as you read each chapter. After you have read the chapter, you will complete the Lesson 4 - GRADED Quiz (#3), which you can take one time for your lesson grade.
Lesson Objectives
At the end of this lesson, you will be able to:
- discuss the concept of "intelligence" as articulated by Lowenthal (chapter 1);
- trace the evolution of the US intelligence system (chapter 2);
- examine the layout of the US intelligence infrastructure
- differentiate the functions of the major agencies (chapter 3);
- identify key components of the intelligence process, including: requirements, collection, processing and exploitation, analysis and production, dissemination and consumption, and feedback (chapter 4);
- identify the functions of collection and analysis as described by Lowenthal (chapters 5-6).
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
4.2 Checklist
Lesson 4 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 4:
- Work through Lesson 4 in this website.
- Read the following chapters from Lowenthal's Intelligence: From Secrets to Policy 9th edition. (Required text):
- Chapter 1: What is Intelligence?
- Chapter 2: The Development of US Intelligence
- Chapter 3: The US Intelligence Community
- Chapter 4: The Intelligence Process - A Macro Look: Who Does What for Whom?
- Chapter 5: Collection and the Collection Disciplines
- Chapter 6: Analysis
- Read NGA History fact sheet.
- Participate in the "Share your thoughts on Lesson 4" UNGRADED Discussion Forum.
- Participate in the "What is intelligence?" UNGRADED Discussion Forum.
- Take Lesson 4 - GRADED Quiz (#3) in Canvas.
4.3 What is Intelligence?
Language has power. Those who get to determine definitions often get to determine the scope of "legitimate" discussion for a particular topic. Thus, certain discourses are legitimate and privileged, certain discourses are marginalized as less important, and some discourses may be tainted as illegitimate and not worthy or allowable for discussion. The legitimacy and privilege of a discourse is critical when it comes to resource allocation. Those with privileged discourse win, while those with marginalized or illegitimate discourses lose, to a lesser or greater degree.
Required Reading
Read Lowenthal's Chapter 1: "What is Intelligence?" in Intelligence: From Secrets to Policy.
As you read, do some critical thinking and ask yourself:
- Who is the author, and what is his agenda?
- Why do they define intelligence as they do?
- What are alternative discourses that might define intelligence differently?
- Why is this discourse powerful, as evidenced by its inclusion in a standard textbook now in its sixth edition?
- What might be your alternative definition?
Knowledge Check
Prepare for the quiz by answering the following questions.
4.4 The Development of US Intelligence
Required Reading
Read Lowenthal's Chapter 2: "The Development of US Intelligence" in Intelligence: From Secrets to Policy.
As you read chapter 2, do some critical thinking and ask yourself:
- Why did the US not develop a formal intelligence establishment until relatively recently?
- Must a threat based foreign policy continue to be the mainstay of US foreign policy?
- Are there other alternatives to competitive analysis?
- What is the optimal relationship between producers and consumers of intelligence?
- How does the issue of "a heavy reliance" on technology relate to geospatial intelligence?
Read NGA History fact sheet [64].
As you read, note:
- The National Geospatial-Intelligence Agency (NGA) is responsible within the US intelligence community for imagery intelligence (as Lowenthal would term it - it is more correctly referred to as geospatial intelligence).
- You will read about the NGA and the National Geospatial-Intelligence Strategy (NGS) next week.
- Reading the fact sheet will help you familiarize yourself with the history of the NGA.
Knowledge Check
Prepare for the quiz answering the following questions.
4.5 The US Intelligence Community
Required Reading
Read Lowenthal's Chapter 3: "The US Intelligence Community" in Intelligence: From Secrets to Policy.
As you read, think critically and ask yourself:
- As a CIA executive coming from the analysis and production community, what cultural filters does Lowenthal bring to his discussion? What might this chapter look like if a covert operation or geospatial intelligence professional wrote it?
- Is the organization of the US intelligence community the best way to do business, or can you think of alternative approaches?
- Geospatial intelligence is concentrated in the National Geospatial Intelligence Agency (formerly the National Imagery and Mapping Agency and formerly the Defense Mapping Agency (as its core)). Is this the best way to organize the geospatial intelligence contribution? In a later lesson, we will discuss in detail the evolution of the NGA and why it evolved as it did.
From the Armed Forces to the NSA to the Treasury Department, PostTV breaks down the 16 different agencies and organizations that collect intelligence for the U.S. government—and the 17th office that oversees them all. Watch the video below. (Davin Coburn / The Washington Post)
Video: America's intelligence community, explained (2:11)
There are 16 different federal agencies gathering intelligence for the US government. In 2004, a 17th Office of the Director of National Intelligence was set up to oversee them all. Here's what to know about America's intelligence community and how the different branches operated.
Start with the Armed Forces. Each service has at least one major intelligence organization to support its information needs. Then there are intelligence departments. Those are the offices embedded in other government agencies to enable their missions. The office of National Security Intelligence, which analyzes major drug cartels and facilitates counter-narcotics efforts. The Office of Intelligence and Counterintelligence, which provides analysis on foreign nuclear weapons and global energy issues. The Office of Intelligence and Analysis, which focuses on domestic threats. The Bureau of Intelligence and Research, which provides analysis for the Secretary of State and ambassadors, and the Office of Terrorism and Financial Intelligence, which focuses on international economic issues.
Finally, the National Agencies that help advise the Director of National Intelligence. Those include the CIA, which collects and analyzes foreign intelligence to inform policymakers. The NSA, which mostly monitors foreign information systems for signals intelligence, collecting data including cell phone and email traffic for intelligence and counterintelligence purposes and sometimes sweeping up information about Americans in the process. The Defense Intelligence Agency, which focuses on foreign military intelligence. The National Geospatial-Intelligence Agency, which charts and maps the physical earth and human activity for national security purposes. And the National Reconnaissance Office, which designs, builds, launches, and maintains US spy satellites.
Then there's the FBI's counterintelligence unit, which helps protect the American homeland from foreign intelligence operations here. For the 2015 fiscal year, the White House requested sixty billion dollars for two programs that fund all of these agencies combined, but that's known as the black budget because the breakdown beyond that top line is classified. Earlier this year, to help Democrats introduce legislation that would force the White House to reveal more details about how that funding is actually spent.
Knowledge Check
Prepare for the quiz by answering the following questions.
4.6 The Intelligence Process - A Macro Look: Who Does What for Whom?
Required Reading
Read Lowenthal's Chapter 4: "The Intelligence Process - A Macro Look: Who Does What for Whom?" in Intelligence: From Secrets to Policy.
As you read this chapter 4, do some critical thinking and ask yourself:
- The intelligence process as defined by the US intelligence community has five steps, and the author adds two. What is your evaluation of these steps? Are they the best combination and order of steps, or can you think of alternatives? Why does the author add two steps? Why are his two additional steps not standard in US intelligence community practice and doctrine?
- The author notes that the training and the mind-sets of analysts are important. How might analysts from different professional and academic backgrounds see things differently? How might a former military person see things differently from a civilian? How might a geographer see things differently from a political scientist or historian or an economist, etc?
- The US practices of dissemination have evolved over time. Why have they evolved as they have? What agency or agencies are advantaged or disadvantaged through this method. Can you think of better ways to disseminate the intelligence?
Analyst Training and Education
Reference the second bullet above on analyst's training; the National Geospatial-Intelligence Agency (NGA) puts great emphasis on training their analysts. As an example, NGA manages the GEOINT Professional Certification Program (GPC), part of a broader initiative to professionalize the Department of Defense Intelligence Enterprise workforce. Certifications are based upon a set of competencies associated with the knowledge and skills necessary to successfully execute the mission. Earning a GPC credential demonstrates proficiency in the content areas in the essential body of knowledge for that certification. These certifications promote interoperability across the GEOINT community and enable practitioners to demonstrate proficiency in the competencies that are common to their specific geospatial intelligence discipline. For additional information about this program, visit GEOINT Professional Certification [67].
GPC credentials are categorized as either proficiency at the fundamental level or within a specific GEOINT discipline or tradecraft. According to the GPC essential body of knowledge, core competencies at the fundamental level are:
- Demonstrate understanding of processes and techniques used in GEOINT problem-solving
- Understand source evaluation principles, tasking procedures, and collection requirements
- Understand GEOINT collection and production requirements
- Understand basic principles and techniques used to evaluate the utility and quality of geospatial data
- Understand the principles of Geographic Information Systems to display and analyze geospatial data
- Understand standards, policies, practices, and authorities governing GEOINT
- Understand the distribution of intelligence and data to mission partners, organizations, and individuals to support the GEOINT mission
- Understand how intelligence issues impact national and defense GEOINT mission priorities
- Understand the National System for Geospatial Intelligence and Allied System for Geospatial Intelligence
- Understand quality assurance in processing and exploiting GEOINT
- Understand strategies, techniques, and technologies used to identify, acquire, and filter sources of information
- Understand the policies and procedures involved with classification, control, and disclosure/release of information, intelligence, and data.
The U.S. Geospatial Intelligence Foundation (USGIF) is a non-profit organization dedicated to promoting the geospatial intelligence tradecraft. USGIF supports academic programs and accredits colleges and universities that offer geospatial intelligence certificate and degree programs. A list of accredited schools and the programs they offer can be found here: USGIF Academic Programs [68]. Penn State's program was one of the first to be offered and accredited. An article about the beginning of this program is below.
Why are multiple programs offered in geospatial intelligence? Are these programs redundant, or do they fulfill different educational functions? Going back to your critical approach, do the different cultural filters and agendas of NGA versus academic programs influence the programs?Penn State Begins First Online Geospatial Intelligence Program
Wednesday, June 20, 2007
University Park, Pa. — In light of a greatly increased demand for qualified analysts in the intelligence, defense and emergency management fields, Penn State has developed a new online certificate program in geospatial intelligence (GEOINT). The ... program is designed to provide students with the core competencies required to effectively and ethically provide geospatial analysis to key decision makers at defense, governmental, business and nongovernmental organizations. (para.1)
Rather than simply developing students' proficiency with technology, Penn State's geography faculty want to develop students' abilities in critical thinking and spatial analysis, while promoting cultural sensitivity and high ethical standards to students in the field. (para. 5)
Penn State's Geospatial Intelligence Certificate program [69] is the first online program of its kind in the nation. (para. 9)
Reference
Penn State begins first online geospatial intelligence program. (2007, June 20). https://www.psu.edu/news/university-park/story/penn-state-begins-first-o... [70]
Knowledge Check
Prepare for the quiz answering the following questions.
4.7 Collection and the Collection Disciplines
Required Reading
Read Lowenthal's Chapter 5: "Collection and the Collection Disciplines" in Intelligence: From Secrets to Policy.
As you read, do some critical thinking and ask yourself:
- Lowenthal says that, "Collection is the bedrock of intelligence…Without collection, intelligence is little more than guesswork…" Evaluate this statement considering his background and organizational placement. After you read the chapter, consider whether you agree with him or not.
- Consider the processing and exploitation imbalance. Does this apply to geospatial intelligence? Is it a problem? How might the geospatial intelligence community overcome this issue? What are the political and budgetary implications of overcoming this problem?
- On page 98, Lowenthal addresses the limitations of satellites. The author is not a geospatial intelligence expert. Evaluate his assessment, and consider how these limitations might be overcome with other techniques, technologies, systems, or processes.
- The author's coverage of Geospatial Intelligence increased substantially between editions, including an expanded section on unmanned aerial vehicles (UAVs). Many of you are practitioners of GEOINT...did the author get it right?
Knowledge Check
Prepare for the quiz answering the following questions.
4.8 Analysis
Required Reading
Read Lowenthal's Chapter 6: "Analysis" in Intelligence: From Secrets to Policy.
As you read this chapter, do some critical thinking and ask yourself:
- Lowenthal says that while collection is the bedrock of intelligence, analysis is the mainstay of the process. If this is so, then why is there such a resource imbalance between collection and analysis?
- Pay close attention to the discussion of analyst training. Are there special issues for the training of geospatial analysts versus other analysts? Consider the difference between education and training. The NGA College and Penn State were able to work together because they recognized that while the NGA College trains analysts, academic programs such as this one educate analysts. What is the difference, and why are both education and training important? Do other analysts need both education and training?
- Traditional imagery analysis included the disciplines of remote sensing and imagery interpretation. Geospatial intelligence leverages all aspects of geographic information science including remote sensing, GIS, GPS, and cartography. Does Lowenthal's traditional discussion of IMINT reflect this? How does this impact geospatial analysis and dissemination?
- How does analytical stove piping affect geospatial intelligence analysis? What are some solutions to overcome this issue?
Knowledge Check
Prepare for the quiz answering the following questions.
4.9 Summary and Final Tasks
Summary
We had a lot of reading this week. Understanding the basics about the US intelligence community is an important foundation so you can ultimately understand where geospatial intelligence fits into the intelligence community and contributes to national security. Our six chapters covered:
- the definition of intelligence as articulated by Lowenthal;
- the evolution of the US intelligence system;
- the layout of the US intelligence community and the functions of the major agencies;
- the intelligence process of: requirements, collection, processing and exploitation, analysis and production, dissemination and consumption, and feedback;
- the bedrock of intelligence-collection;
- the mainstay of the process-analysis.
Remember that what you read was written by a national security insider who is a veteran of the CIA. His personal history and experience give him a particular cultural filter. Your challenge as a critical thinker is to recognize from where he comes, consider alternative approaches, and keep an open mind. Nevertheless, the US national security intelligence community is the most sophisticated, best funded, and far reaching intelligence establishment on the planet. Thus, it does rate our careful study and understanding even as we focus in on geospatial intelligence in both national security and other applications.
Final Tasks
Your last challenge this week is to take Lesson 4 - GRADED Quiz (#3) on this week's readings.
Deliverable: Lesson 4 - GRADED Quiz (#3)
Return to Lesson 4 in Canvas. Look for the Lesson 4 - GRADED Quiz (#3), where you will find the twenty-five-question quiz on this week's readings. Each question is worth two points. You will have unlimited time, and it is open book, but be forewarned. This is a tough quiz. To do well, you must have read and studied the readings.
Before you move on to Lesson 5, double-check the Lesson 4 Checklist [71] to make sure you have completed all the required activities for this lesson.
Looking Ahead
I hope you like Lowenthal's book, because our next lesson is another reading week. Now that we understand the basics of how the US intelligence community works, in our next lesson, we are going to consider:
- the role of the policymaker;
- the legacy of the Cold War;
- the new intelligence agenda;
- ethical and moral issues in intelligence;
- intelligence reform.
But first, you have to get through the Lesson 4 - GRADED Quiz (#3) successfully. Good Luck!
Lesson 5: GIS and T and National Security
5.1 Overview
This lesson continues our broad look at the US intelligence community, focusing in on the role of policymakers, the evolution of priorities, and thus the organization of the intelligence community, and, quite importantly, ethical issues in intelligence. We will also zero in on the role and place of GEOINT in the community. This is another heavy reading week, with more of those quizzes you are learning to love. Once again, we are going to leverage the knowledge and experience of Mark Lowenthal and his textbook Intelligence: From Secrets to Policy. We are also going to examine NGA's foundational doctrinal manual: NGA Publication 1.0 Geospatial Intelligence (GEOINT) Basic Doctrine, published in April 2018 (link listed under Required Readings). Government doctrinal publications are authoritative in that they provide official definitions, delineate roles and responsibilities, and articulate techniques, procedures, and processes. Much of the underlying authority for doctrine comes from US federal law, as codified in the US Code. Recognize, however, that in the US, "doctrine is not dogma." In other words, doctrine is a guide that coordinates the efforts of agencies and provides guidance on how to conduct business, but operational variation from doctrine is allowed as long as one does not violate the law and is successful.
My teaching approach this week is the same as last week in that you have to read four chapters from the textbook and scan NGA Pub 1.0. I want you to read the book in conjunction with the online lesson. I will provide a brief pre-read commentary for each chapter that asks you to contemplate several questions as you read and provides some other perspectives for comparison. At the end of this module you can take Lesson 5 - GRADED Quiz (#4) one time for your lesson grade.
I suggest that if you have the time, you read the rest of Lowenthal's book. The chapters I did not assign on Counterintelligence, Covert Action, Oversight and Accountability, and Foreign Intelligence Services make for fascinating reading.
Lesson Objectives
At the end of this lesson, you will be able to:
- identify the relationship of policymakers and intelligence professionals (Chapter 9);
- recognize the impact and legacy of the Cold War on the US intelligence community (focusing on the role of imagery analysis) (Chapter 12);
- indicate examples of the new intelligence agenda in the Post Cold War/September 11 Era, and discuss the impact of new challenges on the geospatial intelligence community (Chapter 12);
- examine Lowenthal's insider views on "Ethical and Moral Issues in Intelligence" (Chapter 13);
- recognize efforts at intelligence reform, focusing on possible impacts on the geospatial intelligence community (Chapter 14);
- recognize the evolving role of the National Geospatial Intelligence Agency (NGA) in the context of the overall role of geospatial intelligence in support of US national security (NGA Pub 1.0).
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
5.2 Checklist
Lesson 5 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 5:
- Work through Lesson 5 in this website.
- Read NGA Fact Sheet [72]. (Required)
- Read NGA Publication 1.0: National System for Geospatial Intelligence: Geospatial Intelligence (GEOINT) Basic Doctrine [73]. (Required)
- Read the following chapters from Lowenthal's Intelligence: From Secrets to Policy 9th edition (Required text):
- Chapter 9: The Role of the Policy maker
- Chapter 12: The Intelligence Agenda: Transnational Issues
- Chapter 13: Ethical and Moral Issues in Intelligence
- Chapter 14: Intelligence Reform
- Read NGA 2015 Strategy [74]. (Required)
- View Episode Three, Chapter One of the Geospatial Revolution Series (embedded on page 5.3).
- Participate in the "Impacts of the Cold War on US intelligence community?" UNGRADED Discussion Forum.
- Participate in the "Ethical issues?" UNGRADED Discussion Forum.
- Participate in the "Do efforts at reform have an impact?" UNGRADED Discussion Forum.
- Take Lesson 5 - GRADED Quiz (#4) in Canvas.
5.3 The Role of GEOINT and the NGA
It is important that you understand the doctrinal underpinnings of the premier GEOINT organization in the US and perhaps the world.

Required Reading
- Read the NGA (National Geospatial-Intelligence Agency) fact sheet [72].
- Read NGA Publication 1.0 National System for Geospatial Intelligence: Geospatial Intelligence (GEOINT) Basic Doctrine (STUDY the Introduction on pages 5-6). The reading can be accessed from the Lesson 5 Checklist [75]. As you read NGA Pub 1.0, do some critical thinking and ask yourself:
- Why does NGA define GEOINT as it does and what is NGA's agenda in establishing this definition and its role?
- How does the NGA view differ from Lowenthal's (a CIA type) coverage?
- How might a Geographic Information Science practitioner conducting GEOINT for other than national security purposes (disaster preparedness/response, public health, business intelligence, etc) see the definition and application of GEOINT differently?
- To improve your understanding of the NGA and the strategy it is charged with implementing, scan the NGA 2015 Strategy. The reading can be accessed from the Lesson 5 Checklist [75].
To get a flavor for the topic, please take a few minutes (4:46 running time) to view Episode Three, Chapter One of the Geospatial Revolution Series.
Video: Geospatial Revolution / Episode Three, Chapter One: Mapping the Road to Peace (4:46)
KEVIN POMFRET: Right now, you can track people with their knowledge or without their knowledge. But, is that really an invasion of privacy or is that just new technology?
MATT O'CONNELL: It's important that we be able to look at any place in the world because if trouble strikes, our government has to deal with the situation.
LETITIA LONG: We are the eyes of our nation, if you will. You need geospatial intelligence to target bad guys.
JAN VAN SICKLE: Mapping to some degree has always been driven by conflict, shall we call or war.
ON-SCREEN TEXT (SET TO MUSIC): In the early 1990s, the Socialist Federal REpublic of Yugoslavia broke apart along ethnic lines. War engulfed the region and the central republic of Bosnia-Herzegovina became a killing field.
UNKNOWN NEWS ANCHOR: In the face of the Bosnian Serb Offensive, another Muslim Enclave Falls. Crisis in the Balkans.
UNKNOWN NEWS ANCHOR: The shelling continued for a second day.
WESLEY K. CLARK: A line of siege was established on the hills around Sarajevo. There are snipers shooting people. Tens of thousands of people were killed.
IRV BUCK: In Bosnia and Herzegovina, we had three separate groups. You had the Croatians. You had enclaves of Serbs. nd you had enclaves those Muslims. It was real mess. Finally, the West decided had to it had to iron this situation out by cutting up the country. So, this is what the Dayton Accords were all about.
IRV BUCK: We had to figure this out so that everybody gets a fair shake here.
ALIJA IZETBEGOVIC: I believe that he did not last for long.
IRV BUCK: And the only way to do that was really geospatially. We brought in this thing called PowerScene. We took digital translation data and we overlaid it with imagery. They have joystick. You can fly over the train. Back down into the valley. We were able to get them to agree that, yes, this is a majority Muslim village, or this is a majority Serb village.
WESLEY K. CLARK: Garage door was an isolated enclave, which was populated by Muslims. The Bosnian Muslims wouldn't give up this piece of ground. They demanded secure access to it. And the question is, where would the lines be drawn.
RICHARD JOHNSON: Eventually the solution was to build a road to open a corridor to them. We used PowerScene to fly a route over the mountains that was far enough away from the Bosnian Serbs that the traffic would not be intercepted or shot at.
JAN VAN SICKLE: We needed a wider corridor. And we had to demonstrate that to the president of Serbia.
WESLEY K. CLARK: Milosevic was smart but he wasn't a field soldier. He never walked that terrain. Well, can't we make this more narrow? Why so many kilometers? Well, you can see right here, Mr. president. Here's the mountain top on one side. Here's the mountain top on the other. You can't draw a line down the side of a hill like this and have it defensible. They have to have the high ground on either side of this valley. He could see this with real terrain. Ultimately, he couldn't beat the argument and we had our road and that's what we needed.
RICHARD JOHNSON: This was the first successful use of deployable digital technology in diplomatic negotiations.
SLOBODAN MILOSEVIC: For the great efforts, the United States invested.
RICHARD JOHNSON: It was hugely satisfying and emotional to know that we helped in the war.
PRESIDENT BILL CLINTON: After nearly four years of 250,000 people killed, the people of Bosnia finally have a chance to turn from the horror of war to the promise of peace.
Then read the NGA fact sheet above and complete the required readings. If you are really enthusiastic, look over Joint Publication 2-03 Geospatial Intelligence Support to Joint Operations (a link to the Optional Reading is provided below).
Optional Reading
Joint Publication 2-03 Geospatial Intelligence Support to Joint Operations [78] (PDF). Recall that NGA is both a DoD combat support agency and a national intelligence agency. Read this article if you are interested in learning more about the role of GEOINT within DoD.
Knowledge Check
Prepare for the quiz by answering the following questions.
5.4 The Role of the Policy Maker
Lowenthal notes that most authors and intelligence experts do not consider the policy maker to be part of the intelligence process. Lowenthal disagrees, and that is why he adds two stages to the process. Remember that, according to Lowenthal, "Intelligence refers to information that meets the stated or understood needs of policy makers and has been collected, processed, and narrowed to meet those needs." The needs of policy makers drive intelligence priorities, which will drive the intelligence process, and, very importantly, drive resource allocation. Note also the problems that can arise when the "understood" needs of policy makers are unclear or contentious. To put this another way, the needs of the client policy maker drive the mission and activities of the geospatial intelligence professional. A clear understanding of the client's requirements (which may change over time) is essential to the successful intelligence enterprise.
Required Reading
Read Lowenthal's Chapter 9: "The Role of the Policy Maker" in Intelligence: From Secrets to Policy.
As you read, do some critical thinking and ask yourself:
- Given the author's background and focus on government, is his analysis applicable and appropriate to other intelligence applications in other communities such as disaster preparedness (FEMA, the American Red Cross, etc.), international humanitarian aid and disaster response (UN, International Federation of the Red Cross, other NGOs), the business community, etc.?
- Are there alternative discourses that might define the role and relationships of policy makers and the intelligence community differently?
Now consider how this discussion applies to GEOINT. According to NGA Pub 1.0:
GEOINT can also create a Common Operational Picture (COP) of a specific area by effectively using multiple and advanced sensors, multiple types of data and information (including operations, planning, logistics, etc), as well as multiple intelligence disciplines (INTs) to present a comprehensive visual depiction. This capability provides many advantages for the warfighter, national security policymakers, homeland security personnel, and IC collaborators by precisely locating activities and objects, assessing and discerning the meaning of events, and providing context for decision makers.
In short, GEOINT provides innovative, versatile solutions for meeting today's demanding intelligence requirements and predicting tomorrow's future threat environment. (NGA Pub 1.0 pages 5-6, emphasis added)
NGA Publication 1.0 Geospatial Intelligence (GEOINT) Basic Doctrine
This passage points out that NGA provides GEOINT products and support to a wide customer base beyond federal government policy makers as envisioned by Lowenthal. NGA customers also include warfighters (military commanders and their forces engaged in planning and operations), the homeland security community (focused on both terrorism and disaster planning and response—i.e., all hazards preparedness and response), and other domestic and international partners (allies).
Knowledge Check
Prepare for the quiz by answering the following questions.
5.5 The Intelligence Agenda
Required Reading
Read Lowenthal's Chapter 12: "The Intelligence Agenda" in Intelligence: From Secrets to Policy.
As you read, do some critical thinking and ask yourself:
- The Post Cold War/Post September 11 era changed the focus of US foreign policy and thus the needs of policy makers. What are the implications for GEOINT?
- The era of the Global War on Terrorism has been succeeded by a focus on possible conflict with “near peer competitors” such as China and Russia. What are the implications for GEOINT?
-
Compare and contrast Lowenthal’s priority changes between the 8th and 9th editions. Why have these priorities changed, and what is the impact on GEOINT
Note how Lowenthal’s priorities changed in Chapter 12 between the eighth and ninth additions. He promoted Heath Issues presumably due to the COVID 19 pandemic and concerns over future pandemics. He also made Climate Change its own category. While there are still "climate deniers” out there, the position of the US Government in the Fourth National Climate Assessment [79] is:
This assessment concludes, based on extensive evidence, that it is extremely likely that human activities, especially emissions of greenhouse gases, are the dominant cause of the observed warming since the mid-20th century. For the warming over the last century, there is no convincing alternative explanation supported by the extent of the observational evidence.Highlights of the Findings of the U.S. Global Change Research Program Climate Science Special Report (2017).
The assessment goes on to indicate there will be serious issues for US national security due to global climate change. I’ll let you speculate on why he dropped Peacekeeping Operations from the list.
| 8th Edition Intelligence Priorities (2019) |
9th Edition Intelligence Priorities (2023) |
|---|---|
| Cyberspace | Cyberspace |
| Terrorism | Terrorism |
| Proliferation | Proliferation |
| Narcotics | Health Issues |
| Economics | Climate Change |
| Demographics | Narcotics |
| Health and Environment | Economics and Energy |
| Peacekeeping Operations | Demographics |
| Support to Military | Support to Military |
Knowledge Check
Prepare for the quiz by answering the following questions.
5.6 Ethical and Moral Issues in Intelligence
Required Reading
Read Lowenthal's Chapter 13: "Ethical and Moral Issues in Intelligence" in Intelligence: From Secrets to Policy.
As you read, do some critical thinking and ask yourself:
- Some people (many of them in academia and not a few at Penn State) have serious issues with the morality of conducting secret intelligence activities and covert actions. Why would some citizens have problems with the conduct of the US intelligence community? As you consider this, reread the Penn State news release from 2007 [70]. Does the press release in any way relate to the discussion of ethics and "good" decision making? What does it tell you about the concerns of the Penn State faculty that had to approve the program?
- Lowenthal addresses the following general moral questions:
- Secrecy
- War and Peace
- Ends versus Means
- The Nature of the Opponent
- National Interest
- Changes in Ethics and Morals
- Consider what other general moral questions a different author with a different background might have asked, or how they might have addressed these issues differently. What are specific issues for the GEOINT professional and community for each of them? Are the issues the same for the CIA, NSA, and NGA, or do different issues arise?
- GEOINT professionals seldom deal directly with HUMINT and the related activities of covert action, assassination, and rendition and torture. Yet, GEOINT activities might well support or enable such activities. How do you feel about this personally, and what are the responsibilities, if any, of GEOINT professionals relative to these difficult issues?
- How are the analysis issues similar or different for the GEOINT professional and community versus other elements of the intelligence community?
- Do these ethical and moral issues apply to GEOINT professionals outside the national security intelligence community (e.g., the International Committee of the Red Cross ICRC, the United Nations, non-governmental organizations)?
Video: Revolution in Intelligence Affairs Future Strategic Environment (11:23)
Dr. Joseph Czika, Senior Program Officer, ICSB, NASEM: Welcome to the colloquium entitled revolution in Intelligence Affairs the Future Strategic Environment. My name is Joe Czika. I am a staff member of the Intelligence Community Studies Board of the National Academies of Sciences, Engineering and Medicine. This is the 15th colloquium in the partnership of the Academies with the Office of the Director of National Intelligence. You will notice that this is the third of a series of colloquia on the Revolution in Intelligence Affairs. I refer you to the ICSB website for information on the prior to colloquia and to access the videos of those presentations. Before introducing the representatives from the sponsoring organizations, I want to make a few administrative announcements. This is an unclassified meeting. This colloquium is being held as a virtual colloquium. As is our custom. This colloquium is being video recorded and the recordings will be available in the near future. Check the ICSB website for notice of their availability. Please note, at the bottom of your screen, or somewhere on your screen, is a feature that allows you to ask questions for our panel, both during the three individual panels and the grand panel at the end of the program. In those questions, please identify yourself and clearly state your question and whether it should be directed at any specific speaker or the entire panel.
You can submit those questions anytime during the colloquium. Also available to you is the colloquium program or agenda, complete with speaker biographical information. Lastly, I would like to thank Dr. Anthony Vinci for his invaluable support for this series of colloquial. To extend a welcome from the office of the Director of National Intelligence is Mr. Dan Flynn. He's the director of the Net assessments in the ODNI. In this position, he is responsible for developing forecasts and comparative assessments to identify emerging intelligence challenges and opportunities for U. S. Intelligence capabilities. Prior to his current assignment, Mr. Flynn was the Director of the Global Security Program for the National Intelligence Council's Strategic Futures Group. Prior to joining the NEC, Mr. Flynn served as the chairman of CIA's senior analytics service. Mr. Flynn is a distinguished graduate of the National War College, where he earned a master's degree in National Security Strategy. He also earned a BS. Degree in aerospace engineering from Boston University. Dan, thank you for your introduction and welcome.
Mr. Dan Flynn, Director, Office of IC Net Assessment, ODNI: Thank you, Joe, for that kind introduction. I want to thank the National Academy of Science and the IC Studies Board, as well as all our speakers today for supporting our event. To give everybody a little more context of why we're here. As Joe said, I'm from the Office of Director of National Intelligence, specifically the Policy and Capabilities Directorate, and it's the responsibility of our directorate to articulate a path forward for the intelligence community. And we do this also by investing in strategic bets to address enduring challenges as well as potential opportunities for the IC looking forward what they need to prepare for in the future. Before we can prepare for the future though we need to understand what that future is that we're preparing for. And that's the job of my team and ICNet assessments. To think about intelligence, environment ten to 20 years from now and identify those emerging challenges and opportunities for the IC to inform our senior leadership so they can make better decisions about what are the resources and investments we need to make as a community to be prepared for that future. Our role is similar to the Pentagon's office in that assessment that many of you may be familiar with that was set up by the late Andy Marshall back in the 1970s.
Dr. Joseph Czika: They looked at the future security environment to inform the senior DoD leadership on the changes that were occurring that the DoD needed to prepare for part of that work. They looked at the so called revolution in military affairs, which looked at was it possible to have technological innovation, organizational adaptation and doctrinal concept improvements to create revolutionary changes in military capabilities. Many now are suggesting that there isn't on the verge of a revolution intelligence affairs. And so, hence purpose of this colloquium. And as Joe mentioned, we've had a series of these. This is the third in the series. Our first was last April when we talked about technology drivers that might shape a revolution, intelligence affairs, things like artificial intelligence and machine learning and the explosion of information that we'll be seeing from the Internet of things and how that's going to change the conduct intelligence. Our second colloquial was in late June, which we talked about organizational implications of revolutionary intelligence affairs and how the IC might have to react to that. Today's colloquium is looking at drivers in the strategic environment and how that may shape the future as well as shape intelligence. The panels today will also discuss kind of looking back over the series, what are the key implications for the intelligence community going forward.
Mr. Dan Flynn: Now, many of you may be wondering why we're going outside the community to have these conversations. Well, history has shown that many organizations, often when they look within themselves, fail to see the revolutionary changes that are occurring on the outside. And so it's important that we speak with some people who have been thinking deeply about a lot of these issues. And luckily for us, we have a great panel series of panels of experts, many of whom I've had the privilege to work for or work with during my career. So, I'm really looking forward to what they come up with today and what insights they have for us. And I look forward to working with them again and engaging on this topic some more in the future. So, with that, my thanks to everyone and I'll hand it back to Joe. Thank you.
Dr. Joseph Czika: Thank you, Dan. Now to extend a welcome from the National Academies of Science, Engineering and Medicine is Dr. Scott Weidman. He's the deputy executive director for the Division on Engineering and Physical Sciences of the National Academy of Sciences. Prior to that, he served as the Director of the National Research Council's Board on Mathematical Sciences and analytics, and he has held many leadership positions in the NRC. He holds a doctorate and master's degree degrees from the University of Virginia and a bachelor's degree in Mathematics and Material Science from Northwestern University. Scott, thank you for your welcoming comments.
Dr. Scott Weidman, Deputy Director, DEPS, NASEM: Thank you, Joe. And thank you, Dan. As Joe said, I just want to offer a welcome to all of you for coming to this, especially if you haven't interacted with the National Academy of Sciences, Engineering and Medicine in the past. We are very energized to play a role as a kind of a matchmaker between the intelligence community and the broader world of science, engineering and medicine. We are not part of the government. We are a nonprofit that primarily serves to provide advice to the government. And we're a fairly large organization. We have at any given time, there's approximately 500 or 600 committees of experts serving pro bono to help plan activities, conduct studies, or oversee activities like this one. And we collectively put out about 200 reports a year. Most of those are public in the public domain, some fraction is classified and more limited. So, we cover a wide range of topics. And the main reason that this activity of our Intelligent Community Studies Board, which is the parent organization for this forum today, was set up to establish that connection between the IC and a broader science and technology communities. So, we're very interested in doing what we can to help.
Dr. Joseph Czika: We're very sensitive to the fact that, as Dan said, a lot of this could be done behind within the community itself in a more closed session. But there is a lot of benefit to reaching further, trying to see over the horizon, trying to understand different perspectives that can maybe forced all surprise. So, that's all i wanted to say. Welcome very much to all of you. We look forward to today's event and we look forward to a long connection between our communities. Thank you!
Dr. Joseph Czika: Thank you, Scott. As you're aware, we're departing from our normal practice of presenting individual speakers for today's colloquium. Rather than the usual five speakers speaking individually, we have great 12 experts along with our moderator talking to us via panel sessions. In each session, each panel member may open with a statement, no longer than about 10 minutes. When all panel members have completed their statements, the general discussion will be moderated by Anthony Vincy. At the conclusion of the third panel discussion, he will moderate a general discussion among all the panelists from all three sub-panels. You can submit your questions at any time using the smartsheet available on your screen.
We know from earlier readings that one of the mortal sins in the intelligence business is to politicize intelligence. Consider the perspective of a former CIA analyst in assessing the track record of a former Secretary of Defense (who you will recall controls about 80% of the intelligence assets on a daily basis, and is a major consumer of intelligence products).

Optional Reading
ON THE POLITICIZATION OF INTELLIGENCE [82]
Tomes, Robert. "On the politicization of intelligence"; War on the Rocks, September 29, 2015
Optional Reading
The Politics of Intelligence and the Politicization of Intelligence: The American Experience [83] (Hastedt, Glenn).
Abstract:
The relationship between intelligence analysis and policy decisions is a contentious one with both policymakers and intelligence analysts frequently expressing frustration over its underlying dynamics and with each faulting the behavior of the other. This article examines one aspect of this relationship, the manner in which intelligence analysis can become politicized. Rather than view politicization as an aberration it is treated here as a normal feature of intelligence analysis. A typology of politicization organized around the concepts of hard and soft politicization is presented and illustrated with historical examples from the American experience with intelligence analysis.
Knowledge Check
Prepare for the quiz by answering the following questions.
5.7 Intelligence Reform
Reading
Read Lowenthal's Chapter 14: "Intelligence Reform" in Intelligence: From Secrets to Policy.
As you read, do some critical thinking and ask yourself:
- Do the efforts at intelligence reform have significant impact on GEOINT, or are they targeted elsewhere?
- The issue of stovepiping is very significant. By concentrating all GEOINT functions in the NGA, has the intelligence community deprived other agencies of opportunities to leverage GEOINT for their areas of interest and expertise?
Knowledge Check
Prepare for the quiz by answering the following questions.
5.8 Crisis in Atlantica
Atlantica Scenario Background
Listen
Listen to two simulated on-the-ground news broadcasts about the crisis in Atlantica:
Why Atlantica and Why Now? [84] (6.6 Mb mp3 file)
(Transcript of Why Atlantica and Why Now?) [85]
Fighting in the South-Central Highlands of Atlantica [86] (8.1 Mb mp3 file)
(Transcript of Fighting in the South-Central Highlands of Atlantica) [87]
INTELLIGENCE ESTIMATE
REPUBLIC OF ATLANTICA
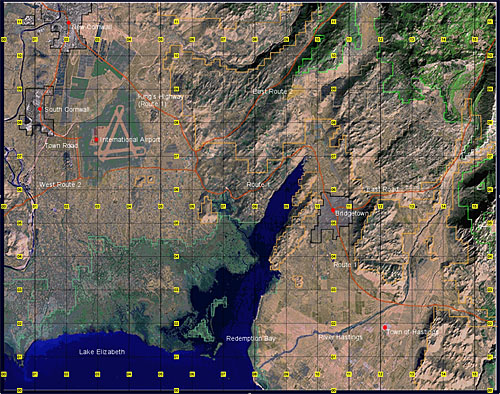 [88]
[88]
Background
- Atlantica is a small pro-Western Eurasian republic. Since gaining their independence from Great Britain in 1985, its people had been living in relative harmony and have enjoyed a fair degree of economic prosperity. Their prosperity was based on a thriving tourist industry, burgeoning trade, and a close relationship with the United States Government and the U.S. Air Force (USAF). The USAF has an important forward operating base and airfield located in the northern part of the country that shares a runway with the international airport. The political and economic core of Atlantica is the capital city of Bridgetown (AKA Bridgeport). The Southern Administrative Region is administered from the main southern city of Southport.
- This prosperity, however, concealed the underlying political and cultural divisions in the Republic between the ruling majority population in the northern lowlands and its southern highland minorities with their own historical and intensely tribal traditions. Though racially identical, Atlanticans are distinguished by culture, religion, and ethnicity, and separated by artificial political, economic, and educational barriers. This separation is in part due to differences in geography: the northern half has wide plains and fertile fields while the south is mountainous.
- North Atlanticans have long enjoyed political and economic advantages in the Republic. Atlantican government leaders and politicians, despite their pro-democracy claims, cling to an electoral system that only allows traditional land owners the right to vote, with the result that the majority of seats in the Atlantican Parliament are held by Northern representatives. The Constitution of the Republic excludes minority rights by imposing restrictions on land ownership that result in the disenfranchisement of Southerners. A few Southerners have been able to gain a degree of social status by entering into business arrangements with ethnic Northerners or by marrying into Northern families, though the latter is frowned upon socially and actively discouraged by the Government of the Republic of Atlantica.
- The long term trend, however, is a slow decline in Northern privilege and increasing Southern representation in the Atlantican Parliament, with a concurrent rise in ethnic and political tensions. The last election in 2009 led to the formation of a minority government. The coalition is led by the long-time ruling Atlantica Renewal Party (ARP) (35% of the popular vote) together with the Conservative Party of Atlantica (CPA) (30%), leaving the ethnic southern New World Party (NWP) in opposition with 35% of the vote. Southern professionals have found themselves out of work or passed over for promotion in favor of their ethnic Northern colleagues. The Republic's security forces, comprised of a small British-trained and US-equipped Army (Army of the Republic of Atlantica) and a National Police Force, are dominated by a Northern officer corps.
- As long as its economy generated some wealth for all its citizens, the Republic was at relative peace and its government stable. While poor and disenfranchised by the North, South Atlanticans had been enjoying increasing prosperity as a result of recent discoveries of valuable mineral deposits in the highlands.
- With increasing prosperity and education, Southerners in Atlantica began agitating for more political freedoms, demanding democratic reforms and redress of the basic inequities in Atlantican society. Key demands included:
- Equity in government and law enforcement hiring,
- Greater local administrative autonomy for predominantly Southern areas, and
- Repeal of constitutional restrictions on Southern land ownership.
- At first the Atlantican Government ignored these demands. This resulted in a popular campaign of non-violent agitation within the Southern community including rallies and protests that garnered international support and wide publicity for the Southern cause. General strikes in Southern mines in September 2011 organized by the New World Party brought the regional economy to a standstill. The Government reacted by mounting a public information campaign and appointed several government committees "to study the legitimate grievances of the Southern minorities." NWP and Southern tribal leaders denounced these actions as little more than window-dressing.
- Strikes in the mining industry and increasing communal violence prompted a robust response by the Minister for National Security William H. Barfield II. Barfield is a prominent hard-line figure in the CPA, a favorite at Atlantican political rallies, and is extremely popular among the Army and National Police rank and file. Under attack by his critics in Parliament, Atlantican President Anderson appointed Barfield Minister in 2010 to appease Atlantican conservatives and reorganized all security, police, and military forces in the Republic under the Ministry for National Security (MNS).
- The MNS under the 2010 Security Reform Act changed the position of the national security advisor to the President to an executive ministerial position with full authority over the Atlantican security apparatus "in consultation" with the office of the President. The 2010 Security Reform Act prompted many observers in the United States to decry the emergence of a new "national security state" in the Republic. Atlantican spokesmen responded that these changes merely "streamlined" the Atlantican security apparatus. They claimed that the United States Government and its air base "benefit directly from this enhanced and rationalized security infrastructure."
- Since 2010, there has been little political or economic improvement since the Atlantican government adopted its hardline policies. Many important Northern-owned mines remained closed in the South. Some local populations are reduced to subsistence livelihoods. There are occasional reports of famine in some tribal areas in south central Atlantica.
- Some Southern tribesmen have taken up arms and have launched sporadic attacks against Atlantican security forces. They are actively hostile to any outsiders who enter their tribal areas. Government spokespersons refer to these armed groups as "bandits and criminals" who will be "dealt with severely." In retaliation, tribesmen have attacked some Army patrols with landmines and IEDs.
- Despite the hostility of some traditional tribal leadership, a few humanitarian aid organizations have been successful in entering Southern communities to deliver food aid and medical care. The Government of the Republic of Atlantica and the Army support these efforts reluctantly and only because of pressure from the international community. Some northern Atlanticans believe incorrectly that these aid agencies are sustaining and widening the conflict.
- In April 2013, a 6.8 degree magnitude (Richter scale) earthquake struck south central Atlantica with devastating results. Initial estimates by international aid workers already in the area count at least 2,000 people killed outright and at least another 5,000 injured and 150 missing. Many villages and hamlets in the area have suffered severe damage rendering many local structures uninhabitable. More than 10,000 people are homeless. Many local schools are damaged and the few hospitals in the region are significantly damaged and operating at only 40% capacity. There is also major damage to the dam that retains a regional reservoir. Large amounts of water are pouring from this dam and there is some danger of flooding. Persistent aftershocks continue to afflict the area, causing wide-spread concern.
- Because its own emergency management capabilities have been overwhelmed by the magnitude of the disaster, the Government of Atlantica has requested humanitarian assistance from the United States for its earthquake-stricken area. As the United States Government (USG) considers Atlantica an important strategic ally, the U.S. government is organizing a quick response to the humanitarian crisis in part to prevent the situation in the country from becoming more unstable. Atlantican and American planners have divided the afflicted region in South Atlantica into several Areas of Responsibility (AORs). The Atlantican Government has asked the United States to be responsible for organizing and delivering relief efforts to the Atlantican central highlands
- The Atlantican Government has expressed its gratitude for this humanitarian assistance as the scale of the disaster has overwhelmed its own emergency response capabilities. However, the government is either ambivalent or hostile to external efforts to mediate the internal political crisis and will only accept a limited number of military personnel to operate on its territory. The government welcomes civilian aid workers and emergency personnel and will provide security.
Government Forces
- United States: Given the simmering conflict in the disaster area, the United States has requested and been given permission to position a small but capable Joint Special Operations Task Force (JSOTF) Quick Reaction Force (QRF) inside Atlantican territory at the USAF facility to provide additional security for U.S. and other humanitarian personnel should the need arise. The U.S. airfield will also serve as a staging area for disaster relief efforts.
- Atlantican Forces: Elements of the 2nd Bn (SOC) of the 1st Army of the Republic of Atlantica (ARA) are conducting security operations in the AOR. Uniform: Standard US pattern BDUs; SOC ARA does not wear unit insignia. ARA Emblem: Winged "Sword of the Republic" on OD Background. Equipment: US made small arms; M4A1 is the weapon of choice. Significant presence of armed and unarmed Ministry of National Security operators in civilian dress, distinguished only by MNS documentation/identity cards and two-way radios. MNS operators sometimes observed with MP5s. MNS emblem: "Sword of the Republic" on a red background.
- The United Kingdom has a small operations and security contingent at the US Airbase.
Opposition Forces
- Small numbers of armed tribesmen and sympathizers are resident in the AOR. Uniform: Tribesmen wear civilian dress. Weapons: small arms, mostly former Eastern-block or captured ARA equipment, some capability for manufacturing bombs, landmines, and improvised explosive devices (IEDs), no known WMD capabilities.
- Criminal gangs are known to operate in the Southern Highlands. They primarily engage in smuggling alcohol, tobacco, and gasoline. Certain organized crime elements associated with regional organized crime organizations engage in smuggling drugs and weapons, as well as participating in human trafficking.
Neutral Elements
- IOs/NGOs: Some International Red Cross and additional NGO personnel are conducting HA operations in the affected area.
- Intermediaries: The Anglican Church of Atlantica is willing to serve as an intermediary between agencies and armed groups in the AOR.
POSSIBLE COURSES OF ACTION (COA)
Government of Atlantica COA
- The Government of Atlantica will continue its effort to eliminate all armed groups and rebuild their country. It is expected to be cooperative with U.S. forces. However, U.S. forces can expect ARA and security forces to resist/deny any direct supervision or observation of their activities. American news services, academics, activists, and several congressional representatives have been critical of the repressive actions taken by Atlantican government and its security forces.
- A U.S. effort to moderate the Atlantican position and encourage long-term negotiations with the Southern community is the one source of friction between the two governments despite the natural disaster. The Atlantican position is further aggravated by the human rights criticisms of the international press, the UN and international NGOs. The Atlantican Government is grateful, however, for their humanitarian relief efforts as long as they remain "neutral" and do not support the Southern causes.
- Two NGOs are now present in the Republic - they are International Humanitarian Action and "Rights Without Borders." (RWB). IHA is concerned with relieving the humanitarian crisis and providing aid to all citizens of Atlantica. This equitable approach has generated some conflict with Atlantican security forces on the grounds that IHA should not be, as some Atlanticans describe it, "providing food and medicine to the bandits." There is no evidence that any IHA aid has been misused.
- RWB is a vocal American and European human rights advocacy group highly critical of the Atlantican government and its security forces. It is also critical of the U.S. Government and U.S. Army for supporting Atlantican security forces. RWB activists have held regular press conferences denouncing ARA actions and have issued a number of high profile calls for a "neutral and impartial" international intervention.
- So far, the Atlantican government has tolerated the presence of this group in its effort to demonstrate its good will to the United States and the international community, but members of the hard-line CPA have called for the arrest and deportation of RWB personnel in the wake of the Director's statement. Southern civil rights advocates have received death threats from unknown Atlantican groups demanding their withdrawal. As a result, RWB is expected to extend their "protective accompaniment" and "emergency notification network" to Southern civil rights activists. This move will place U.S. civilian nationals in danger as they accompany threatened Southerners 24 hours/day and speak on their behalf to the U.S. and international media. It will also subject U.S. forces to additional public, media, and congressional scrutiny if RWB activates its network. RWB workers, regardless of nationality, may be subject to arrest by Atlantican security forces or attack by Atlantican extremists.
5.9 Summary and Final Tasks
Summary
Yet again, we had a lot of reading this week. Completion of this lesson gives you a basic understanding of issues affecting the US intelligence community. Our four chapters and additional readings covered:
- the role of the policy maker;
- the new intelligence agenda;
- ethical and moral issues in intelligence;
- intelligence reform;
- the NGA and NGS.
Remember once again that what you read in the Lowenthal book was written by a national security insider who is a veteran of the CIA. His personal history and experience give him a particular cultural filter. This lesson included a doctrinal publication, NGA fact sheets, and several articles from media outlets. Your challenge is to be a critical thinker and to use your higher order thinking skills of interpretation, analysis and synthesis, evaluation, inference, explanation, and self-regulation in utilizing the readings.
Final Tasks
Your last challenge this week is to take Lesson 5 - GRADED Quiz (#4) on this week's readings.
Deliverable: Lesson 5 - GRADED Quiz (#4)
Return to Lesson 5 in Canvas. Look for the Lesson 5 - GRADED Quiz (#4), where you will find the twenty-five question quiz on this week's readings. Each question is worth two points. Take all the time you want and feel free to use your book, but be forewarned. This is another tough quiz. To do well, you must have read and studied the readings.
Before you move on to Lesson 6, double-check the Lesson 5 Checklist [75] to make sure you have completed all the required activities for this lesson.
Looking Far Ahead........
In Lesson 7, you will be required to complete four Federal Emergency Management Administration (FEMA) online training courses. Please note that FEMA's Independent Study Exams require a FEMA Student Identification (SID) Number. If you do not yet have a SID, register for one today at FEMA Student Identification System [89]. For directions on how to request an alternative ID number, please see FEMA's Frequently Asked Questions on that same page.
Back to Lesson 5
Before we get too far ahead of ourselves, you have to get through Lesson 5 - GRADED Quiz (#4) successfully. Good Luck!
Lesson 6: GEOINT and National Security
6.1 Overview
This lesson serves two purposes. First, it completes the discussion of national security aspects of geospatial intelligence by focusing on the evolution of military applications of geographic technology. Second, it allows us to critically examine so called "revolutions in military affairs" or RMAs and consider how they do or do not impact GEOINT.
Geographic techniques have supported warfare since shortly after Cain slew Abel and mapped out his next moves. Cartographers provided increasingly sophisticated maps to support military activities, while military demand spurred the development of the discipline. This symbiotic relationship between geographic techniques and military activities was very evident in the development of the sub-disciplines and technologies of remote sensing and global positioning systems. It is somewhat less evident in the development of Geographic Information Systems (or is it?)
To get ready for this topic, watch the following video from the Geospatial Revolution Series.
Video: Geospatial Revolution / Episode Three, Chapter Two: Waging Modern War (4:18)
MIKE LEE: Geospatial intelligence, to the war fighter, is everything-- being able to lay the maps down to get you spatially oriented and then layering imagery on the top of it in a digital world so that you can see where you are and what you're doing.
LAWRIE JORDAN: With all this technology available to everyone, the real enemy is time.
OFFICER: That's a direct order. Do it now.
MIKE LEE: We have to turn inside the enemy's decision cycle. We have to be able to make the right decision faster than he does.
LETITIA LONG: If you're going to use precision-guided munitions, you need very precise coordinates.
LAWRIE JORDAN: We cannot have collateral damage to anything that's important, safe, and precious.
LETITIA LONG: We use geospatial information for route planning. Special forces need to know the best way to get into a compound and get out.
SOLDIER: There you go. Just lay it down.
MICHAEL A. HARPER: The Buckeye Program collects, processes, and disseminates high resolution terrain data. We use an electro-optical camera along with a lidar sensor. We fly it over major routes to extract detailed features of what they're going to encounter on their operation. So how high are the walls? How wide is the road? What's the depth of the ditches?
LETITIA LONG: Where are they going to land their helicopters, so they're not seen, so they're not heard? We try to give them multiple routes. Is the terrain flat so that they can land easily? We're looking for emplacements of IEDs.
[INTERPOSING VOICES]
[EXPLOSIONS AND GUNFIRE]
LAWRIE JORDAN: Improvised explosive devices, IEDs, are very difficult to detect.
MICHAEL A. HARPER: We might fly a sensor down a road at one date and time-- get a view of what that surface looks like-- and then the next day or even hours later, fly over that same route and then see what's been disturbed, where have IEDs been planted. You can monitor an area continuously to see who planted it, where did they leave from, how'd they get there.
LETITIA LONG: You have to understand the hearts and minds. Often, what is important to the people relates to the earth, and the earth's feature, and the geography of the earth.
MAN: [SPEAKING ARABIC]
MICHAEL A. HARPER: The importance of human geography and human terrain is really in a soldier understanding that aspect of his environment-- understanding the culture that he's operating in.
MAN: [SPEAKING ARABIC]
ELIZABETH LYON: Different aspects of society, culture, economic systems-- all of these pieces translate onto the physical geography.
MAN: [SPEAKING ARABIC]
ELIZABETH LYON: We look at languages that are spoken in one neighborhood versus another neighborhood. Understanding an education level-- we put it onto a map to help explain the complexities. Really fine-grained details, depending on what the commander needs.
EDWARD COPE: How can we understand what's important to them so that we're not just doing things that we think are important, but may be totally inconsistent with their value systems? That's the biggest challenge.
MICHAEL A. HARPER: We're putting them in harm's way. We owe it to our soldiers to provide them with the best information that all of this technology is capable of providing.
The American Association of Geographers [94] commissioned two books to celebrate the centennial of the organization in 2004. These books were given as gifts to each of the 5,000 participants in that year's annual meeting in Philadelphia, PA. You will be asked to read a chapter of one of these books, Geotechology, the U.S. Military, and War. This chapter is based entirely on open-source documents. The sections on current national technical systems were based on open-source information from the Federation of American Scientists. Some of the GEOINT practitioners may roll their eyes at inaccuracies. If there are any--do not tell us. For our purposes, this is the best information we have and all we need to know.
The chapter is a history of the evolution of geographic technologies and their contributions to military activities. The chapter also contends that geographic technologies fundamentally underpin the so-called "Revolution in Military Affairs" (RMA). This is a very debatable point, and we will have some fun doing just that. The RMA concept is somewhat out of favor in military academic circles, but a different major discussion addressed the related concept of "Network Centric Warfare (NCW)." I will ask you to consider whether the NCW is still worth discussing, and how it relates to geospatial intelligence. We will also look at an alternative view provided by P.W. Singer in Wired for War that posits the RMA is really all about robots. We will then look at the current discussion about the role of artificial intelligence coupled with ground, air, and sea "killer robots" and the role GEOINT might play.
Our final topic on future applications of GEOINT is actually up to the students. This topic will provide an opportunity for you to educate me and your classmates on future applications based on your research and experience. We are at a transitional point in history with the end of OIF and OEF, and apparently a return to competition and potential conflict with near-peer competitors such as Russia and China (or proxies such as Ukraine, Israel, and Taiwan). Consider how all of this will affect Geospatial Intelligence, and how this course should reflect those potential changes. We look forward to your feedback on this to help us with future revisions to keep this course current.
Lesson Objectives
At the end of this lesson, you will be able to:
- analyze the evolution of military applications of GIS&T from 19th Century to the present (including cartography, remote sensing, GIS, GPS, and simulations/modeling);
- critique the idea that GIS&T underpins the so-called "Revolution in Military Affairs" as articulated by Schneider;
- analyze network centric warfare, military robotics, and the application of military AI (to include the Replicator Initiative) and evaluate and explain the role of GEOINT in the future;
- speculate on future applications of geospatial intelligence for national security.
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
6.2 Checklist
Lesson 6 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 6:
- Work through Lesson 6 in this website.
- Read:
- "Geotechnology, the US Military, and War [95]" in Geography and Technology (Pages 401-427) (PSU Login required)*
- "The Big Cebrowski and the Real RMA: Thinking About Revolutionary Changes in Technologies" in Wired for War (Chapter 10, Pages 179-204) (located in Canvas)*
-
"The State of Artificial Intelligence and Machine Learning (AI/ML) in the GEOINT Community and Beyond" from the US Geospatial Intelligence Foundation (USGIF) (located in Canvas)*
-
"What is Network-Centric Warfare?" from Naval Post. (located in Canvas)*
-
"Human intel vs. technology." from The Washington Times. (located in Canvas)*
-
"Battle Networks and the Future Force, Part 2: Operational Challenges and Acquisition Opportunities." from CSIS Briefs. (located in Canvas)*
-
"Unpacking the Replicator Initiative at the Defense News Conference" from U.S. Department of Defense. (located in Canvas)*
- View all videos unless noted as optional
- Participate in Lesson 6 - GRADED Discussion Forum (#2).
* Students who register for this Penn State course gain access to assignments and instructor feedback, and earn academic credit. Information about Penn State's Online Geospatial Education programs is available at the Geospatial Education Program Office [3].
6.3 Evolution of Military GIS and T
Before we get too deeply into the topic at hand, consider viewing the following videos about the history of remote sensing. The videos were produced by the American Society for Photogrammetry and Remote Sensing (ASPRS) in celebration of their 75th anniversary and in preparation for a full length documentary on Remote Sensing. The videos are also available on YouTube at: The American Society for Photogrammetry and Remote Sensing [96].
Video: Evolution of Analog to Digital Mapping (3:41)
[MUSIC PLAYING]
ROY MULLEN: Early map preparation was all by foot.
WILLIAM A. RADLINSKI: You had to go and walk the land.
ALFRED O. QUINN: Well, I'd never heard of photogrammetry before.
MORRIS THOMPSON: What is a stereoplotting instrument?
ROY MULLEN: Oh, there were many things--
WILLIAM A. RADLINSKI: State-of-the-art cameras.
ROY MULLEN: Various multiplex systems.
ALFRED O. QUINN: The Fairchild system--
FREDERICK DOYLE: The Kelsh plotter projector photographed from a glass plate. We went from optical systems to mechanical systems.
MARILYN O'CUILINN: With every generation, the resolution got better and the geometric fidelity of the lenses got better.
WILLIAM A. RADLINSKI: We got into space imagery early on.
MARILYN O'CUILINN: There were the analytical stereoplotters.
ROY MULLEN: Computers came along as a tool for design.
MARILYN O'CUILINN: And then forward image motion compensation. We went to softcopy photogrammetry.
ROY MULLEN: And digital orthophotography.
MARILYN O'CUILINN: And then, of course, the digital cameras.
JACK DANGERMOND: This database wasn't about money or about people. It was about geographic information systems.
ROY MULLEN: Because of the ability to digitize directly, photogrammetry, as we knew it, reached its apex of evolution.
MARILYN O'CUILINN: 20 years ago, you would've seen monster pieces of metal.
WILLIAM A. RADLINSKI: In the world today, it's almost obsolete. Anybody can get a map just by turning on his computer and googling it.
ROY MULLEN: You put it into your GPS systems that use a base map. It's universally used throughout the world now.
MARILYN O'CUILINN: And the appetite for that sort of digital data is almost insatiable.
[MUSIC PLAYING]
Knowledge Check
Prepare for the quiz by answering the following questions.
Video: Aerial Survey Pioneers (2:56)
[TYPEWRITER KEYS CLACKING]
JIM LIVING: Back in 1923, Talbert Abrams bought an airplane, and he was barnstorming. And he found out that people would pay him more to take pictures of their farms and buildings than they would to go for a ride in the airplane. It was people like him that started this whole industry.
MO WEINBERG: Map makers, topographers from the four different sections of the country would bring about a revolution in mapping
MORRIS THOMPSON: They were in an airplane, open cockpit, no shelter. After you get the aerial photos, what do you do with them?
MARILYN O'CUILINN: They saw the possibilities of mapping from the air.
WILLIAM A. RADLINSKI: Most of the farmers didn't know how many acres they had, so we would determine which acreage was tillable, and that was called "mapping."
ALFRED O. QUINN: I tried to get mathematics with Professor Earl Church, but the only course that I could get with him was one known as photogrammetry.
DON LAUER: I had a plan to play for the army all-star basketball team, but Bob had a vision. He convinced me to go to graduate school. Profound experience.
MORRIS THOMPSON: I only know of one person around here who would still remember so much detail. And he wasn't there when it began, and I was.
[AIRPLANE ENGINES]
[MUSIC PLAYING]
Knowledge Check
Prepare for the quiz by answering the following questions.
Video: Geospatial Intelligence in WWII (1:58)
MARILYN O'CUILINN: Photogrammetry started with the military.
MORRIS THOMPSON: We had a combined TVA-USGS force. When the war started in Europe, we got to wondering about who is next.
MO WEINBERG: Map making was turned over to the Army map service, so that we would map for them.
MORRIS THOMPSON: And where do you suppose we started? China, Japan. Where? Upstate New York.
VIRGINIA LONG: They thought the Germans would invade the United States by way of the Saint Lawrence Waterway.
MORRIS THOMPSON: But that's just the beginning.
WILLIAM A. RADLINSKI: We landed in Normandy and went all the way across Europe, going with the front line. We provided topographic maps for the infantry and to the artillery.
ALFRED O. QUINN: After Pearl Harbor, we computed targets for the Naval bombardment prior to an invasion, so that ships could fire at coordinates.
FREDERICK DOYLE: We made target charts and bomb damage assessment charts for the B29 raids on Japan.
MORRIS THOMPSON: I remember there was one place we were mapping, and then came the news that there's nothing left of it. We were mapping Hiroshima.
ALFRED O. QUINN: Without maps, we'd have been lost in WW II.
Knowledge Check
Prepare for the quiz by answering the following questions.
Video: The Role of Women in the History of Photogrammetry (1:38)
FRANKLIN D. ROOSEVELT: I ask that the Congress declare a state of war.
ALFRED O. QUINN: A lot of our men, of course, were drafted. And so, we went recruiting young ladies.
GWENDOLYN GILL: Mr. Quinn asked if I was interested in the job. I accepted it immediately. I was real glad to get a job with TVA.
VIRGINIA LONG: I was fresh out of college when I was assigned to maps and surveys.
MARGARET DELAYNEY: We did parcels of property land somewhere. It was hush-hush, because we weren't supposed to know what this was.
LOUISE EDWARDS: But when you saw a map that you were compiling in the newspapers, you had a pretty good idea.
MORRIS THOMPSON: They took to it. They learned quickly. Their drafting was nicer than ours.
ALFRED O. QUINN: They had greater patience than most men. They were well-adapted to the photogrammetric equipment.
SID IZLAR: And I said, I'd love to get in the multiplex, because all these girls they were hiring were making more money than I was.
MARILYN O'CUILINN: In ASPRS, being a woman was not much of a barrier.
If you look around now at the USGS, and the civilian side, it's truly becoming one world and this is part of it.
Knowledge Check
Prepare for the quiz by answering the following questions.
Video: Photogrammetry in Space Exploration (2:00)
[MUSIC PLAYING]
FREDRICK DOYLE: Nowadays, sophisticated programs are used to make the maps. It's not the challenge it was when I was working on it. We were making the maps of the moon. I was in charge of the cameras on the Apollo spacecraft. We established 14,000 points. We had used photographs from four different missions. It was an enormous job.
We made a whole series of maps for the ground crews-- what they would see at each station, digital maps and perspective views. A very fancy package.
JACK SCHMITT: Oh, shoot.
EUGENE CERNAN: Oh, you won't believe it.
FREDRICK DOYLE: But when they unloaded the roving vehicle, they broke one of the fenders.
EUGENE CERNAN: Oh, there goes a fender.
FREDRICK DOYLE: They decided to patch the fender.
HOUSTON: OK, we'll need to tape it.
FREDRICK DOYLE: They took our set of maps and duct tape.
EUGENE CERNAN: How do you want those things taped together?
HOUSTON: Allow about an inch of overlap, and tape both sides of them.
FREDRICK DOYLE: So they didn't use them at all on the terrain. When we got back, they said, well, those were the most valuable maps we had ever made.
[LAUGHTER]
ROY MULLEN: There may be one map the saves an untold number of lives. It's intangible what value that is. But think about what was avoided by having had that map to begin with.
ALFRED O. QUINN: The use of digital map data in all kinds of investigations, plans, developments-- I think the whole thing is going to continue.
MARILYN O'CUILINN: It's very exciting to watch the progression, because it does touch so many aspects of our lives.
[MUSIC PLAYING]
Knowledge Check
Prepare for the quiz by answering the following questions.
Lowenthal's text he taught us about the evolution of the US intelligence community and made mention of the role of IMINT. Military applications of geographic techniques can be traced much farther back into history.
Required Reading
Read pages 401-419 of "Geotechnology, the US Military and War" in Geography and Technology - edited by Stanley D. Brunn, Susan L. Cutter, and JW Harrington Jr. Dordrect: Kluwer Academic Publishers. Registered students can access this reading in Lesson 6 in Canvas.
As you read, do some critical thinking and ask yourself the following questions.
- Corson and Palka are not geographic techniques specialist or geospatial intelligence professionals. Why would they be asked to write such a chapter for an American Association of Geographers centennial celebration book entitled Geography and Technology?
- The authors focus on the US military. What additions would there have been had they included the contributions and experiences of other countries? Why did they limit themselves to the US experience?
- The authors are both military academics. What might this chapter have looked like had someone with a different background and cultural filter written it (e.g., a civilian academic remote sensing specialist, a human geographer, an NGA analyst)?
- This chapter was written in 2002 and revised in 2003 for a 2004 publication. What should be added to bring the chapter up to date?
6.4 GIS and T and the "RMA"
Required Reading
Read pages 419-427 of "Geotechnology, the US Military and War" in Geography and Technology.
Read pages 179-204 "The Big Cebrowski and the Real RMA: Thinking About Revolutionary Changes in Technologies" in P.W. Singer's Wired for War.
Registered students can access these readings in Lesson 6 in Canvas.
As you read the chapter by Corson and Palka, do some critical thinking and ask yourself:
- Corson and Palka use limited definitions of the RMA based on Schneider’s approach. Given Singer's approach and other definitions of the RMA, do Corson and Palka's contentions still stand up?
- Corson and Palka are both geographers, writing in a geography book. Singer is a journalist. How might different authors from different communities have envisioned the underpinnings of the RMA? In terms of power relationships, how does the contention that the RMA is underpinned by geographic techniques bolster the discipline of geography and GIS&T, while potentially disadvantaging other disciplines?
- Do you agree with the author’s contentions? Why or why not?
The literature suggests that so-called Revolutions in Military Affairs (RMA) have occurred in the past with the advent of technologies such as gunpowder, railroads, the aircraft carrier, and nuclear weapons. This literature goes on to suggest that a new RMA is emerging, predicated on the idea that a rapid pace of technological innovation is altering the nature of modern warfare and the basic foundations of security. Barry Schneider of the Air War College identifies four new warfare applications that represent this RMA: long range precision strike, information warfare, dominating maneuver, and space warfare. All of these warfare applications are enabled by or associated with "information dominance," also known as "dominant battlespace awareness." The authors of the reading contend that both of those concepts are fundamentally based on geography and geographic technologies.
P.W. Singer, in his New York Times bestselling book Wired for War, contends that the real RMA is the revolution in robotics and the potential implications not only for warfare, but for society and the human species itself. I highly recommend the whole book as it is brilliantly written and really funny (Jon Stewart of The Daily Show noted it "Blew my f***ing mind...This book is awesome"). As you cannot read the whole book here, you will read chapter 10 entitled "The Big Cebrowski and the Real RMA: Thinking About Revolutionary Changes in Technologies."
6.5 Network Centric Warfare
We may or may not be in the midst of a RMA, but Network Centric Warfare (NCW) is a key capability (and vulnerability) for modern armed forces. Below are a few short readings and videos. The first addresses the nature of Network Centric Warfare; the second is a promotional video for Rafael’s “Fire Weaver” battlefield networking system. As critical thinkers, we need to consider multiple sides of issues. The article by Major General (RET) Robert H. Scales from 2005 challenges all the claims about network centric warfare in an urban insurgent environment such as Iraq. The article from the Center for Strategic and International Studies focuses on vulnerabilities of network centric forces and how resilience strategies can mitigate such vulnerabilities. The optional video from the Disruption Network Lab looks at the ethical issues of NCW and poses ethical questions and if the whole concept is really benefitting humanity.
As you read the following articles and watch the videos, do some critical thinking and:
- evaluate the arguments for and against the importance of NCW;
- analyze how the arguments stack up against your experience with NCW;
- analyze how all this talk of NCW impacts the field of geospatial intelligence, and specifically the role, mission, political position, and funding of the NGA.

Right: Major Allan Foskett, Chief of Highway Traffic, and SGT Juan Franco of the 450th Movement Control Battalion are shown preparing to enter Iraq
Blue Force Tracker allows Soldiers to maintain situational awareness on the battlefield by knowing their own location, the location of friendly forces (the blue forces), plotting enemy locations, and communicating this all over a network to maintain a common operating picture or COP. The system uses digital maps, remotely sensed imagery, and global positioning system data that are all geospatial intelligence products or techniques.
In the image on the right, MAJ Foskett has his Movement Tracking System (MTS) up. MTS is a satellite based system with a digital map that can be zoomed in and out. A global positioning system transmits the unit location to other users, and the system overlays all or selected users on the digital map. The system also allows for text messaging via satellite, thus overcoming the limitations of terrestrial radio systems. MTS allowed the 450th Movement Control Battalion to maintain in-transit visibility of critical logistics convoys, and to communicate over long distances. Highway Regulating Teams patrolling the main supply route often were able to call in medical evacuation helicopters for units out of radio contact, thus saving many lives. SGT Franco is a digital graphic designer. He took locational data obtained by GPS equipped Highway Regulation Teams and produced a simplified strip map of all the theater logistics nodes in Kuwait and Iraq. His map was widely reproduced and distributed. The map enabled both military and contracted logisticians to support the force.

Read
What is Network-Centric Warfare? [103]
McConoly, R. (2021, June 21). What is Network-Centric Warfare?. Naval Post. https://navalpost.com/what-is-network-centric-warfare/ [103]
Now watch with a critical eye this advertisement from defense contractor Rafael for their Fire Weaver system.
Video: FIRE WEAVER™ - A networked combat system (urban scenario) (4:33)
[Music]
As we all know, today's battlefields are more challenging than ever. We are required to fight in complex urban areas amongst civilian populations and to handle time-critical targets.
The biggest challenge is to close the sensor shooter loops in a very short time, accurately, effectively and efficiently. Today, we at Rafael are proud to present the revolutionary solution to these challenges. Fire Weaver, the world's most mature network detect system. See how in real-time action, the sensors detect and identify the targets.
Fire Weaver selects the optimal shooters and marks the targets to the shooter's site. As a result, all the attack processes are completed simultaneously in an unprecedentedly short time, as we are seeing different shooters from different locations simultaneously neutralizing different targets within a few seconds. This can only be achieved today with Fire Weaver.
Now, let's understand step by step how Fire Weaver actually works. As we see, all the forces are connected through a radio network.
[Music]
The attack process begins with a variety of sensors gathering information in the battlefield. The sensor identifies the target, classifies it and disseminates it through the system.
In the same way, all the other sensors detect and classify the information and disseminate it through the net to all the connected participants.
[Music]
Thanks to Rafael's advanced Computer Vision Technologies, each participant receives very accurate augmentation symbols, so they all see the same targets regardless of their position.
Once the sensors detect and classify the targets, the Fire Weaver core, the brain of the system, goes immediately into action. It calculates all the data and within seconds it chooses the optimal shooter for each target based on such parameters as location, line of sight effectiveness and current ammo status. All that in accordance to the Fire policy. The process can be performed automatically or controlled according to the commander's decision.
As you see, the target is sent from the sensor to the shooter, who sees the target from his point of view on his sight.
The targets are neutralized simultaneously in a very short time with maximum precision, while minimizing damage and avoiding friendly.
Fire Weaver system enables other shooters to neutralize further targets. According to the same operational process, Fire Weaver uses three targeting languages, geocordinate Laser Designation, and Electro Optical Pixel. The system has already been tested in the field, including many to many and live fire scenarios. For the first time, With Fire Weaver, the sensor to shooter loop is closed in seconds instead of minutes.
[Music]
Now read this commentary by retired Major General Robert Scales. His perspective derives from operations in Iraq in 2003-2004. Are his observations in this 2005 article still applicable today?
Read
Human Intel vs. Technology [104]
Scales. R.H. (2005, February 2). Human intel vs. technology. The Washington Times. https://www.washingtontimes.com/news/2005/feb/2/20050202-102009-9150r/ [104]

Read
Battle Networks and the Future Force, Part 2: Operational Challenges and Acquisition Opportunities [105]
Harrison, T. ( 2021, November). Battle Networks and the Future Force, Part 2: Operational Challenges and Acquisition Opportunities. CSIS Briefs. https://www.csis.org/analysis/battle-networks-and-future-force-0 [105]
Government and military practitioners tend to take a very technical/operational approach to NCW. Seldom do they ask “just because we can do it, should we do it?” This optional video takes a critical look at NCW and includes presentations by expert whistleblowers.
The Keynote address in the following optional video was given by Lisa Ling (Whistleblower, Former Technical Sergeant, US Air Force Drone Surveillance Programme, US) and Cian Westmoreland (Whistleblower, Former US Air Force Drone Technician, US). It was moderated by Daniel Eriksson (CEO of Transparency International, SE/DE). Distribution Network Lab describes the video like this in the video description.
"This keynote presentation introduces what Lisa Ling and Cian Westmoreland have come to call the “Kill Cloud,” a rapidly growing networked infrastructure of global reach with the primary intent of dominating every spectrum of warfare. There is a need for a critical analysis of how the “Kill Cloud” operates, from its ideological underpinnings, its ambitions, to the technological approach being pursued to achieve global military dominance over all battlespace dimensions including, space, cyberspace, and the electromagnetic spectrum itself. Modern network centric warfare has been hidden behind the captivating image of the drone, yet these systems are vastly more complex, insidious, ubiquitous, and inaccurate than the public is aware, and its colonial underpinnings continue to bring endless war to societies across the globe. The Kill Cloud has emerged as an immense and evolving system of systems hastening the expansion of the Global War on Terror. This talk pays close attention to the US military drone programme’s contribution to the framing and evolution of modern network centric war. This Kill Cloud has far-reaching consequences beyond those of what have been traditionally considered in warfare. Read the full chapter in the book Whistleblowing for Change."
Optional Video
KEYNOTE: The Kill Cloud: Real World Implications of Network Centric Warfare (1 hour, 39 minutes)
Go to Keynote Transcript [106]
6.6 Warfare, GEOINT, and AI
So far in this lesson we have examined the relationship between geography and military technology from the 19th Century, and the idea of revolutions in military affairs or RMA’s from the ideas of Schnieder through Cerbowski to Singer. Whether or not it is a RMA, the application of artificial intelligence is the current focus (as of late 2023) of military thinkers.
The PBS News Hour video explores how AI is changing the battlefield in Ukraine (as of 2023) while also addressing ethical and legal issues associated with autonomous lethal AI weapons. The second video addresses (as of 2023) the Pentagon’s “Replicator” plan to field thousands of networked, AI enabled systems to deter the People’s Republic of China from aggression in the South China Sea and against Tawain. The associated transcript Is Deputy Secretary of Defense Kathleen Hicks announcing the Replicator initiative. The last reading from the US Geospatial Intelligence Foundation ties all of this talk about AI to how the geospatial community can contribute to Replicator, NCW, and the future of America’s military capability.
Video: How militaries are using artificial intelligence on and off the battlefield (6:14)
Search in video JOHN YANG: Artificial intelligence has been a crucial tool for many nation's militaries for years. Now the war in Ukraine is driving innovation. And as that conflict drags on, AI is rolling it is likely to grow. Ali Rogin looks at how militaries are using AI today, and ahead to how it might be used in the future.
ALI ROGIN: More artificial intelligence on the battlefield carries great potential, but also higher risk. Right now, Congress is pressing the Pentagon through legislation to invest further and move faster on AI to avoid falling behind on this nimble but critical technology. Paul Scharre is the Vice President and Director of Studies at the Center for a New American Security. He's also a former Army Ranger, Pentagon official and the author of "Four Battlegrounds: Power in the Age of Artificial Intelligence." Paul, thank you so much for joining us. Artificial Intelligence is already used to some extent on the battlefield, but we're not talking about completely autonomous technology, what is available currently, what are warfighters already using? And then where do you see the technology going in the near future?
PAUL SCHARRE, Vice President, Center For A New American Security: That's right, we're already seeing AI being used on the battlefield in Ukraine. Now, humans are still in control of the fighting. But one of the things that AI is doing is helping to process information faster. AI is being used to sift through satellite images and drone video feeds, and that helps militaries then better understand what's happening on the battlefield, make decisions faster, and then target the enemy faster and more accurately.
ALI ROGIN: So what happens when we do consider having humans not be at all in control when these systems are fully automated? What are the pros and cons of that?
PAUL SCHARRE: Well, we're already seeing drones being used in Ukraine that have all of the components needed to build fully autonomous weapons that can go out over the battlefield, find their own targets, and then all on their own attack those targets without any further human intervention. And that raises very challenging legal, and moral and ethical questions about human control over the use of force of war.
ALI ROGIN: Now we're seeing Ukraine sort of lead the conversation in the application of using these fully autonomous devices. Do you think we're going to see more of that? And is there concern about how they might be used by differently by state actors and non-state actors like terrorist organizations?
PAUL SCHARRE: Well, war is an accelerant of innovation. So the longer that this war goes on, the more that we're going to see more innovation on the battlefield. We're already seeing innovative uses of drones and counter drone technologies, things like electronic warfare systems that can target drone operators, and then call it artillery strikes on the drone operator. And that kind of technology pushes militaries towards more autonomy, but it's not just confined to nation states. ISIS actually had a pretty sophisticated drone army a few years ago, and they were carrying out drone attacks against Iraqi troops are pretty effective.
ALI ROGIN: And now we've talked about how AI is used in weapons, but how about systems off the battlefield?
PAUL SCHARRE: Well, most of what militaries do is not actually right at the tip of the spear fighting. It's logistics, personnel, maintenance, it's moving people pulling things from one place to another, on a day to day basis, it looks a lot like what Walmart or Amazon do. It's what happens at the end, it's different. And so AI has advantages and all of those other non-combat functions that are critical how to how militaries operate. And if militaries can make their maintenance and logistics, and personnel and finance functions, just 10 percent better, that's going to have huge impacts for militaries on ultimately, their capability at the military's edge on the battlefield.
ALI ROGIN: Now, some of what we're seeing in Ukraine is employing commercially available technology that can simply be purchased for a couple $1,000. How is the U.S. Department of Defense, dealing with keeping up with that sort of competition that exists? How is that playing out?
PAUL SCHARRE: Well, they're not keeping up. That's the short version, they're woefully behind because the culture is so radically different. And the bottom line is, you can't buy AI the same way that you might buy an aircraft carrier. The military is moving too slow. It's mired in cumbersome bureaucracy. And the leadership of the Pentagon has tried to shake things up. They had a major reorganization last year of the people working AI and data and software inside the Defense Department. But we haven't seen a lot of changes since then. And so the Pentagon is going to have to find ways to cut through the red tape and move faster if they're going to stay on top of this very important technology.
ALI ROGIN: And Paul, lastly, on the global level, as this technology continues to proliferate, some countries are calling for the establishment of some general rules of the road. What does that conversation look like? What are some of the contours of that debate?
PAUL SCHARRE: Well, we've certainly seen debates over the last several years, all the way back to 2014. About lethal autonomous weapons, there's a pretty wide range of views on this. And the United States, as well as other countries like Russia, have said that we have existing rules, we have the laws of war. The laws of war apply to autonomous weapons, just like any other weapon, and we need to focus on adhering to those and making sure that any use of these weapons is consistent with the law of war.
ALI ROGIN: And what about the other side of that, those who say we need additional rules and that the existing rules don't fully apply here?
PAUL SCHARRE: That's right. So there's about 30 countries that have said that they'd like to see a preemptive, legally binding treaty that would ban autonomous weapons before they can be built. But right now, none of the leading military powers of robotics developers are part of that group. And so it hasn't yet had the political heft to get to a treaty. That could change as we see the technology advance. And as we see, of course, more broadly, concerns about AI growth (ph), as we're seeing AI technology advanced and there's more calls for global regulation of AI.
ALI ROGIN: Paul Scharre with the Center for a New American Security. Thank you so much for joining us.
PAUL SCHARRE: Thank you. Thanks for having me. 16:39 NOW PLAYING The future of war
Optional Additional Resources
- DOD Artificial Intelligence Strategy Review presentation by the DOD (2019). (located in Canvas)*
- Military Applications of Artificial Intelligence: Ethical Considerations in an Uncertain World 2020 report published by the Rand Corporation. (located in Canvas)*
Both of these optional resources are available to registered students in the Lesson 6 Canvas module.
In August 2023 Deputy Secretary of Defense Kathleen Hicks announced the Replicator Initiative to create thousands of low cost land, sea, and air drones to counter China’s advantage in mass in the South China Sea and Taiwan Straits.
Video: Pentagon 'replicator' initiative: US military plans to thwart China with 1,000 war drones (01:47)
Susan Tehrani: Well, it seems like the future of battlefield is here. We're talking about drones. These are being effectively used in the war in Ukraine. And now the Pentagon has announced a new initiative to use this technology. According to a Wall Street Journal report, the US Department of Defense is considering the development of a vast network of artificial intelligence powered technology, drones, and autonomous systems.
These will be developed within the next two years to counter threats from China. The report added that the Deputy Secretary of Defense, Kathleen Hicks, will sketch out some of the air, land, and sea capabilities that the Pentagon is looking to develop. Last week as well, reports came about Pentagon's new initiative, which they dubbed as Replicators. Pentagon intends to field thousands of drones within the next two years for possible conflicts in the Taiwan Strait.
These low cost and mass deployed unmanned systems could put pressure on Beijing. And according to Hicks, replicator is meant to help us overcome Beijing's biggest advantage mass, which basically means more ships, more missiles, and more people. The Deputy Secretary of Defense further added that with deployment of these drones, it will become difficult for Beijing to attack them. It will be harder to hit and harder to beat. Funding for Replicator would come from existing funds and costs hundreds of millions. The latest Pentagon budget request includes $1.8 billion for artificial intelligence for fiscal year 2024.

Read
Here is Deputy Secretary of Defense Hick’s speech about the Replicator iniative. [113]
Hicks' Remarks: Unpacking the Replicator Initiative at the Defense News Conference (As Delivered). (2023, Sept. 6) U.S. Department of Defense. https://www.defense.gov/News/Speeches/Speech/Article/3517213/deputy-secr... [113]
Required Reading
The State of Artificial Intelligence and Machine Learning (AI/ML) in the GEOINT Community and Beyond [114] published in September 2021.
Now you get to geek out a little bit while reading the white paper, consider joining or following USGIF. They host excellent professional conferences with great presentations by leaders from DOD, NGA, industry, academia, and other agencies. They also have a scholarship program that has benefitted many Penn State students.
According to their website About - USGIF [115] :
The United States Geospatial Intelligence Foundation (USGIF) is a 501(c)(3) nonprofit educational foundation dedicated to promoting the geospatial intelligence tradecraft and developing a stronger GEOINT Community with government, industry, academia, professional organizations, and individuals who develop and apply geospatial intelligence to address national security challenges. USGIF achieves its mission through various programs and events and by building the community, advancing the tradecraft, and accelerating innovation.
6.7 Future GEOINT Applications
This topic is up to you, the students. Please do some thinking and a little research to identify and consider future applications of geospatial intelligence in the national security arena. Future applications of geospatial intelligence will be one of our major discussion questions in this week's Graded Discussion Forum (#2). You might also give some thought to the current issues in the news surrounding cybersecurity and the leaking of government sensitive and public sensitive data from organizations such as the National Security Agency (NSA). As this debate continues, what are some of the legal and societal ramifications of needing to collect geospatial intelligence data while protecting citizens' basic freedoms in a democracy?
6.8 Summary and Final Tasks
Summary
This lesson ends our study of national security applications of GEOINT. The lesson and our reading assignments covered:
- Evolution of Military GIS&T
- GIS&T and the "RMA"
- Network Centric Warfare
- Artificial Intelligence and future GEOINT Applications
Geographic techniques have played an important role in military history, and military requirements have spurred rapid advances in geographic techniques. Geospatial intelligence is an evolving INT that leverages these techniques in support of policy makers and Warfighters. It will be interesting to see how the evolving concepts of the RMA and NCW, as well as new technologies and applications such as unmanned vehicles integrated with artificial intelligence, will interact with geospatial intelligence. Some of you in this class will be future leaders and decision-makers involved in this process.
Deliverable: Lesson 6 - GRADED Discussion Forum (#2)
Return to Lesson 6 in Canvas. Look for the Lesson 6 - GRADED Discussion Forum (#2), where you will find the four topics for this assignment separated out in their own discussion forums. The minimum requirement is that each of you post one primary response to TOPIC 1, one primary response to TOPIC 2a or TOPIC 2b, one primary response to TOPIC 3. Your thoughts about TOPIC 4 are welcome yet optional. You must then comment on at least THREE of your classmates' posts. (Six total posts - three primary posts and three comments.)
Remember to analyze the questions to determine specified and implied requirements, explicitly demonstrate your higher order and critical thinking skills, show me you read the required readings, and that you did some research if required. I challenge you to try and see beyond your cultural filters (which are sometimes blinders) and view these issues from a higher level or different perspective.
Note: Please post your primary response to the questions by Sunday evening to allow time for everyone to post comments by Tuesday night.
Before you move on to Lesson 7, double-check the Lesson 6 Checklist [116] to make sure you have completed all of the required activities for this lesson.
Looking Ahead
Next week, we start Part Three of the course on Disaster Management. This might be a new subject for many of you, and it is an important topic for all citizens. You also get a change of pace on your deliverable. After you have completed the brief lesson introduction in Canvas, you will leverage the resources of the Federal Emergency Management Agency (FEMA) to become National Incident Management System (NIMS) certified. The FEMA website provides free training and certification to government officials, first responders, and concerned citizens. Knowledge of NIMS will help you speak the same language of disaster and facilitate interagency cooperation for those of you in the field. The next lesson will address:
- the basic concepts of disaster management;
- the hierarchy of disaster responders, roles of the major agencies/organizations, and the capabilities and limitations of different types of organizations;
- the fundamentals of emergency management;
- the National Incident Management System (NIMS);
- the Geospatial Concept of Operations (GeoCONOPS).
Before moving on, you have to complete Lesson 6 - GRADED Discussion Forum (#2).
Good Luck!
Lesson 7: Disaster Management Part 1
7.1 Overview
This lesson begins our three-week examination of homeland security, emergency preparedness, and disaster management. This first lesson covers basic concepts of disaster management, as well as the National Incident Management System (NIMS) and the Geospatial Concept of Operations (GeoCONOPS). The assignments for this lesson are different from other lessons in that you will do most of your work on the Federal Emergency Management Agency's Emergency Management Institute website. You will complete the online training courses for the NIMS and GeoCONOPS, resulting in your basic certification in these areas. This basic knowledge will improve your ability to understand how geospatial intelligence can support interagency disaster preparedness and response activities.
Lesson Objectives
At the end of this lesson, you will be able to:
- explain the basic concepts of emergency management;
- explain the role of the major agencies/organizations;
- discuss the capabilities and limitations of different types of organizations;
- describe the key concepts, principles, scope, and applicability underlying the National Incident Management System (NIMS);
- describe how GIS technology can support the emergency management community to include: GIS fundamentals and history; how GIS is used in emergency management and tools available to enhance GIS usefulness.
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
7.2 Checklist
Lesson 7 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 7:
- Work through Lesson 7 on this website.
- Complete the following three required online certification courses
- IS-230: Fundamentals of Emergency Management. (Note: A link to the online certification course is provided on page 7.3 of the lesson.)
- IS-700: An Introduction to the National Incident Management System (NIMS). (Note: A link to the online certification course is provided on page 7.4 of the lesson.)
- IS-922: Applications of GIS for Emergency Management (Note: A link to the online certification course is provided on page 7.5 of the lesson.)
- Complete the following optional (extra credit) online certification course
- IS-103: Geospatial Information Systems Specialist (GISS). (Note: A link to the online certification course is provided on page 7.6 of the lesson.)
- Submit your Certificates of Completion in .pdf format to the Lesson 7 - GRADED Assignments in Canvas.
7.3 Emergency Management
Integrated Emergency Management System
When an emergency or disaster occurs:
- agencies from different jurisdictions and government levels need to work together. Major emergencies and disasters ignore city, county, and state boundaries.
- rapid decision making is required.
Without planning and coordination, emergency operations can suffer from serious misdirection and mistakes.
An integrated emergency management system provides a conceptual framework for organizing and managing emergency protection efforts. This framework prescribes when and how local officials and agencies will work together to deal with a full range of emergencies, from natural disasters to terrorism.
Each level of government participates in and contributes to emergency management.
- Local government has direct responsibility for the safety of its citizens, knowledge of the situation and personnel, and proximity to both the event and resources. Emergency Support Services are the departments of local government that are capable of responding to emergencies 24 hours a day. They include law enforcement, fire/rescue, and public works. They may also be referred to as emergency response personnel or first responders.
- State government has legal authorities for emergency response and recovery and serves as the point of contact between local and Federal governments.
- Federal government has legal authorities, fiscal resources, research capabilities, technical information and services, and specialized personnel to assist local and State agencies in responding to and recovering from emergencies or disasters.
The Spectrum of Incident Management Actions
Incident management covers a spectrum of activities ranging from:
- Pre-incident activities, such as information sharing, threat identification, planning, and readiness exercises.
- Incident activities that include lifesaving missions and critical infrastructure support protections.
- Post-incident activities that help people and communities recover and rebuild for a safer future.
The National Planning Frameworks [117] describe how the community works together to achieve the National Preparedness Goal [118], which is: "A secure and resilient nation with the capabilities required across the whole community to prevent, protect against, mitigate, respond to, and recover from the threats and hazards that pose the greatest risk." These address the full spectrum of emergency management activities, including these five mission areas:
- Prevention: Prevent, avoid or stop an imminent, threatened or actual act of terrorism.
- Protection: Protect our citizens, residents, visitors, and assets against the greatest threats and hazards in a manner that allows our interests, aspirations, and way of life to thrive.
- Mitigation: Reduce the loss of life and property by lessening the impact of future disasters.
- Response: Respond quickly to save lives, protect property and the environment, and meet basic human needs in the aftermath of a catastrophic incident.
- Recovery: Recover through a focus on the timely restoration, strengthening and revitalization of infrastructure, housing and a sustainable economy, as well as the health, social, cultural, historic and environmental fabric of communities affected by a catastrophic incident.
Preparedness as Program Centerpiece
Between emergencies and disasters, emergency managers can focus on preparedness measures. The National Preparedness Cycle is a continuous "cycle of planning, organizing, training, equipping, exercising, evaluating, and taking corrective action" in an effort to ensure effective coordination during incident response (FEMA, "Developing and Maintaining Emergency Operations Plans," 2010).
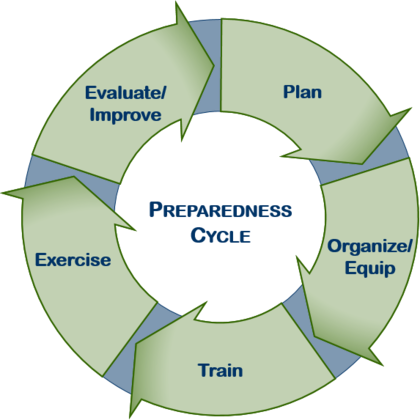
Threat and hazard identification is a crucial first step in the planning process. This analysis determines:
- what can occur;
- how likely it is to occur;
- what devastation it is likely to cause;
- how likely it is to affect the community;
- how vulnerable the community is to a hazard.
The first step is to develop a list of threats and hazards that may occur in the community. Next, profiles should address each hazard's:
- duration
- seasonal pattern
- speed of onset
The availability of warnings also will play a crucial role in a hazard profile.
Hazard-specific information is combined with a profile of your community to determine the community's vulnerability—or risk of damage—from the hazard.
After information about the community is gathered, emergency managers use it to develop the community's hazard analysis. After a hazard and community profile has been compiled, it is helpful to quantify the community's risk by merging the information so that the community can focus on the hazards that present the highest risk.
Risk is the predicted impact that a threat or hazard would have on people, services, and specific facilities and structures in the community. A severity rating quantifies the expected impact of a specific event.
A guide for conducting threat and hazard identification and risk assessments (THIRA) can be found at: Comprehensive Preparedness Guide 201 [121].
Planning and Coordination

The appearance of U.S. Department of Defense (DoD) visual information does not imply or constitute DoD endorsement.
An Emergency Operations Plan (EOP) is a key component of an emergency program.
When an emergency threatens or strikes, the community must be prepared to take immediate action. An EOP describes:
- what emergency response actions will occur….
- under what circumstances….
- using what resources….
- who will be involved and by what authority.
An EOP consists of the following basic components:
- The Basic Plan
- Annexes
- Appendices
- Standard Operating Procedures
The EOP provides overall authority, roles, and functions during emergencies.
An Emergency Operation Center (EOC) is a central location where agency representatives can coordinate and make decisions when managing an emergency response. EOC personnel do not control the on-scene response but help on-scene personnel by establishing priorities, coordinating the acquisition and assignment of resources, and acting as a liaison with other communities and the State. The EOC is a place for working together.
The Multi-Agency Coordination System (MACS) integrates facilities, equipment, personnel, procedures and communications into a common system with responsibility for coordinating and supporting domestic incident management activities. The functions of the system are to support incident management policies and procedures, facilitate logistical support and resource tracking, inform resource allocation decisions, coordinate incident-related information, and coordinate interagency and intergovernmental issues regarding policies, priorities, and strategies.
The Incident Command System (ICS) defines the operating characteristics, interactive management components, and structure of incident management and emergency response organizations engaged throughout the life cycle of an incident. NIMS requires the use of ICS.
The conclusion of mutual aid agreements to augment local resources is an important part of developing and maintaining an emergency management program.
In any emergency or disaster, mutual aid partners may be able to provide:
- communications capability
- emergency personnel
- overall management strategy and program management
- equipment such as bulldozers or dump trucks
- sandbags
- facilities such as warehouses or temporary shelters
The best way to communicate the plan to response agencies that are responsible for implementing the plan is through training and exercising.
Training is critical to response personnel so that they know:
- what they are to do,
- when they are to do it,
- how they are to do it.

The appearance of U.S. Department of Defense (DoD) visual information does not imply or constitute DoD endorsement.
Functions of an Emergency Management Program
There are two ways to categorize emergency management activities:
- emergency management core functions that are performed during an emergency;
- emergency management program functions that continue on a day-to-day basis.
The eight emergency management core functions performed during emergencies are:
- Direction and Control
- Communications
- Warning
- Emergency Public Information
- Evacuation (or in-place sheltering)
- Mass Care
- Health and Medical Services
- Resource Management
Day-to-day emergency management program functions include:
- Hazard Identification and Risk Assessment
- Hazard Mitigation
- Resource Management
- Planning
- Direction and Control
- Communication and Warning
- Operations and Procedures
- Logistics and Facilities
- Training
- Exercises, Evaluations, and Corrective Actions
- Public Education and Information
- Finance and Administration
Emergency Management Program Partners
Emergency management partners include local, State, and Federal emergency managers.
The State's role is to supplement and facilitate local efforts before, during, and after emergencies. The State must be prepared to maintain or accelerate services and to provide new services to local governments when local capabilities fall short of disaster demands.
The local Emergency Program Manager has the day-to-day responsibility of managing emergency programs and activities. The role entails coordinating all aspects of a jurisdiction's mitigation, preparedness, response, and recovery capabilities.
The State provides direct guidance and assistance to local jurisdictions through program development, and it channels Federal guidance and assistance down to the local level. In a disaster, the State office helps coordinate and integrate resources and apply them to local needs. The State's role might be best described as "pivotal."
The Federal government provides legislation, Executive Orders, and regulations that influence all disaster activities. It also maintains the largest pool of fiscal resources that can be applied to emergency management. Assistance may take the form of fiscal support, technical assistance, and information about materials, personnel resources, and research. FEMA takes a lead role in national preparedness for major crises. It also plays coordinating and supportive/assistance roles for integrated emergency management in partnership with State and local emergency management entities.
Emergency Management Online Training
Click on the following link to access the FEMA's IS-230: Fundamentals of Emergency Management [124] online training. Complete the training and take the online examination. FEMA will provide a certificate, which you are to provide to the instructor as an Adobe Acrobat (.pdf) file.
Deliverable #1 (required - 70 points)
Make sure you save the IS-230 Fundamentals of Emergency Management certificate .pdf file after completing the online certification. To submit your certificate for your grade, return to Canvas and click on the Lesson 7: IS-230 Certificate (GRADED) link. The Assignment will have directions for submitting your certificate.
Please note: Depending on the amount of web traffic, there can be a one to two day delay between the time you complete your IS-230 Certificate and when FEMA emails you the PDF of your certificate. You should consider completing the online training well before the deliverable date.
7.4 National Incident Management System
Click on the following link to access the FEMA's IS-700: An Introduction to the National Incident Management System (NIMS) [125] online training. Complete the training and take the online examination. FEMA will provide a certificate that you are to provide to the instructor as an Adobe Acrobat (.pdf) file.
Deliverable #2 (required - 35 points)
Make sure you save the IS-700: An Introduction to the National Incident Management System (NIMS) certificate as a .pdf file after completing the online certification. To submit your certificate for your grade, return to Canvas and click on the Lesson 7 - GRADED (IS-700 NIMS Certificate) link. The Assignment will have directions for submitting your certificate.
Please note: Depending on the amount of web traffic, there can be a one to two day delay between the time you complete your NIMS Certificate and when FEMA emails you the PDF of your certificate. You should consider completing the online training well before the deliverable date.
7.5 Applications of GIS for Emergency Management
Click on the following link to access FEMA’s IS-922: Applications of GIS for Emergency Management [126] online training. Complete the training and take the online examination. FEMA will provide a certificate that you are to provide to the instructor as an Adobe Acrobat (.pdf) file.
Deliverable #3 (required - 35 points)
Make sure you save the IS-922: Applications of GIS for Emergency Management certificate as a .pdf file after completing the online certification. To submit your certificate for your grade, return to Canvas and click on the Lesson 7 - GRADED (IS-922 Certificate) link. The Assignment will have directions for submitting your certificate.
Please note: Depending on the amount of web traffic, there can be a one to two day delay between the time you complete your Certificate and when FEMA emails you the PDF of your certificate. You should consider completing the online training well before the deliverable date.
7.6 Geospatial Information Systems Specialist (GISS)
Click on the following link to access the IS-103: Geospatial Information Systems Specialist [127] (GISS). Complete the training and take the online examination. FEMA will provide a certificate that you are to provide to the instructor as an Adobe Acrobat (.pdf) file.
Deliverable #4 (Extra Credit - 20 points)
Make sure you save the IS-103: Geospatial Information Systems Specialist (GISS) certificate as a .pdf file after completing the online certification. To submit your certificate for your grade, return to Canvas and click on the Lesson 7: IS-103 Certificate (Extra Credit) link. The Assignment will have directions for submitting your certificate.
Please note: Depending on the amount of web traffic, there can be a one to two day delay between the time you complete your Certificate and when FEMA emails you the PDF of your certificate. You should consider completing the online training well before the deliverable date.
7.7 Geospatial Concept of Operations
Geospatial technology is used throughout the mission areas of prevention, protection, mitigation, response, and recovery. The Homeland Security Geospatial Concept of Operations (GeoCONOPS) is a strategic roadmap to understand and improve the coordination of geospatial activities across the entire spectrum of the nation—from federal, state, and local governments, to private sector and community organizations, academia, the research and development industry, and citizens - in support of homeland security and homeland defense. The GeoCONOPS includes:
Community Tools (Resources and Capabilities)
- current resources and capabilities such as personnel, assets and analytical models
Best Practices
- requirements and activities for disaster response mission areas
Federal Operation Centers
- a detailed scenario of response activities for a catastrophic natural event
Authoritative Data
- requirements and activities for mitigation and preparedness areas
Benefits of the GeoCONOPS include:
- defines the geospatial mission blueprint of the resources and capabilities available for support in the homeland security enterprise
- identifies points of coordination and collaboration
- documents authoritative geospatial data sources
- describes best practices
- identifies technical capabilities
Optional Reading
In the previous version of Geography 882 we assigned the three FEMA IS lessons addressing the HSE Geospatial Concept of Operations. FEMA discontinued these lessons without replacement and archived the content. The information is valuable and interesting so while you won't be assessed on the content, it would be worth your time to review the material in the link below.
Homeland Security Geospatial Concept of Operations (GeoCONOPS) [128]
7.8 Summary and Final Tasks
Summary
Completion of this lesson gives you a basic understanding of emergency preparedness and the emergency management systems in use in the US. The lesson and the online FEMA lessons covered:
- basic concepts of disaster management;
- the hierarchy of disaster responders, the role of the major agencies/organizations, and the capabilities and limitations of different types of organizations;
- the Emergency Management System;
- the National Incident Management System (NIMS);
- the Homeland Security Geospatial Concept of Operations (GeoCONOPS)
You are now officially certified to speak the language and understand the organization and operation of civilian agencies as they prepare for and respond to emergencies. For those of you in the military or the intelligence community, this knowledge facilitates your ability to work as part of the interagency process. For other students, this knowledge will improve your understanding of how your government deals with emergencies and disasters. Should you decide to get involved in emergency preparedness and response as a volunteer (e.g., in the American Red Cross, Community Emergency Response Team, or Medical Reserve Corps), this knowledge will improve your ability to work with civilian government agencies at all levels.
Final Tasks
Deliverables: Lesson 7
Required: IS-230, IS-700, IS-922 online certifications
Optional (for extra credit): IS-103 online certification
As previously mentioned, when you have completed your online certifications, return to Lesson 7 in Canvas. Look for the Lesson 7 Assignments where you will submit your PDF copies of the 3 required certifications and one optional certification. You will find directions for submitting your pdf files when you enter the Assignments.
Remember: There may be a delay between the time you complete the online certification and when FEMA emails your PDF certificate. Consider completing your online training well before the due date.
Before you move on to Lesson 8, double-check the Lesson 7 Checklist [129] to make sure you have completed all of the required activities for this lesson.
Looking Ahead
Next week is another heavy reading week, capped off by your second reflection paper. In our next lesson, we are going to consider:
- Cutter's concept of an "All Hazards" approach to disaster management;
- capabilities and limitations of geospatial intelligence in support of the disaster management process;
- how geospatial intelligence can be of value to the first responder and provide examples;
- social justice issues in the disaster management process;
- differences in the practice of geospatial intelligence for disaster management and other national security applications.
If you have not already taken the Midterm Course Assessment Survey, please consider completing the survey.
Lesson 8: Disaster Management Part 2
8.1 Overview
This lesson continues our three-week examination of homeland security, emergency preparedness, and disaster management. The last lesson introduced you to the basic concepts of emergency management and allowed you to become certified in the National Incident Management System and the Geospatial Concept of Operations. This lesson will introduce you to the background and importance of the "All Hazard" approach to the study of hazards, risk, and vulnerability. We will also look at federal disaster planning by examining the National Preparedness System, FEMA's geospatial support activities, and support provided by the Department of Defense in domestic emergency planning and response.
Lesson Objectives
At the end of this lesson, you will be able to:
- evaluate the pros and cons of a policy that would make Geographic Science and Technology the “linchpin” of the US Emergency Management System and conclude with a solid approve/disapprove recommendation that logically derives from your analysis;
- defend your own analysis using your higher order and critical thinking skills;
- write a graduate level political analysis paper.
Assignment Preview
A heads up- your deliverable this week is a policy analysis paper for the Secretary of Homeland Security. You must recommend whether the Secretary should approve/disapprove a policy to make GIScience the linchpin of the US Emergency Management System. The lesson and the readings provide information that will support your paper. A word to the wise: your ability to think critically and address the following topics will bolster your recommendation in your political analysis paper. Have a thorough understanding of:
- Cutter's concept of an "All Hazards" approach to disaster management;
- federal disaster preparedness and response efforts;
- the capabilities and limitations of geospatial intelligence in support of the disaster management process;
- how geospatial intelligence can be of value to the first responder and provide examples;
- the practice of geospatial intelligence for disaster management and other national security applications.
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
8.2 Checklist
Lesson 8 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 8:
- Work through Lesson 8 in this website.
- Read (the following are available in Canvas):
- "National Response Framework [130]" from FEMA (Scan)
- "The Role of Vulnerability Science in Disaster Preparedness and Response [131]" from Susan Cutter's testimony, beginning on page 13 of the report.
- "The Executive Summary" from the National Infrastructure Protection Plan 2013 [132].
- "GIS: a common operational picture for public safety and emergency management [133]" from J. Perdikaris's paper, WIT Press.
- Chapter 1 in Tomaszewski, Brian (2020) GIS for Disaster Management [134]. Routledge, Taylor & Francis Group.
- "Emergency and Disaster Management" [135] from the ESRI emergency management website.
- View Episode One Chapter Four of the Geospatial Revolution Series.
- Research the pros and cons of a policy that would make Geographic Science and Technology the “linchpin” of the US Emergency Management System
- Write your paper in accordance with the assignment and technical instructions and save using the correct file name convention.
- Submit Lesson 8 - GRADED Paper (#2)
8.3 The "All Hazards Approach"
Historically, geographers and other scholars tend to think in terms of "natural hazards" such as floods, tornadoes, hurricanes, and earthquakes, and "technological hazards" such as nuclear power plant accidents, chemical spills, or the consequences of a terrorist attack. Geographers have used geographic information science techniques to assist in preventing, planning for, responding to, and recovering from these natural and technological hazards since the advent of cartography.
Dr. Cutter, her faculty colleagues, and her entourage of graduate students from the University of South Carolina have done cutting edge work on the integration of geographic information science and hazards research.
Much of Dr. Cutter's work focused on issues of social justice. While many disasters are natural in origin, the risk to different communities varies based on how vulnerable they are to the effects of the hazard. In many cases, communities increase their vulnerability and risk by making questionable choices about what they build and where they build it. Consider these examples:
- houses built in flood plains or on geologic faults,
- communities built on barrier islands susceptible to the winds and storm surge of hurricanes,
- neighborhoods built near toxic industrial facilities,
- the clearing of wetlands for development,
- the construction of whole neighborhoods in a city nine feet below sea level.
In many cases, there are issues of race, class, gender, and age that increase or decrease both the vulnerability of populations to these risks and the ability of affected groups to recover from a disaster. Wealthy, predominantly white people, for example, can afford to live on barrier islands vulnerable to hurricanes because they can afford the risk of losing their home and have government subsidized flood insurance to rebuild their homes should they be damaged or destroyed. On the other hand, many poor, predominantly minority families (many with a single mother as head of household) have no choice but to live in areas of high risk to both technological and natural hazards. Thus, there is the significant issue of social justice that must be addressed when studying the geography of hazards, risks, and vulnerability. The social justice issue is also a significant factor for emergency management professionals as they plan to prevent and mitigate hazards and respond to and recover from disasters.
Susan Cutter was among the first scholars to recognize the intimate relationship between natural hazards and technological hazards. She identified early on that many disasters originating with a natural event would create a greater hazard as technological disasters occurred in response to the original natural disaster. A classic example would be a hurricane that causes massive damage through wind and storm surge, to include flooding the local wastewater treatment plant and destroying and exposing toxic wastes from industrial storage facilities. Think of the 2011 nuclear disaster in Fukushima, Japan caused by a tsunami. These human engineered hazards thus create a spiraling cascade of hazards, exponentially increasing the risk to affected populations. The social justice issue arises again as economically poorer populations (often minorities) often live in closer proximity to the technological hazards and have fewer resources to utilize to evacuate or safely shelter in place. This phenomenon was locally evident in every hurricane to hit the southeastern United States, and only became nationally evident during Hurricane Katrina. The recognition in academic and governmental circles of the synergy between natural and technological hazards resulted in what is now referred to as "The All Hazards Approach." This approach now dominates thinking in the emergency management community about how to prepare, respond, and recover from emergencies. In academic circles, this approach is often referred to as the "Cutter School."
Dr. Cutter's 25 years of scholarship were collected in a volume entitled Hazards, Vulnerability, and Environmental Justice, published in 2006 by Stylus Publishing.
The publisher describes the book this way:
In a world of increasingly prominent hazards and disasters, from those with their genesis in natural events such as the South Asian tsunami, to human-induced atrocities and terrorist attacks, and the profound effects of climate change, this collection provides a timely assessment of these critical themes. Presenting the top selections from Susan L. Cutter's twenty-five years of scholarship on hazards, vulnerability, and environmental justice, this collection brings together powerful and difficult-to-find literature, framed by a fresh introduction that maps out the terrain and draws out the salient themes and conclusions. This essential collection is ideal for academics and students studying hazards, risk, disasters, and environmental justice across a range of disciplines.
Susan L. Cutter is a Carolina Distinguished Professor of Geography and Director of the Hazards and Vulnerability Research Institute at the University of South Carolina. She was formerly President of the Association of American Geographers. Cutter was interviewed in 2014, and discussed the use of GIS in emergency management and the ‘why of the where’ when working with maps (How GIS Can Aid Emergency Management [136]).
Dr. Cutter had the opportunity to testify to the Research Subcommittee of the U.S. House of Representative's Committee on Science on "The Role of Vulnerability Science in Disaster Preparedness and Response" on 10 November 2005 in the wake of Hurricane Katrina. You now have the opportunity to read her testimony.
Required Reading
Read Dr. Cutter's testimony to the Research Subcommittee of the U.S. House of Representative’s Committee on Science "The Role of Vulnerability Science in Disaster Preparedness and Response." The reading can be accessed from the Lesson 8 Checklist [137]. Registered students can access a PDF of the reading in Lesson 8 in Canvas.
As you read Dr. Cutter's testimony, do some critical thinking and ask yourself:
- Dr. Cutter conducted research in the Katrina damage zone shortly after the Hurricane. She was interviewed on National Public Radio and was highly critical of the governmental response. Given her research interests, academic position, and recent experience, what was her agenda in testifying before the US Congress?
- Dr. Cutter is a geographer, an expert in the geography of hazards, risks, and vulnerability, and an important player in the emerging interdisciplinary field of "Vulnerability Science." What other disciplines might have a contribution to make to vulnerability science? How might scholars from those other disciplines have testified differently to congress?
- Dr. Cutter implicitly includes the contribution of GIScience in her testimony, and the contribution is explicit in her examples. How can GIScience contribute to reducing risk and vulnerability? Does geospatial intelligence have a role here, and, if so, in what way?
- Based on what we have studied, much of the application of GIScience to emergency management is applied geospatial intelligence. Why do academics like Dr. Cutter never make reference to geospatial intelligence in their work or public statements? Why do they seldom make reference to the NGA or other Department of Defense elements?
8.4 Federal Disaster Preparedness

Read
The terrorist attacks of September 11, 2001 prompted new thinking about disaster preparedness and response within the US federal government. With the passage of the Homeland Security Act in 2002, the Department of Homeland Security was created from all or part of 22 federal organizations as a Cabinet-level department to coordinate and unify national homeland security efforts. Thus homeland security was to encompass the preparation, protection, and response to an entire range of threats ranging from terrorism to natural disasters.
Subsequently in 2011, President Obama issued Presidential Policy Directive/PPD-8 [138] regarding national preparedness, which is intended to strengthen the security and resilience of the U.S.
Please read the following top three sections from the Presidential Policy Directive 8 to understand its purpose and scope: this includes the National Preparedness Goal, and the National Preparedness System.
Presidential Policy Directive/PPD-8 [139]
Obama, B. (2011, March 30). Presidential Policy Directive/PPD-8. Naval Post. https://www.dhs.gov/presidential-policy-directive-8-national-preparedness [140]
The National Response Framework
The National Response Framework is an essential component of the National Preparedness System outlined in PPD-8. It is designed to be an all discipline, all hazards plan applicable to all members of the government and private sector involved in any way with domestic emergency preparedness and response. It provides context for how the whole community works together and how response efforts relate to other parts of national preparedness. A working knowledge of the NRF is essential for all federal workers potentially involved in this area, as well as for state and local emergency management professionals, non-governmental organization leaders, and concerned citizens. As you review the NRF and subsequently the National Infrastructure Protection Plan, consider how geospatial intelligence capabilities might contribute to these efforts.
Required Reading
Scan through the sections of the National Response Framework. The reading can be accessed from the Lesson 8 Checklist [137]. Registered students can access a PDF of the reading in Lesson 8 in Canvas.
The National Infrastructure Protection Plan
The September 11 attacks also focused attention on the vulnerability of critical infrastructure and key resources (CI/KR) in the US to terrorist attack or exploitation. Critical infrastructure and key resources are those that are essential to national security, safety, and economic well being. The fear is that attacks on CI/KR could impact the ability of government and the economy to function and threaten the American way of life. Consider the far ranging damage to the national economy from the September 11 attacks. Not only did New York City sustain massive physical, psychological, and economic damage, but the damage to the national economy as evidenced by reduced air travel was substantial. The vulnerability of transportation systems, hazardous material facilities, and public water and food supplies are all areas of concern. Because of this, Presidential Policy Directive/PPD-21 [141] was issued. This directive focuses on strengthening and maintaining secure, functioning, and resilient critical infrastructure. One of the requirements of PPD-21 is to prepare a National Infrastructure Protection Plan (NIPP). The NIPP outlines how government and the private sector work together to manage risks and achieve security and resilience.
Required Reading
Read the Executive Summary and scan the other sections of the National Infrastructure Protection Plan. The reading can be accessed from the Lesson 8 Checklist [137]. Registered students can access a PDF of the reading in Lesson 8 in Canvas.
Homeland Security versus Homeland Defense
The Department of Homeland Security (DHS) is responsible for a wide array of tasks that constitute "homeland security." The Department of Defense has its own mission of "homeland defense." To accomplish the homeland defense mission, DOD established US Northern Command (USNORTHCOM), headquartered at Peterson Air Force Base in Colorado. Given the traditional US commitment to civilian control over the military, and legitimate concerns about military activities at home impinging on civil rights, how should homeland security and homeland defense relate?

Optional Reading
For those students who are particularly interested or involved in this topic, you may want to look at the following Joint Publications:
Homeland security is defined in the National Strategy for Homeland Security as, "a concerted national effort to prevent terrorist attacks within the United States, reduce America's vulnerability to terrorism, and minimize the damage and recover from attacks that do occur." Notice that this definition explicitly covers only terrorism and not natural or technological hazards. (This is one of the complaints about having FEMA under DHS. DHS is too focused on terrorism, even though disasters take more lives and cause more damage.) Thus it is the Department of Homeland Security's primary mission to prevent terrorist attacks within the US, and the Attorney General is responsible for investigating and prosecuting the perpetrators of terrorist attacks.
Homeland defense is defined as, "the protection of US sovereignty, territory, domestic population, and critical defense infrastructure against external threats and aggression, or other threats as directed by the President." The Department of Defense is responsible for homeland defense. However, we know that the DOD has an enormous budget and substantial capabilities to assist in domestic disaster response. Witness the resources brought to bear by LTG Raymond Honore, "The Rag'in Cajun" and his federal military task force during the response to Hurricane Katrina.
The Department of Defense is allowed to support civil authorities in domestic emergencies when authorized by the President. Defense support to civil authorities, usually referred to as "civil support," is any DOD support for domestic emergencies and designated law enforcement activities. Examples include federal troops restoring order during the Los Angeles Riots and DOD support for Hurricane Katrina. Civil support can include military forces, DOD civilian and contract personnel, and DOD agency and component assets.
As we will see in the next lesson, DOD agencies such as the National Geospatial Intelligence Agency provide essential geospatial intelligence support to FEMA and state and local agencies. The issue of classified sources and methods poses issues for such cooperation, as does the predominant military focus and culture of NGA. We will examine in the next lesson how NGA attempts to overcome these challenges.
A word of clarification is in order concerning the National Guard versus federal forces. National Guard forces (Army and Air National Guard) are organized by state and territories and are normally under the control of the state governor. This status is known as Title 32 after that section of the US Code that authorizes this arrangement. While in Title 32 status, Guardsmen serve at the direction of the governor and may carry out civil law enforcement functions such as crowd control and prevention of looting. National Guard units can be federalized by order of the President and used domestically or deployed overseas (e.g. Iraq and Afghanistan). The National Guard, along with the federal Army, Navy, Air Force, and Marine Reserves constitute the Reserve Component. Federal forces are organized under Title 10 of the US Code. When Guard units are federalized, they operate under Title 10. An important point is that Title 10 forces are prohibited from conducting civil law enforcement activities under Title 18, known as The Posse Comitatus Act of 1878. The exception to this law is in the event the President invokes the Insurrection Act, which allows him or her to order federal forces to restore order. Note that the US Coast Guard in peacetime is subordinate to the Department of Homeland Security and may become subordinate to DOD in time of war (e.g. World War II).
8.5 GIScience and Emergency Management
Geographic Information Science has proven its worth in numerous domestic emergencies, ranging from fires in California, Canada and Maui to Hurricanes Katrina, Maria and Harvey a local fire to Hurricane Katrina. Nearly every county and municipality in the US has an Emergency 911 system, which is a geographic information system optimized to route emergency assets to respond to incidents via the most efficient route. Digital cartography, remotely sensed imagery, and global positioning systems are all essential supporting technologies.
Ask Yourself
You will review several readings that highlight the contributions of geospatial technologies. As you read these works, do some critical thinking and ask yourself:
- What is the affiliation of the authors and what is their underlying agenda?
- When was the article written, and are there new developments and experiences that cast new light on the author's contentions?
- What experiences do you have that cause you to agree or disagree with the authors' contentions?
- The authors typically extol the virtues and capabilities of geospatial techniques for solving all problems. What are the limitations of geospatial techniques in emergency preparedness and response, and how can we overcome them?
As related by Tomaszewski, in his 2020 book Geographic Information Systems (GIS) for Disaster Management 2nd Edition, GIS plays an active role in each phase of the disaster cycle, from planning and preparedness, to response, to recovery, to mitigation. Per Tomaszewski, "Regardless of how GIS is utilized, one theme that emerges from any use of GIS within any disaster cycle phase, that GIS serves an information management role within disaster management activities" (p. 114).
Required Reading
Chapter 1: A Survey of GIS for Disaster Management in Tomaszewski’s 2020 textbook Geographic Information Systems (GIS) for Disaster Management, 2nd Edition.
The reading can be accessed from the Lesson 8 Checklist [137]. Registered students can access a PDF of the reading in Lesson 8 in Canvas. This resource is useful for your second paper.
Geospatial technologies have also been critical in responding to international disasters such as the Haitian Earthquake and the Japanese Tsunami and subsequent nuclear catastrophes. Review Episode One, Chapter Four of the Geospatial Revolution Series for a powerful example.
Video: Geospatial Revolution / Episode One, Chapter Four: Why We Need It (5:18)
Environmental Systems Research Institute [145] (Esri) contends that GIS is the linchpin technology for emergency management that brings practitioners together, reduces or removes data and organizational stovepipes, facilitates communications, and ultimately improves planning and response.
Required Reading
Explore the ESRI emergency management website: Emergency and Disaster Management [135]. The reading can be accessed from the Lesson 8 Checklist [137]. This resource can help you with your second paper.
As learned in the previous section regarding GeoCONOPS, geospatial technology and products play key roles in the preparation for and response to disasters. One online resource for public and government agencies that provides geospatial tools and data is the GeoPlatform. Through GeoPlatform, users have access to:
- a one-stop shop to deliver trusted, nationally consistent data and services;
- authoritative data to support informed decision-making;
- problem-solving applications and services that are built once and can be used many times across multiple Federal agencies and other organizations;
- a shared infrastructure to host data and applications;
- a national and Federal focal point where governmental, academic, private, and public data and applications can be visualized together to inform and address national and regional issues.
Additional information can be found at GeoPlatform [146].
The Federal Emergency Management Agency is responsible for coordinating the federal response to disasters. A geospatial tool provided by FEMA for disaster mitigation and response is HAZUS. See the below block for additional information regarding HAZUS [147].
Hazus is a nationally applicable standardized methodology that contains models for estimating potential losses from earthquakes, floods, and hurricanes. Hazus uses Geographic Information Systems (GIS) technology to estimate physical, economic and social impacts of disasters. It graphically illustrates the limits of identified high-risk locations due to earthquakes, hurricanes, and floods. Users can then visualize the spatial relationships between populations and other more permanently fixed geographic assets or resources for the specific hazard being modeled, a crucial function in the pre-disaster planning process.
Hazus is used for mitigation and recovery, as well as preparedness and response. Government planners, GIS specialists and emergency managers use Hazus to determine losses and the most beneficial mitigation approaches to take to minimize them. Hazus can be used in the assessment step in the mitigation planning process, which is the foundation for a community's long-term strategy to reduce disaster losses and break the cycle of disaster damage, reconstruction and repeated damage. Being ready will aid in recovery after a natural disaster.
Consider the following paper on "GIS: a common operational picture for public safety and emergency management." Read this assignment closely as it plays a key role in the reflection paper assignment.
Required Reading
Read the paper on "GIS: a common operational picture for public safety and emergency management." The reading can be accessed off of the Lesson 8 Checklist [137] page. Registered students can access a PDF of the reading in Lesson 8 in Canvas.
The advent of the Internet has revolutionized how geospatial products are disseminated to users. Products such as Google Earth make remotely sensed data available to the masses, while apps such as Google Maps make optimized route selection analysis available to average motorists. Internet dissemination methods have enormous potential in making geospatial information rapidly available to government officials and first responders across jurisdictional lines.
8.6 Paper Number 2- Policy Analysis Paper
Introduction
Esri and others in the geospatial community contend that GIScience should be the linchpin of homeland security and emergency preparedness that allows emergency management professionals and other governmental leaders to break out of their stovepipes, share information, and ultimately improve their communications and cooperation through a "Common Operational Picture" or COP. Susan Cutter similarly believes that geographers using geospatial techniques as part of "vulnerability science" should play a key role in emergency preparedness and response.
Scenario
For this assignment, your instructor is the Secretary of Homeland Security. You are an analyst in the Department of Homeland Security. You have a great opportunity to demonstrate your analytical and explanation skills to your supervisor, and to gain the notice of the Secretary of DHS. You can also kill your career by screwing this up—so no pressure.
The Secretary has an important policy decision to make. Should they approve or disapprove a policy that would make Geographic Information Science and Technology the “linchpin” of the US Emergency Management System. Your job is to do the analysis and present the Secretary with a policy paper that analyzes and evaluates the pros and cons of such a policy and conclude with a solid approve/disapprove recommendation that logically derives from your analysis. You must demonstrate your higher order and critical thinking skills. Note that you are an objective analyst with no pre-conceived conclusion. Your analysis must rely on evidence, data, and citations from reputable sources. No one cares about your personal opinion.
Assignment Details
Your assignment is to write a policy analysis paper, in the form of a memo, of 1000 words (plus or minus 10%), which is about four double-spaced pages in a 12-point font.
Your paper should utilize all of the content included in Lesson 3 [148] and be:
- concise (1000 words plus/minus 10%)
- well organized
- uses one-inch margins and Times Roman or Arial font
- uses correct citations and bibliographic references
- is generally correct in terms of spelling, grammar, punctuation
- properly formatted memo: includes "FOR TRAINING USE ONLY" in large, BOLD capital letters in the header and footer. If you feel the need to put a classification, ensure it is UNCLASSIFIED for Training Use Only.
-
Writing Guideline Refresher
Your paper should follow the guidelines you learned in Lesson 3. In order to do well, I recommend going back and reviewing the following:
- Intelligence Writing Guidelines [149]
- Technical Specifications [150]
- Doing Academic Research [151]
- And of course, review my feedback on paper #1. It is likely there are comments that will help inform your successful completion of this assignment.
Submission
Please submit your policy analysis paper in Microsoft Word Format using the following file naming convention: Lastname_Firstname_Paper_2.doc
Grading
Please see Canvas for the Lesson 8 - GRADED Paper (#2) Rubric that will be used to assess your work.
-
8.7 Summary and Final Tasks
Completion of this lesson increased your understanding of:
- Cutter's concept of the "All Hazards" approach to disaster management;
- social justice issues in the disaster management process;
- federal disaster planning and response efforts, including the NRF and NIPP, as well as the roles of DHS in Homeland Security and DOD in Homeland Defense and Civil Support;
- the capabilities and limitations of geospatial intelligence and geographic information science in support of the disaster management process;
- how geospatial intelligence can be of value to the first responder;
- how geospatial intelligence for disaster management compares with other national security applications.
Deliverable: Lesson 8 - GRADED Paper #2
When you have completed your paper, return to Canvas. Look for the Lesson 8 - GRADED Paper (#2) link where you will submit your paper. You will find directions for submitting your papers when you enter the link.
Before you move on to Lesson 9, double-check the Lesson 8 Checklist [137] to make sure you have completed all of the required activities for this lesson.
Looking Ahead
Next week we'll learn about one of FEMA's most catastrophic disasters - Hurricane Katrina - and how that has reshaped the way we do emergency management now. Lesson 9 is a case study of Hurricane Katrina capped off by your third discussion forum. It should be quite interesting as several of you might have been involved in Katrina. In our next lesson, we are going to consider:
- the use of intelligence and especially geospatial intelligence in the planning for, and response to, Hurricane Katrina;
- a synthesis of the ideas of previous lessons to critique the role of intelligence and especially geo-spatial intelligence in relation to Hurricane Katrina;
- the social justice implications for geospatial intelligence applications in Hurricane Katrina;
- future applications of geospatial intelligence for disaster management.
Lesson 9: Case Study: Hurricane Katrina
9.1 Overview
This lesson will conclude our three-week examination of emergency preparedness and disaster management. This third lesson is a historical case study of Hurricane Katrina. Your deliverable this week is a forum with two questions and an assignment. As part of your deliverable, you will research a contemporary disaster and provide a short PowerPoint presentation (see 9.6) part of which will show how the government disaster response efforts have improved (or not) since Katrina.
Lesson Objectives
At the end of this lesson, you will be able to:
- discuss and critique the use of intelligence and especially geospatial intelligence in the planning for, and response to, Hurricane Katrina;
- synthesize the ideas of previous lessons to critique the role of intelligence and especially geospatial intelligence in relation to Hurricane Katrina;
- discuss the social justice implications for geospatial intelligence applications in Hurricane Katrina;
- compare the government response to Katrina with the government response to a more recent disaster;
- speculate on future applications of geospatial intelligence for disaster management.
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 in Canvas.
9.2 Checklist
Lesson 9 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 9:
- Work through Lesson 9 in this website.
- Read:
- the Foreword, Chapter 5, and Appendix A, and scan the rest of the material in "The Federal Response to Hurricane Katrina: Lessons Learned [152]."
- the Executive Summary (6 pages) of "A Failure of Initiative [153]."If you are interested, you can access to the individual sections of the full report [154].
- the Executive Summary and scan the rest of "From Challenge to Action." [155]
- "The Worst is yet to Come: Lessons from September 11 and Hurricane Katrina. [156]" from the research paper from Donald F. Kettl of the Fels Institute of Government of the University of Pennsylvania.
- "The Geography of Social Vulnerability: Race, Class, and Catastrophe [157]" from the essay by Dr. Cutter and then examine the Understanding Katrina website [158] and peruse any other essays that interest you.
- the Executive Summary and scan the rest of "In the Wake of the Storm: Environment, Disaster, and Race after Katrina." [159]
- "Partnerships: FEMA Looks to NGA for Disaster Help" [160] from Shawna Wolin's article (page 29-30) in the July-August 2006 issue in the NGA Pathfinder magazine.
- "Results and Recommendations on the Role of Airborne and Commercial Satellite Imagery in Emergency Response [161]" from the ASPRS report.
- "The Red Pill [162]" by Kathleen Tierney.
- "NGA Makes the Difference: Hurricanes and Technology Challenges [163]" from the September-October 2005 issue of the NGA Pathfinder magazine.
- Watch Frontline's "The Storm" [164] and watch the entire video.
- Participate in the three-part "Lesson 9 - GRADED Discussion Forum (#3)."
- Create a PowerPoint comparing the government response to Katrina with the government response to a more recent disaster and upload it to one of the three discussion forums.
9.3 Hurricane Katrina
Background on Katrina and its Aftermath
Hurricane Katrina formed on 23 August 2005 and dissipated on 31 August 2005. In her nine day life, Katrina would wreak devastation across several states and destroy the city of New Orleans. Overall, Katrina would take at least 1836 lives and cause over $80 billion in damage, making it the most expensive disaster in US history. The after effects of Katrina continue to this day. The general perception is that the US disaster preparedness and response system, including all levels of government and disaster non-governmental organizations, failed in its initial response to Katrina. Thus, governments and NGOs at all levels continue to study Katrina to prevent future debacles. The political fallout from Katrina also continues as New Orleans attempts to rebuild with a population that as of 2023, is less that 80% of the pre-Katrina number.


Optional Reading
Wikipedia article on Hurricane Katrina [166]
Hurricane Katrina. (2023, Nov. 16, 2023) https://en.wikipedia.org/wiki/Hurricane_Katrina [167]
Frontline: "The Storm"
We begin our case study of Hurricane Katrina with a Frontline documentary available from the PBS website via streaming video. As an educator, I personally love Frontline as I believe it is fair, balanced, well researched, and hard hitting beyond anything on commercial television. I also love Frontline because they have over sixty of their best episodes available as streaming video for free.
Required Viewing
Access Frontline's "The Storm [164]" and watch the entire video. I also encourage you to review the website [168] for this episode and examine the Interviews, Analysis, and Timeline sections for further information. The link to the video can also be accessed from the Lesson 9 Checklist [169].
The Federal Response
President George Bush suffered severe criticism for the federal response to Hurricane Katrina. He charged his Assistant for Homeland Security and Counter-Terrorism to oversee a study that determined what went right and wrong, and what changes should be made to prepare for the next Katrina.
Required Reading
Read the Foreword, Chapter 5, and Appendix A, and scan the rest of the material in "The Federal Response to Hurricane Katrina: Lessons Learned." The reading can be accessed from the Lesson 9 Checklist. [169]
Required Reading
Read the Executive Summary (6 pages) of "A Failure of Initiative." If you are interested, you can access to the individual sections of the full report. The reading can be can be accessed from the Lesson 9 Checklist [169].

NGO Responses to Katrina
Non-Governmental Organizations play a crucial role in disaster relief. Some NGOs spring up shortly after a major disaster as groups of concerned citizens who want to help their neighbors. Other NGOs are enduring charitable organizations such as the Salvation Army that rapidly bring resources to bear in an emergency. The premier NGO for disaster relief in the United States is the American Red Cross.
The Red Cross Movement consists of the International Commission of the Red Cross/Red Crescent (ICRC), and The International Federation of the Red Cross/Red Crescent (IFRC). The ICRC based in Geneva, Switzerland is mandated by international treaty to support several functions during armed conflict including emergency humanitarian relief, protection of human rights, detainee visits, etc. The ICRC is funded by contributions by all the signatory governments to the Geneva Conventions and has a one billion Swiss Frank budget per year. The IFRC is the umbrella organization for the national Red Cross movements. Each national movement has its own charter and often has a relationship and charter from their national government to provide certain services and capabilities.
Mission Statement
The American Red Cross prevents and alleviates human suffering in the face of emergencies by mobilizing the power of volunteers and the generosity of donors.
Fundamental Principles of the International Red Cross and Red Crescent Movement
- Humanity
The International Red Cross and Red Crescent Movement, born of a desire to bring assistance without discrimination to the wounded on the battlefield, endeavours, in its international and national capacity, to prevent and alleviate human suffering wherever it may be found. Its purpose is to protect life and health and to ensure respect for the human being. It promotes mutual understanding, friendship, cooperation and lasting peace amongst all peoples. The principle of humanity expresses what the Movement places beyond anything else: the need to act in order to prevent and alleviate human suffering. Respect for human dignity and helping people—regardless of who and where they are—is paramount to everything we do.
- Impartiality
It makes no discrimination as to nationality, race, religious beliefs, class or political opinions. It endeavours to relieve the suffering of individuals, being guided solely by their needs, and to give priority to the most urgent cases of distress. Non-discrimination is one of the most important aspects of protecting human beings in human rights law, humanitarian law and refugee law. Sadly, there are many factors for which people are discriminated against. The text of this principle does not include an exhaustive list of factors. But it makes clear that no group of people will be denied services or receive preferential treatment based on anything other than their needs.
Only by acting with impartiality can we ensure the Movement is trusted by all people to assist and protect them. We therefore have systems in place to ensure we deliver our support based on people’s needs alone and prioritize the most vulnerable at all times.
- Neutrality
In order to continue to enjoy the confidence of all, the Movement may not take sides in hostilities or engage at any time in controversies of a political, racial, religious or ideological nature. The Movement must not take sides, or be regarded as doing so, either in its speech or actions at any time or place. Neutrality ensures the Movement has the confidence of all and can provide humanitarian support to all. Embodying the principle of neutrality at all times ensures the Movement can provide medical assistance to civilians and wounded or detained fighters during hostilities without being perceived as interfering in conflict. It is of the utmost importance that all parties in a conflict understand and respect the humanitarian role of a National Society.
- Independence
The Movement is independent. The National Societies, while auxiliaries in the humanitarian services of their governments and subject to the laws of their respective countries, must always maintain their autonomy so that they may be able at all times to act in accordance with the principles of the Movement. The principle of independence means that the Movement must resist any interference—be it political, ideological or economic—capable of diverting it from embodying the principles of humanity, impartiality and neutrality. It is only by being truly independent that the Movement can respect these principles. Independence not only relates to the relationship between National Societies and States, but also between National Societies and any other forms of power or influence, such as religions, political parties, companies and so on.
- Voluntary Service
It is a voluntary relief movement not prompted in any manner by desire for gain. The principle of voluntary service represents the common motivation uniting all those working within the Movement: a desire to help others. It is both a source of inspiration and a statement of solidarity. Whether members volunteer without pay or with some form of acknowledgement or even modest remuneration, it is not inspired by desire for financial gain but by individual commitment and devotion to the humanitarian purpose. This is freely chosen and accepted as part of the service the Movement provides to the community.
- Unity
There can be only one Red Cross or one Red Crescent Society in any one country. It must be open to all. It must carry on its humanitarian work throughout its territory. Having only one Red Cross or Red Crescent Society in any given country ensures it can work efficiently. It avoids any risk of confusion in the public mind and means all people and communities are represented by one organization. A National Society must be active in all parts of the country so that even the hardest-to-reach communities can benefit from support when needed. This doesn’t mean that the level of activities must always be the same country-wide—the principle of impartiality may justify that certain areas need more support where the needs are greater. Similarly, National Societies must not discriminate when recruiting volunteers. They must ensure their membership includes a broad spectrum of people across the population so that humanitarian assistance is delivered to all people, by all people.
- Universality
The International Red Cross and Red Crescent Movement, in which all Societies have equal status and share equal responsibilities and duties in helping each other, is worldwide. The universality of suffering requires a universal response. It is one of the Movement’s great strengths that we are present in virtually every country in the world through our 191 member National Societies. This principle also means that National Societies have a collective responsibility to support each other’s development and to work together in partnership and solidarity during disasters, for the benefit of all. When it comes to decision-making within the Movement, the principle of universality ensures that all National Societies have an equal vote during Statutory Meetings irrespective of their size or wealth.
The American Red Cross plays a key role in American disaster preparedness and response. While ARC volunteers made significant contributions during Katrina, the organization acknowledged shortcomings within its operations. In an effort to improve and be prepared for future Katrinas, the ARC published "From Challenge to Action: American Red Cross Actions To Improve and Enhance Its Disaster Response and Related Capabilities For the 2006 Hurricane Season and Beyond [170]" in June 2006.
Required Reading
Read the Executive Summary and scan the rest of "From Challenge to Action" for a sense of the challenges Katrina posed for a major American NGO and the ARC's plans for change. The reading can be accessed from the Lesson 9 Checklist [169].
The Worst is yet to Come
Katrina was a disaster, but some would say the catastrophe was our response to the storm. The terrorist attacks of September 11, 2001 and Katrina caused serious consideration of the American ability to deal with the consequences of a serious natural or technological disaster. Political leaders, scholars, and citizens ask the legitimate question of what will America do as a nation to be prepared for the next Katrina, nuclear accident, or major terrorist attack?
Required Reading
Read the following research paper from Donald F. Kettl of the Fels Institute of Government of the University of Pennsylvania, entitled "The Worst is yet to Come: Lessons from September 11 and Hurricane Katrina." The reading can be accessed from the Lesson 9 Checklist [169].
9.4 Social Justice Issues
As we learned in a previous lesson, people experience risk and vulnerability to hazards differently. Quite often this is based on characteristics of social class, race, gender, and age. Hurricane Katrina brought this home to the American people as never seen before. The news media played a major role in highlighting the inequities and social justice issues Katrina made evident.
My experience is that many GIScience students are unaware of the social justice implications of GIS&T. These students often times see the technology as a neutral tool that supports good decision making. This impression is wrong. Every time a geospatial analyst makes a decision about what data or technique to use, there are potential social justice issues. At best, the non-critical geospatial analysts may make choices without thinking about the implications for traditionally disadvantaged groups. At worst, the analysts may make conscious choices to use data sets and methods that will discriminate against certain groups to the benefit of others for reasons of profit, power, influence, or favor with policy makers. My challenge to you is to recognize the implications in your choice of data, methods, and your analytical outcomes in regards to social justice issues. The technology may be value free and neutral, but the humans behind the technology are not.
Susan Cutter on Hurricane Katrina
The Social Science Research Council [171] responded to Hurricane Katrina with an online project called "Understanding Katrina: Perspectives from the Social Sciences." As the SSRC puts it:
As analyses and "spin" of the Katrina crisis grow, we confront the sort of public issue to which a social science response is urgently needed. Accordingly, the SSRC has organized this forum addressing the implications of the tragedy that extend beyond "natural disaster," "engineering failures," "cronyism" or other categories of interpretation that do not directly examine the underlying issues-political, social and economic-laid bare by the events surrounding Katrina.
The SSRC believes the underlying failures of Katrina go far deeper than weather, bad levees, or good old boy government. The social science scholars involved seek to understand the deeper implications of underlying issues.
Dr. Susan Cutter, whom you will recall from the previous lesson, contributed the Understanding Katrina project with the essay "The Geography of Social Vulnerability: Race, Class, and Catastrophe [157]". See reading below.
Required Reading
Read Dr. Cutter's essay on "The Geography of Social Vulnerability: Race, Class, and Catastrophe [172]," and then examine the Understanding Katrina website [173] and peruse any other essays that interest you. The links can be accessed from the Lesson 9 Checklist [169].

In the Wake of the Storm
The Russell Sage Foundation [174] was established in 1907 by Mrs. Margaret Olivia Sage to foster the improvement of social and living conditions in the US. The foundation does this by fostering the development and dissemination of knowledge about US political, social, and economic problems. In the wake of Katrina, the foundation sponsored research on the social justice implications of Katrina. The resulting report entitled "In the Wake of the Storm: Environment, Disaster, and Race after Katrina [175]" is a major contribution in understanding the social justice issues related to hazards, risks, and vulnerability.
Required Reading
Read the Executive Summary and scan the rest of "In the Wake of the Storm: Environment, Disaster, and Race after Katrina." The reading can be accessed from the Lesson 9 Checklist [169].
9.5 Geospatial Intelligence and Katrina
The NGA and Katrina
Government and private sector geospatial intelligence practitioners have good reason to be proud of the contribution of GIS&T to Katrina response and recovery efforts. The National Geospatial-Intelligence Agency was mentioned in the "Federal Response to Hurricane Katrina" report in Appendix B on "What Went Right":
The National Geospatial-Intelligence Agency (NGA) started collecting key infrastructure-related information (i.e. on airports, hospitals, police stations, emergency operations centers, highways, schools, etc.) well in advance of landfall and got this information into the hands of Federal, State, and local first responders in the affected region. As the storm was tracked, NGA pre-deployed analysts and mobile systems to the affected areas that provided expertise and information on the ground and facilitated the delivery of additional information from NGA offices elsewhere. Because they had assets in place and focused on the region, NGA provided the first comprehensive overview of the damage resulting from the hurricane and flood. NGA merged imagery with other information, creating hundreds of intelligence products per day that could be used and applied by response professionals to aid in decision-making. NGA assessments were multi-dimensional, timely, relevant, and continuous. They addressed many issues, including but not limited to: recovery planning and operations, transportation infrastructure, critical and catastrophic damage, dike stability and breaches, industry damage, and hazard spills. The NGA World Wide Navigational Warning Service also provided navigation information to the U.S. Navy, Merchant Marine, and Coast Guard, and relayed messages from the National Weather Service to people at sea. NGA also aided in the location and recovery of oil platforms. The imagery activities of NGA were essential to the restoration of critical infrastructure." See Also: U.S. National Geospatial Intelligence Agency, "Geospatial Intelligence Aids Hurricane Recovery Efforts," news release, September 7, 2005.
NGA is proud of its contribution to hurricane preparedness and relief efforts.
Required Reading
Read the September-October 2005 issue of the NGA Pathfinder magazine. The issue title is "NGA Makes the Difference: Hurricanes and Technology Challenges." The issue can be accessed from the Lesson 9 Checklist [169].
Many of my students in this course are geospatial analysts for NGA or the military. Shawna Wolin was a student in the first offering of this class, and she is the co-author of an article in the July-August 2006 NGA Pathfinder magazine.
Required Reading
Read Shawna Wolin's article "Partnerships: FEMA Looks to NGA for Disaster Help" (page 29-30) in the July-August 2006 issue of the NGA Pathfinder magazine for insight on how a classmate might be directly involved in the issues we study. The reading can be accessed from the Lesson 9 Checklist [169].
A Critical Look
My mission in teaching this course is to teach you to use higher order thinking skills and, most importantly, to be CRITICAL THINKERS. So let me tell you a story about trying to craft this lesson. The Penn State GEOINT faculty paid a visit to Washington to talk to key players in the geospatial intelligence business for national security, disaster preparedness, and international disaster relief. This included visiting the NGA College at Fort Belvoir and FEMA Headquarters in Washington, DC. To make a long story short, all the agency representatives thought this course and program were a great idea. They especially liked the critical thinking component of this course. However, no one wanted to take any risk by providing any unclassified case studies that were self-critical of their own operations. Perhaps these case studies do not exist or they are classified and unavailable. What is available from NGA is public affairs material like the Pathfinder magazine. Now, do not take me wrong. I have some background with the world of secrets and I understand protecting sensitive information and sources and methods. However, my experience and personal opinion is that too often secrecy is used to prevent true critical analysis, which is essential to process and produce improvement.
You just read several articles on NGA contributions during Katrina. Let me tell you about an interview with a key geospatial player from FEMA and that person's insights on NGA support for FEMA during Hurricane Katrina. (As the person did not respond to a request to provide written notes or participate in our forum, their privacy will be respected, and they will remain unnamed.)
The FEMA geospatial analysts had numerous requirements for imagery, data, and processed geospatial analytical products. NGA was on the scene and highly motivated to help. The problem was one of culture and orientation.
A historical conversation from a FEMA responder to Hurricane Katrina and some of the issues they noted:
- There were issues about data sharing due to the classified nature of some of the collection systems. Fortunately, commercial imagery solved many of these problems. However, the culture of secrecy hinders interagency coordination between defense oriented agencies such as NGA, and other federal, state, local, and NGO agencies who do not share that culture nor have the required clearances.
- NGA did not understand FEMA procedures and processes and thus did not always provide usable products. For example, FEMA must do damage assessments at various scales to include house by house assessments. These assessments drive the amount of relief funds that FEMA provides to individual homeowners. Katrina caused devastation on a scale that overwhelmed traditional ground damage assessment survey methods. Geospatial approaches seemed a natural solution to conduct damage assessment on such destruction. NGA used remote sensing products processed with GIS to provide damage assessment maps. Unfortunately, the map data did not suit the needs of FEMA and was unusable. The issue was educating the NGA analysts on FEMA customer needs, and having NGA be nimble enough to understand and craft technical solutions capable of creating useful products in a timely fashion.
- FEMA is a civilian agency that has been in crisis for over a decade. NGA is a Department of Defense combat support agency, as well as a member of the national intelligence community. There are cultural gaps between NGA (DOD really) and FEMA that get in the way of truly seamless interagency coordination.
(Note to students: consider for your case study in the related Canvas Discussion forum- Fema was in crisis at the time- is this still the case? Or how have things changed?)
Now, for those of you at NGA who may have worked Katrina and might be fuming, do not take the above observations as a criticism of you or NGA. My point is that to get better, you have to be willing to take a hard and candid look at what went wrong, so that you can get better for the next time. Those of us outside the federal agencies hope they are doing this internally, because they certainly are not doing it in view of the public. And that is a shame because there are citizens and scholars who might well have an outside perspective useful to the discussion.
Now consider the lessons learned from members of the American Society of Photogrammetry and Remote Sensing (ASPRS) who were involved in Katrina. Read the report below and then look over the resources on the ASPRS website [176]. The presentations are especially interesting. Andrew MacInnes of Plaquemines Parrish, LA is a graduate of the Penn State online masters in GIScience Program. His presentation on "Airborne and Satellite Imagery Use and Collection for Katrina and Rita is very interesting, and it has some amazing images.
Required Reading
Read the ASPRS report "Results and Recommendations on the Role of Airborne and Commercial Satellite Imagery in Emergency Response". The report can be accessed from the Lesson 9 Checklist [169].
As a final reading, consider this most interesting essay from the SSRC Understanding Katrina Project. Note the author's academic background and affiliation. Consider the implications of her insights for both geospatial intelligence and the broader issues we have been studying.
Required Reading
Read "The Red Pill" by Kathleen Tierney. The reading can be accessed from the Lesson 9 Checklist [169].
Reference:
National Geospatial Intelligence Agency (n.d.). Geospatial Intelligence Aids Hurricane Recovery Efforts. Retrieved Nov. 16, 2023 from https://www.fgdc.gov/organization/steering-committee/meeting-minutes/oct... [177].
9.6 Summary and Final Tasks
Summary
This lesson was a case study of Hurricane Katrina, and it concludes our three-lesson section on domestic disaster preparedness. In this section of the course, we examined the fundamentals of emergency management, including the National Response Plan and the National Incident Management System. We also examined the very important and often ignored issue of social justice in disaster preparedness and response, as well as the contribution of GIS&T to emergency management. This final case study of Hurricane Katrina allowed you to:
- discuss and critique the use of intelligence and especially geospatial intelligence in the planning for, and response to, Hurricane Katrina;
- synthesize the ideas of previous lessons to critique the role of intelligence and especially geo-spatial intelligence in relation to Hurricane Katrina;
- discuss the social justice implications for geospatial intelligence applications in Hurricane Katrina;
- compare the government response to Katrina with the government response to a more recent disaster;
- speculate on future applications of geospatial intelligence for disaster management.
Final Tasks
Deliverable: Lesson 9 - GRADED Discussion Forum (#3)
Return to Lesson 9 in Canvas. Look for the Lesson 9 - GRADED Discussion Forum (#3), where you will find the three required questions and an optional question for this assignment. The minimum requirement is that each of you post one primary response to each of my questions and comment on at least three of your classmates' posts. (Note: for the second discussion forum question, you are required to create a PowerPoint comparing the government response to Katrina with the government response to a more recent disaster and upload it to the corresponding discussion forum.)
Please post your primary response to the questions by Sunday evening to allow time for everyone to post comments by Tuesday night.
Before you move on to Lesson 10, double-check the Lesson 9 Checklist [169] to make sure you have completed all of the required activities for this lesson.
Looking Ahead
Congratulations!! You have completed lessons 1 through 9 and are now ready to move on to the final lesson - Lesson 10 - Trends in Geospatial Intelligence.
For the final lesson, we will explore some other applications of geospatial intelligence and reflect on the future of the field. I will also ask that you complete two course surveys that will provide feedback to PSU and to me regarding the course content, delivery, graded requirements, etc. This feedback is essential to improving the course, so I appreciate your candid responses.
See you at the Critique!
Lesson 10: Trends in Geospatial Intelligence
10.1 Overview
In this lesson, we will be exploring some additional applications of geospatial intelligence, including areas of US Law Enforcement, International Human Relief operations, and Cyberspace applications. In addition, we are asking you to do your own investigation into new applications. We will have an abbreviated discussion at the end of the lesson.
Lesson Objectives
At the end of this lesson, you will be able to:
- discuss some of the applications of geospatial intelligence to law enforcement analysis;
- discuss the application of geospatial intelligence to international humanitarian aid and disaster relief operations;
- discuss some GEOINT and cyberspace considerations.
Questions?
If you have any questions now or at any point during this week, please feel free to post them to the GEOG 882 - General Discussion Forum in Canvas.
10.2 Checklist
Lesson 10 will take us one week to complete. Please refer to the Calendar in Canvas for specific time frames and due dates. Specific directions for the assignments below can be found within this lesson.
Complete the following steps to complete Lesson 10:
- Work through Lesson 10 on this website.
- Read: (the following are available in Canvas)
- "Crime Mapping and Crime Forecasting [178]" from the webpage of the National Institute of Justice.
- "Remote Sensing and Humanitarian Aid: A Lifesaving Combination" [179] from www.esa.int [180].
- "Using satellite imagery to improve emergency relief" [181] from the Humanitarian Practice Network.
- "UN Uses GIS to Promote Peace and Provide Aid" [182] from esri.com.
- The Executive Summary of "Mapping the Risks" [183] from the RAND Corporation.
- "National Cybersecurity Strategy [184]" [185] from the whitehouse.gov.
- "Department of Defense Strategy for Operating in Cyberspace" [186] from the US Dept. of Commerce.
- Skim the "Introductory Guide to Crime Analysis and Mapping [187]" from the US Dept. of Justice (PSU Login Required)*.
- Watch "The Geospatial Revolution Episode One, Chapter Four: Why We Need It” (embedded on page 10.6 in the lesson).
- Watch "Has the Cyber War Threat Been Overly Exaggerated?" (embedded on page 10.7 in the lesson).
- Participate in "Lesson 10 - GRADED Discussion Forum (#4)."
- Complete Penn State's SEEQ (Student Educational Experience Questionnaire).
- Provide feedback on the course to the instructors.
10.3 Geospatial Intelligence in Law Enforcement Analysis
Law enforcement analysis promotes effective policing in areas such as conducting investigations and intelligence operations, planning and managing resources, and deterring criminal activity. Geographic information science and technology (GIS&T) and geospatial intelligence (GEOINT) assist in these areas. From the beginning of an investigation to its conclusion, analysis can aid in determining what is needed in an investigation and where it can be collected. Analytical charts, maps, and reports help guide the operation. Analysis can identify crime trends and provide strategic assessments that assist policy makers in resource allocation and long-term planning. Law enforcement analysis supports the deterrence and prevention of crime through identifying patterns of criminal incidents, forecasting threats to the community, assisting in the effective deployment of patrol resources, and supporting community policing efforts.
Before discussing the various applications of GIS&T and GEOINT in law enforcement analysis, it is useful to examine several behavioral theories, looking at them from a geospatial perspective. These theories are not discussed in detail, but they do build upon each other. The material includes references for additional research. Individuals who have studied criminology might be familiar with these theories. These theories also have applications to studying terrorism.
Behavioral Theories from a Geospatial Perspective
Rational Choice Theory
Choices are made based on opportunities and rewards.
George Homans built a series of explanatory principles based on the assumption that people make rational choices about how to maximize benefits in light of their priorities. This perspective suggests that individuals, such as criminals and terrorists, will select their targets and define the means to achieve their goals in an explainable manner. (Homans, G. 1974. Social Behavior, Its Elementary Forms, 2nd ed. New York: Harcourt, Brace, Jovanovich)
Routine Activity Theory
Opportunities change based on changes in behavior.
Lawrence Cohen and Marcus Felson studied crime as an event and highlighted the relationship of these events to space and time. Routine activity theory explains an event through three essential elements that converge in space and time – the potential offender with the capacity to commit an offense, a suitable target or victim, and the absence of guardians capable of protecting the target or victim. (Cohen, L. & Felson, M. 1979. Social change and crime rate trends: A routine activity approach. American Sociological Review, 44, 588-608)
Crime Pattern Theory
Crimes occur where offender’s space overlaps with victim’s space.
Crime pattern theory highlights spatial ties connecting crime, targets, and patterns of movement of offenders. The theory relates that offenders commit crimes near areas where they spend most of their time and along routes that connect them. The concept of space is essential to crime pattern theory because the characteristics of spaces influence the likelihood of a crime. (Brantingham, P. L. & Brantingham, P. J. 1993. Environmental, routine, and situation: Toward a pattern theory of crime. Advances in Criminological Theory 5: 259-294)
Environmental Design Theory
Identify and alter geographical characteristics that contribute to criminal predation.
Crime prevention through environmental design is a micro/neighborhood approach to identifying conditions of the physical and social environment that provide opportunities for criminality. It uses such mechanisms as real and symbolic barriers, defined areas of influence, and opportunities for surveillance to bring an environment under the control of its residents (Jeffrey, C. R. 1971. Crime Prevention Through Environmental Design. Thousand Oaks, CA: Sage. Newman, O. 1973. Defensible Space. New York: Collier Books)
10.4 Applications of GIS&T and GEOINT in Law Enforcement Analysis
Following are several analytic techniques that can be used to produce geospatial intelligence, considering the nature of intelligence and the grounding of the previously described theories.
Crime Mapping
Crime mapping is the process of using a geographic information system to conduct spatial analysis of crime problems and other police-related issues. It facilitates visual and statistical analyses of crime, allows linkages based on common variables, and helps to communicate results of analysis. (Boba, R. 2022. Crime Analysis and Crime Mapping 5th edition. Thousand Oaks, CA: Sage.)
Police data includes: criminal incidents, arrests, calls for service, and traffic crashes and incidents. To see how an agency has incorporated crime mapping, go to the Philadelphia Police Department's Crime Maps and Stats [188]site.
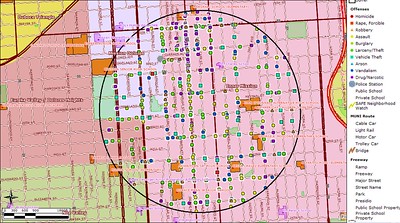
Geographic Distribution Analysis
Geographic distribution analysis examines the occurrence of events over a geographic area to determine what can be concluded about the activity. To complete a geographic distribution analysis, data on the locations of activities are collected and plotted on a map. Then, the information is reviewed to create a summary of what is depicted and from which to draw conclusions as to what the information means. (Peterson, M. B. 1994. Applications in Criminal Analysis. Westport, CT: Greenwood)
The following is an interactive website from Esri on crime mapping that allows you to analyze the geographic distribution of crime in the US versus various demographics. Crime Mapping [193].
Geographic Flow Chart
The map below depicts a geographic flow chart that shows the movement of activities from one location to another. To complete this analysis, an analyst would summarize the information and draw conclusions about the activity to provide to a decision-maker.
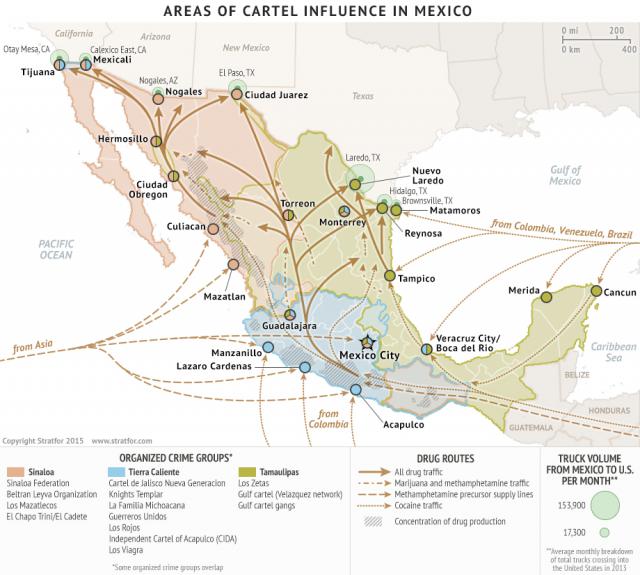
Spatial Analysis
Spatial analysis explores relationships within and between data in space and provides the ability to define characteristics of the data as they relate to other information. (Steinberg, S. L. & Steinberg, S. J. 2015. GIS Research Methods. Redlands, CA: Esri Press) In the criminal justice field, spatial analysis creates a snapshot of crime incidents and related factors within a geographic area. Looking for patterns is one aspect of spatial analysis. Patterns can be found in locations, distances, direction, and hot spots. One application of spatial analysis in the fight against human trafficking can be found at A Global Display of Human Trafficking Incidents and News. [195]
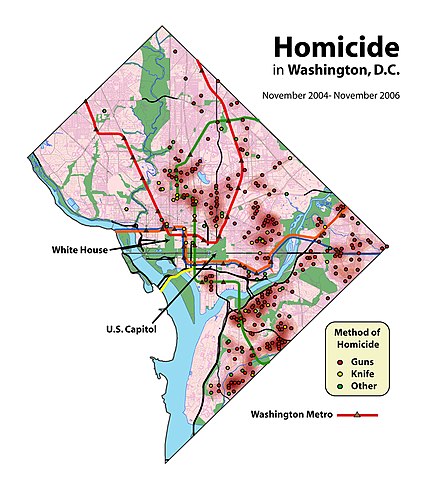
Public Domain Image:
Credit: Homicides in Washington, DC [196] by User:Aude [197] from Wikimedia [198](Public Domain [199]).
Using Other Applications of GIS&T and GEOINT in Criminal Investigations and Law Enforcement
You can use GIS&T and GEOINT for other purposes as well. Some examples include:
- Looking up sex offenders to assist in child abduction cases using an application such as Family Watchdog [200].
- Tracking motor vehicle thefts using tools such as OnStar [201] and Lojack [202].
10.5 GEOINT in Law Enforcement Readings
You will explore a website and a publication that lay out the basics of crime analysis and crime map production.
The website is from the National Institute of Justice (NIJ). The NIJ is the research and development and evaluation agency of the United States Department of Justice.
The US Department of Justice Office of Community Oriented Policing Services (COPS) was established in 1994. Since then, COPS has provided over $11.3 billion in assistance to state and local law enforcement agencies that included hiring additional police officers and running specialized training and workshops. In 2001 COPS funded the Police Foundation to conduct an “Introduction to Crime Analysis Mapping and Problem Solving” training course.
Required Readings
- Explore the NIJ website content [178] on Mapping and Analysis for Public Safety.
- Skim the Introductory Guide to Crime Analysis and Mapping. If you found this publication useful, the author, Rachel Boba Santos, published a 5th edition of Crime Analysis with Crime Mapping, SAGE, 2022.
Readings can be accessed from the Lesson 10 Checklist [203].
As you explore the NIJ website and the Guide to Crime Analysis and Mapping, do some critical thinking and consider these questions:
- Is the application of GIS&T to law enforcement and criminal justice really an application of geospatial intelligence? Why or why not?
- Given what you know of the application of geospatial intelligence to US national security activities, compare and contrast how the law enforcement community leverages GIS&T and the intelligence process.
- Given that GIS&T includes at least the four subfields of cartography, remote sensing, GIS, and GPS, consider the central role that mapping seems to play in crime analysis. Is the law enforcement community missing an opportunity to leverage the other components of GIS&T and geospatial intelligence?
10.6 Geospatial Intelligence in Support of International Humanitarian Relief (IHR)
International disasters can be even more complex than domestic disasters. In the last lesson on Hurricane Katrina, we saw the challenges faced by the US government, state and local governments, and NGOs in dealing with a major hurricane disaster. Consider, however, that only one set of national laws applied, most people spoke the same language, and the resources of the rest of the US could be brought to bear. Now consider the challenge for US government and NGO personnel when working on an international disaster relief mission. The host nation government is in charge and their laws apply. There could be several affected nations, thus there could be several sets of laws and several different languages with which to contend. The affected nation could quite probably be a developing world nation with far less infrastructure and fewer resources than what is found in the US. The affected populations may have a far higher number of citizens who are of a lower socio-economic status, with far fewer personal resources than in the US (think social justice issues on a much larger scale). US government elements will usually work with several other partner nations providing relief, as well as many more local and international NGOs. The point here is that international humanitarian relief operations can be very complex.
Just as GIS&T has a major contribution to make to domestic disaster preparedness and relief, it also has great potential for support of international humanitarian aid and relief operations. Many of the same challenges found in domestic activities apply to international efforts. US Government geospatial intelligence (already challenged at the inter-agency level) faces even greater challenges and constraints when dealing with partner nations and organizations that might not be particularly sympathetic or friendly to the United States. Read the following selections and consider how geospatial intelligence can be leveraged by governments, intergovernmental organizations (IGOs), and nongovernmental organizations (NGOs) to support international disaster relief and humanitarian aid agencies. Consider the limitations faced by the US government and how such limitations might be overcome.
You will watch a short video from the Geospatial Revolution series on applications of geospatial technology in the 2010 Haitian Earthquake. You will then review three short articles that approach this topic from different perspectives.
Required Viewing and Reading
Mirroring the question concerning geospatial intelligence and law enforcement, do some critical thinking and consider these questions as you review the material below:
- Is the application of GIS&T to international disaster relief and humanitarian aid really an application of geospatial intelligence? Why or why not?
- Given what you know of the application of geospatial intelligence to US national security activities, compare and contrast how the international relief community (especially non-governmental organizations) uses GIS&T and geospatial intelligence.
- Is a geospatial intelligence approach appropriate for the different elements of the international relief community (why or why not)?
Required Viewing
Video: Geospatial Revolution / Episode One (6:37)
DIGITAL FEMALE VOICE: Welcome to The Geospatial Revolution.
CAPT. ARTURO DERRYBERRY: In a world where everybody's texting, geospatial technology is critical to understanding what's happening at a particular location.
MARK BRENDER: It's the speed of the Internet. It's a capability of remote sensing satellites. It's software like Google Earth. Taken all together, we have an explosion in the way we view the earth.
WALTER SCOTT: Everybody's somewhere. Everything's someplace. And a map is a way of organizing of all that information.
DAVID COWEN: It's information from aircraft, from satellites, it can be a collection of information from a tower that you've set up.
KASS GREEN: We've been using maps for hundreds and hundreds of years to know where we are. Now, that nice lady tells me which way to turn.
GPS: Turn right, then turn left.
ADENA SCHUTZBERG: Virtually all the information that you're sharing with anybody these days has some kind of geospatial tag on it.
PATRICK MEIER: It's really the human element. There's basically this entire information ecosystem that we have access to now.
JOE FRANCICA: I can receive information. I can transmit information. I can broadcast my location. And that is revolutionary.
JAN VAN SICKLE: It's amazing. It's cutting edge. It's, well, changing the world.
GPS: In 1/10th mile, turn right at stop sign.
DAVID DIBIASE: Some people call this a GPS. It's not. It's a GPS receiver. It is, I think it's fair to say, a miracle of science and technology. It's able to collect signals from global positioning satellites far up in space.
ADENA SCHUTZBERG: Each one of them is every moment of every day saying, this is the location I'm at in orbit around the Earth. If you know where you are with respect to three satellite points, you can use mathematics to determine where you must be on the face of the Earth.
DAVID DIBIASE: There are millions of coordinates encoded in this box.
GPS: Re-calculating.
DAVID DIBIASE: And it can take those coordinates and render a map on the screen for you.
GPS: Turn left on Whitehall Road. Then, turn left in 0.3 miles.
DAVID DIBIASE: Where do all those coordinates come from? Where do those streets come from? Lots and lots of people driving special cars, continuously up and down every single road and digitizing those roads into a database that then can be downloaded into this little box.
MICHAEL JONES: There's nothing new about mapping. You can imagine, without being able to talk, somebody showing where you're going, and draw a line, show where the river is, and X where they are now, and X where they're going to go.
MARK BRENDER: Viewing the earth has really been based on technology. The Babylonians etched the lay of the land on clay tablets in 2300 BC. And then in the 15th century, with the advent of printing, they started making maps using wooden blocks.
DAVID DIBIASE: Surveyors would map by making measurements in front of them to a reference point and then back behind to the reference point they had just passed. That information had to be transcribed into a map.
DAVID COWEN: From in the air, it's as if we sent out thousands of surveyors all at once. Remotely sensed data provides highly accurate measurements of the earth and the features upon it.
[ROCKET LAUNCHING]
GEN. C. ROBERT KEHLER: We rely on satellites for pictures of the earth for communications, for navigation, for weather. Geospatial technology has become woven throughout the fabric of how we live.
JACK DANGERMOND: About 50 years ago, people came along and started building on big-ol' mainframes. Geographic information systems, which would integrate on a map information about culture, about population, about demographics, about physical environment. GIS allows us to bring it all together.
JAN VAN SICKLE: I used the first commercial GPS receiver-- took two men to carry it-- our antenna was a meter square piece of aluminum. We had to have a generator for it. Massive batteries.
TIM TRAINOR: The Census Bureau in the United States needed to capture all of the mine work for roads, railroads, hydrography, and then boundaries. That formed the basis of the first TIGER files in the late 1980s in support of the 1990 census. TIGER was an impetus to technological developments like MapQuest, Yahoo, followed by Google.
MATT O'CONNELL: Google Earth introduced people to the coolness of place. I am here. Where's the nearest Starbucks? Or, where's the nearest hospital?
CHRIS PENDLETON: Now, we're all carrying around GPS. We've got really rich interfaces that allow us to do things that we would only imagine previously.
MICHAEL JONES: On a mobile device, you are the center of the map, and the city is around you, not you see a city and then look for yourself on the map. It's putting you in the map.
[HONK]
[PHONE RINGING]
ADENA SCHUTZBERG: Say you find yourself in a location that you don't know very well. You might want to find a place to have dinner. Well, what places are around, and which places have other people rated very highly? Maybe you want a particular kind of food within a 15-minute walk.
DAVID COWEN: I've got not only a restaurant, but I've got the map. I can find the reviews of it. I can find out what the menu is.
CHRIS PENDLETON: We're moving away from me having to actively search for something to now searches telling me what I should check out that might be interesting to me. These are the things where location and search start to come together.
JOE FRANCICA: We are becoming individual sensors. We are creating this huge sensor network of people holding these mobile devices. And that information is two-way.
DAVID COWEN: It's not just a passive collection, listen to your GPS technology, tell you how to get to someplace. You're going to say, wait a minute. I see a problem. I want to report that problem. I want to see that someone's going to respond to that.
JEAN PHILIPPE FRANTZ: We were playing basketball. We see the ground keep on moving. I saw a lot of people-- some of them dying. Like, the ceiling killed them.
JEAN-ROBERT DUROCHER: I have both extended family members and close family members who live in Haiti. And the first reaction was more like surreal. Is this really happening?
CAPT. ARTURO DERRYBERRY: We needed to know where we could go in, and so we use geospatial technology to prepare the area with information before we even got there.
CRAIG CLARKE: Approximately 2/3 of the cell towers stayed active. And aid workers and Haitian nationals are posting information saying that they needed help.
PATRICK MEIER: I was watching CNN and immediately called our Ushahidi tech lead in Atlanta. I told him that we needed to move and set up an Ushahidi platform for Haiti.
JAROSLAV VALUCH: Ushahidi's an open-source platform for crowdsourcing crisis information. Basically, that means you are following the local media, Twitter, Facebook, text messages-- any sort of information you can get. Once you aggregate this information and map it, you have a real-time picture of the actual situation on the ground. This information can be used by rescue workers or anyone.
PATRICK MEIER: With an Ushahidi platform, you can decide what kind of map you want to use. OpenStreetMap uses crowdsourcing to do street mapping. And within a few days, OpenStreetMap had the most detailed map of Haiti that was available.
KATE CHAPMAN: There were maps of Haiti before the earthquake, but they just weren't up to date anymore. So people started using donated satellite imagery to trace, in OpenStreetMap, collapsed buildings, clinics, hospitals.
PATRICK MEIER: Within a week or so, we had trained over 100 individuals at Tufts University to map the incidents and the alerts. And then a text number, 4636, was set up for reporting. But these text messages were all going to be in Creole. So we started getting as many of Creole-speaking volunteers as possible.
JEAN-ROBERT DUROCHER: I found out about 4636 effort through a friend of mine. So I got online and started getting involved, basically staying up late after putting the kids to bed, trying to translate as many text messages as I could.
[CONVERSING]
There was this energy. People from, basically, all over the world creating sort of like a support system over the Internet.
CRAIG CLARKE: A soccer stadium was serving as a camp for displaced persons. But we didn't know it was there. Through Ushahidi's mapping ability, we knew that that would be a location to take aid. We wouldn't have seen it without them.
CAPT. ARTURO DERRYBERRY: Ushahidi alerted the world that if you've got needs in Haiti, or you're trapped in a building, or you're out of food, or you're injured and you need help, that you can alert us.
CRAIG CLARKE: Whether you are that person in Des Moines, Iowa who's reading Twitter or Facebook or you're a Haitian on the ground, with mobile technology and open sourcing information, you're suddenly empowered.
JEAN-ROBERT DUROCHER: Being able to stay online translating those text messages, you know that that information will be forwarded directly to a specific aid organization. That really felt like almost I was on the ground helping.
JACK DANGERMOND: A map is worth a million words. Maps communicate with everybody. That's powerful. You can make a difference. And you can look at relationships, and patterns, and processes, and models-- help save the world.
JOE FRANCICA: I don't think we can project 50 years out. But given what we're seeing today, it's just a fantastic explosion of location technology and location based data. And now, we have the devices to read it, and capture it, and visualize it. And that's something that's really helping the geospatial revolution truly explode.
WALTER SCOTT: Revolutions rarely end up the way they started. That's almost a definition of a revolution.
Required Readings
- "Remote Sensing and Humanitarian Aid: A Lifesaving Combination."
- "Using satellite imagery to improve emergency relief."
- "UN Uses GIS to Promote Peace and Provide Aid."
Readings can be accessed from the Lesson 10 Checklist [203] (and from Canvas).
10.7 Geospatial Intelligence in Cyberspace
Dr. Michael Thomas is the original author of Geography 489 [205] " Cyber-Geography in Geospatial Intelligence", and is also one of the instructors for Geography 882. He has worked as an analyst for HQEUCOM in Stuttgart, Germany, in the Cyberspace Division, as a Professor of Cyberwarfare Studies at the AIr War College and USAF Cyber College at Maxwell AFB and is currently the Deputy Director of the National Cyber Range Complex (NCRC) - Charleston Node. He is very interested in how geographic information science and technology (GIS&T) can be applied to the emerging field of Cyberspace both within and outside the government. There are two dimensions to Cyberattacks – collecting of intelligence from nations that are of interest to us, and realizing that others are constantly collecting on us.
Information is the only asset that is stolen by replication. As such, securing it is problematic because for it to be of any use it also needs to be available for access. In the wake of the September 11, 2001 attacks, the US government began instituting information protection policies aimed at increasing homeland security. The aim of these policies was to minimize the targets of opportunity that could be exploited by potential attackers using publicly available information they might obtain from authoritative public (federal, state and local) sources in planning attacks against the US homeland.
One of the outcomes of these policies is the “National Cybersecurity Strategy” that was released in March 2023. The DoD has stated that “The Department and the nation have vulnerabilities in cyberspace. Our reliance on cyberspace stands in stark contrast to the inadequacy of our cybersecurity – the security of the technologies that we use each day.” DoD strategy flows from both the National Cybersecurity Strategy and the National Defense Strategy.
There are thousands of networks, incalculable data assets freely in the open, and adversaries – individuals, groups, and nation-states, that can and will use our own information sources against us. It raises the question – how much information should a free society place in the open?
Required Readings
- "Mapping the Risks" is a Rand study complied in 2004. It attempts to evaluate the risks and rewards of having easily accessible Geospatial data available online for use by anyone. Although federal agencies produce and publicly disseminate geospatial information for a wide range of beneficial purposes, there also exists the risk that some types of geospatial information could be and has been exploited by terrorists. This is the challenge the federal agencies face in deciding which types of geospatial information should be publicly accessible, as well as whether and how to restrict new sensitive information as it becomes available.
The full study is available from The Rand Corporation Website [206].
NOTE: For this assignment, you need only read the Executive Summary.
- The Office of the President released the "National Cybersecurity Strategy" in March 2023. It has been an ever evolving document, the latest being the 2023 "National Cybersecurity Strategy [184]" [185].
Between 2004 and 2023, Cyberspace evolved into a mature operating domain. For many reasons, many of them political or driven by DOD component infighting, no final concrete policy existed before this and the debate to establish a separate CYBERCOM took years to finalize between the sister services within the DoD, with a final definition of cyberspace finally being imposed on the DoD by Gordon England in May 2008.
Readings can be accessed from the Lesson 10 Checklist [203].
You will compare and contrast these two publications that lay out some of the basics of Geo-based Cyberspace analysis and cyber map production.
As you read, do some critical thinking and ask yourself:
- What aspects of the application of GIS&T in the military and the intelligence community are really applications of geospatial intelligence?
- Given what you know of the application of geospatial intelligence to US national security activities, compare and contrast how the DoD intelligence community leverages GIS&T and the intelligence process.
- Given that GIS&T includes at least the four subfields of cartography, remote sensing, GIS, and GPS, consider the central role that mapping seems to play in cyber analysis. How might the DoD and the intelligence community better leverage the other components of GIS&T and geospatial intelligence?
Required Viewing
Video: The Cyber War Threat Has Been Grossly Exaggerated. [207] (1:38:00) (Transcript [208])

The debate still continues. After listening, offer a perspective of whether the debate affected your view.
- Which way did you vote at the beginning?
- Which way did you vote at the end?
- Offer your insights as to whether the debate is real or exaggerated.
Information Technology Infrastructure
Information technology infrastructure has changed in the last 10 years. Currently, an integration of geolocating technologies with communications infrastructures has made possible dynamic changes in Northern Africa and parts of the Middle East.
Let us examine a few facts concerning the integration of technologies in Africa over the last decade.
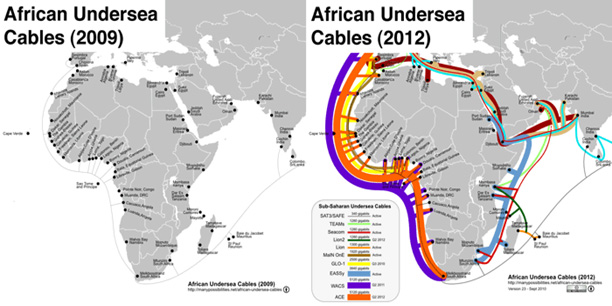
Low-cost, abundant, easily distributed information lowers transaction costs, which affects the nature of institutions and organizations. When internet connectivity was mostly carried on satellites it (and the transaction costs) was high. As these cables come online, the transactions costs are going to come down. Infrastructure increases in Africa will eventually lead to increases in information flow and associated increases in relational aspects between distant points. What could formerly be characterized as "Terra Incognita" is changing with increases in infrastructure.
Would the "Arab Spring" have been possible before 2009? The lack of infrastructure makes it doubtful. Once all the cables are in place, Africa's total bandwidth will increase from 6 terabytes/second (tbps) to well over 40tbps. Currently, there are over half a billion Africans connected to the global system through cell phones and the Internet, and this number is going to dramatically increase.
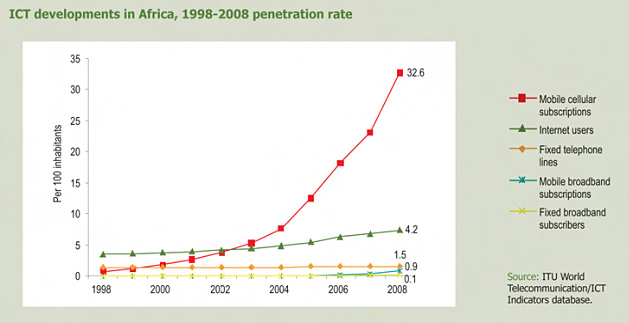
The graph above shows the continent-wide penetration rate of different Information-Communication technologies (ICTs). Notable here is the huge increase in wireless penetration - almost 33% continent-wide that does not require as much infrastructure as traditional landlines. This continent-wide picture does not paint a fully accurate picture. While the overall number is correct, the penetration rates in North Africa show a different story when reviewed separately. Too much variation is concealed in the overall continental rate but becomes apparent when examined more regionally. In the Mahgreb, the rates were almost twice as much as the continental average and increased steadily to over 100% in some places, meaning that some subscribers actually had more than 1 phone by 2010.
The former Director of National Intelligence (DNI), General James Clapper, hinted at the IC's interests in some of the aspects of intelligence collection in an interview in the December 2011 issue of Geospatial Intelligence Review,
"I see all kinds of benefits (from combining collection and analysis). There are a lot of examples that I can't cite because they are classified. But I will say that I think we will be better able to address an Arab Spring, for example, and better able to anticipate it and respond to it."
The richness of available open source data, generated either by social media or other sources, is too complex to accumulate and analyze using current approaches. Currently, analysts often use multiple sources of information in order to create actionable intelligence for a mission. The datasets are large in volume and are likely stored in multiple databases and multiple locations. This requires tailored queries into the systems to be prespecified, filtering significant amounts of data before an analyst has an opportunity to decide if it is important. This query-retrieve paradigm effectively removes the possibility of the "lucky find," because the analyst has to already know what they want to query. Looking forward, the datasets are becoming more connected and the transaction costs are decreasing. The volume of pseudo-humint available from social media is one result of the increase in this connectivity infrastructure, and the impacts are both unpredictable and unforeseen. At a minimum, it raises the following questions for our consideration:
- The tacit-explicit knowledge transformation underway is potentially making disconnected areas such as Africa less a "Terra-Incognita" than ever before. What will this mean in terms of the geo-strategic framework?
- How seriously is the IC reviewing the potentials of Web 2.0 enabled sources geospatially enabled with "Volunteer Geographic Information?"
- How might peer and near peer opponents make use of the models?
Emerging technologies also pose unique challenges and threats. ChatGPT [211], when queried about the threats in cyber to GeoInt replied:
"The dangers of cyberspace in the GeoInt (Geospatial Intelligence) environment are multifaceted and significant. They can be categorized into several key areas:
-
Cyber Espionage and Data Theft: In a GeoInt environment, where sensitive geospatial data is used, cyber espionage is a major threat. Unauthorized access to this data can lead to the theft of classified information, compromising national security and intelligence operations.
-
Cyberattacks on Critical Infrastructure: GeoInt often involves infrastructure critical to national security, like satellite communications, GPS systems, and other space-based assets. Cyberattacks on these systems can disrupt essential services, leading to significant strategic disadvantages.
-
Manipulation of Geospatial Data: The integrity of geospatial data is crucial. If this data is manipulated or altered, it can lead to incorrect intelligence assessments, affecting decision-making in critical situations such as military operations or disaster response.
-
Information Warfare: In the realm of GeoInt, information warfare, including the spread of misinformation and propaganda, can be facilitated through cyberspace. This can undermine trust in institutions and disrupt geopolitical stability.
-
Supply Chain Attacks: GeoInt systems often rely on a complex supply chain that includes software and hardware components from various sources. Cyberattacks targeting these supply chains can compromise the integrity of geospatial intelligence systems.
-
Insider Threats: The risk posed by insiders, such as employees or contractors with access to GeoInt systems, is significant. They might intentionally or unintentionally cause harm by leaking sensitive information or introducing vulnerabilities into the system.
-
Lack of Standardized Security Protocols: In the GeoInt environment, the lack of standardized cybersecurity protocols across different nations and organizations can create vulnerabilities. Disparate systems and practices can lead to gaps in security defenses.
-
Emerging Technologies: The rapid evolution of technology, including AI and quantum computing, presents new challenges in cybersecurity. These technologies can be used to create more sophisticated cyberattacks that are harder to detect and defend against.
-
Legal and Ethical Concerns: Navigating the legal and ethical aspects of cyber operations in GeoInt is complex, especially when it comes to cross-border data sharing and surveillance activities.
-
Resource Constraints: Finally, the challenge of allocating adequate resources (like skilled personnel and funding) to cybersecurity in the GeoInt sector cannot be overlooked. This includes the need for continuous training and updating of systems to counter evolving cyber threats.
Given these threats, it's crucial for organizations and nations involved in GeoInt to invest in robust cybersecurity measures, conduct regular risk assessments, and foster international cooperation to enhance collective cyber defense capabilities."
Reference:
CHAT GPT, response to “threats in cyber to GeoInt,” CHAPT GPT, Dec. 3, 2023.
10.8 Summary and Final Tasks
Summary
Completion of this lesson:
- introduced you to the basics of crime mapping and analysis, and contemplation of how geospatial intelligence applies to this field;
- introduced some questions about how geospatial intelligence applies to the area of international disaster response and humanitarian relief;
- introduced ideas concerning cyberspace and Geoint;
- completed the World Campus SEEQ survey;
- provided your feedback to the instructors on specific components of the course.
Final Tasks
Deliverable: Lesson 10 – GRADED Discussion Forum #4.
Return to Lesson 10 in Canvas. Look for the Lesson 10 - GRADED Discussion Forum (#4), where you will find the three topics for this assignment. You will at a minimum address two of the three topics. You may address all three topics if you wish. The minimum requirement is that each of you post one primary response to two of the three discussion topics: Crime Analysis, IHR, or Cyberspace. You must then comment on at least TWO of your classmates' posts. You must then provide a primary post on the course feedback question. (Five total posts - three primary posts and two comments.) There is no need to comment on the course feedback question.
Remember to analyze the questions to determine specified and implied requirements, explicitly demonstrate your higher order and critical thinking skills, show me you read the required readings, and that you did some research if required. I challenge you to try and see beyond your cultural filters (which are sometimes blinders) and view these issues from a higher level or different perspective.
Note: Please post your primary response to the questions by Sunday evening to allow time for everyone to post comments by Tuesday night.
Deliverable: World Campus Student Educational Experience Questionnaire (SEEQ) Survey.
Return to Canvas and look for the link to the World Campus SEEQ Survey, where you will access the survey. NOTE: Information in this survey is strictly confidential, and has NO impact whatsoever on course grades.
Before you close your books, double-check the Lesson 10 Checklist [203] to make sure you have completed all of the required activities for this lesson.
Looking Back
This concludes the course. It was a pleasure having you in this class, and thank you for all your hard work in completing this course. All of you have been very professional, and I have learned as much from you as I hope you have learned from the course.
Check the Grades to ensure you have credit for all your assignments. I will submit final grades to Penn State no later than 48 hours after the final day of class, and I will also email individually with your course grade. It will probably be a few weeks before the grades are officially posted in eLion (e.g., your transcript).
Do not forget to register for the next course. We wish you the best in the future and hope the knowledge and skills you gained from this course will contribute to your success.
Mark Corson, Greg Thomas, Mike Thomas, and Steve Handwerk
GEOG 882 Course Faculty